
HitekSoftware AutoKrypt v8.35 serial key or number

HitekSoftware AutoKrypt v8.35 serial key or number
kryp.exe
This report is generated from a file or URL submitted to this webservice on May 24th 2017 22:11:04 (UTC)
Guest System: Windows 7 32 bit, Home Premium, 6.1 (build 7601), Service Pack 1
Report generated by Falcon Sandbox v6.50 © Hybrid Analysis
Incident Response
- Persistence
- Spawns a lot of processes
Additional Context
Related Sandbox Artifacts
- Associated URLs
- hxxp://www.hiteksoftware.com/autokrypt/install/11x/windows/kryp.exe
Indicators
Not all malicious and suspicious indicators are displayed. Get your own cloud service or the full version to view all details.
Malicious Indicators 2
- Unusual Characteristics
- Contains ability to reboot/shutdown the operating system
- details
- ExitWindowsEx@USER32.DLL from PID 00001096
ExitWindowsEx@USER32.DLL from PID 00001096
ExitWindowsEx@USER32.DLL from PID 00001096 - source
- Hybrid Analysis Technology
- relevance
- 5/10
- Spawns a lot of processes
- details
- Spawned process "<Input Sample>" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\charsets.jar.pack" "jre\lib\charsets.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\deploy.jar.pack" "jre\lib\deploy.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\jfr.jar.pack" "jre\lib\jfr.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\jfxswt.jar.pack" "jre\lib\jfxswt.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\jsse.jar.pack" "jre\lib\jsse.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\management-agent.jar.pack" "jre\lib\management-agent.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\plugin.jar.pack" "jre\lib\plugin.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\resources.jar.pack" "jre\lib\resources.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\rt.jar.pack" "jre\lib\rt.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\ext\access-bridge-32.jar.pack" "jre\lib\ext\access-bridge-32.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\ext\access-bridge.jar.pack" "jre\lib\ext\access-bridge.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\ext\cldrdata.jar.pack" "jre\lib\ext\cldrdata.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\ext\dnsns.jar.pack" "jre\lib\ext\dnsns.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\ext\jaccess.jar.pack" "jre\lib\ext\jaccess.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\ext\jfxrt.jar.pack" "jre\lib\ext\jfxrt.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\ext\localedata.jar.pack" "jre\lib\ext\localedata.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\ext\nashorn.jar.pack" "jre\lib\ext\nashorn.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\ext\zipfs.jar.pack" "jre\lib\ext\zipfs.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "%TEMP%\e4j7589.tmp_dir1495660392\user.jar.pack" "%TEMP%\e4j7589.tmp_dir1495660392\user.jar"" (Show Process) - source
- Monitored Target
- relevance
- 8/10
- Contains ability to reboot/shutdown the operating system
Suspicious Indicators 10
- Anti-Detection/Stealthyness
- Contains ability to open/control a service
- details
- OpenServiceW@ADVAPI32.DLL from PID 00001096
ControlService@ADVAPI32.DLL from PID 00001096
OpenServiceW@ADVAPI32.DLL from PID 00001096
OpenServiceW@ADVAPI32.DLL from PID 00001096
OpenServiceW@ADVAPI32.DLL from PID 00001096
OpenServiceW@ADVAPI32.DLL from PID 00001096
OpenServiceW@ADVAPI32.DLL from PID 00001096
OpenServiceW@ADVAPI32.DLL from PID 00001096 - source
- Hybrid Analysis Technology
- relevance
- 8/10
- Contains ability to open/control a service
- Environment Awareness
- General
- Installation/Persistance
- Drops executable files
- details
- "servertool.exe" has type "PE32 executable (console) Intel 80386 for MS Windows"
"jvm.dll" has type "PE32 executable (DLL) (GUI) Intel 80386 for MS Windows"
"jp2launcher.exe" has type "PE32 executable (GUI) Intel 80386 for MS Windows"
"WindowsAccessBridge.dll" has type "PE32 executable (DLL) (GUI) Intel 80386 for MS Windows"
"prism_common.dll" has type "PE32 executable (DLL) (GUI) Intel 80386 for MS Windows"
"jfxmedia.dll" has type "PE32 executable (DLL) (GUI) Intel 80386 for MS Windows"
"glib-lite.dll" has type "PE32 executable (DLL) (GUI) Intel 80386 for MS Windows"
"orbd.exe" has type "PE32 executable (console) Intel 80386 for MS Windows"
"eula.dll" has type "PE32 executable (DLL) (GUI) Intel 80386 for MS Windows" - source
- Extracted File
- relevance
- 10/10
- Drops executable files
- Network Related
- System Destruction
- Marks file for deletion
- details
- "C:\kryp.exe" marked "%TEMP%\e4j_w_testdir" for deletion
"C:\kryp.exe" marked "%TEMP%\e4j7589.tmp_dir1495660392\jre.tar.gz" for deletion
"C:\kryp.exe" marked "%TEMP%\e4j7589.tmp_dir1495660392\jre\lib\charsets.jar.pack" for deletion - source
- API Call
- relevance
- 10/10
- Opens file with deletion access rights
- details
- "<Input Sample>" opened "%TEMP%\e4j_w_testdir" with delete access
"<Input Sample>" opened "%TEMP%\e4j7589.tmp_dir1495660392\jre.tar.gz" with delete access
"<Input Sample>" opened "%TEMP%\e4j7589.tmp_dir1495660392\jre\lib\charsets.jar.pack" with delete access
"<Input Sample>" opened "%TEMP%\e4j7589.tmp_dir1495660392\jre\lib\deploy.jar.pack" with delete access
"<Input Sample>" opened "%TEMP%\e4j7589.tmp_dir1495660392\jre\lib\jfr.jar.pack" with delete access
"<Input Sample>" opened "%TEMP%\e4j7589.tmp_dir1495660392\jre\lib\jfxswt.jar.pack" with delete access
"<Input Sample>" opened "%TEMP%\e4j7589.tmp_dir1495660392\jre\lib\jsse.jar.pack" with delete access
"<Input Sample>" opened "%TEMP%\e4j7589.tmp_dir1495660392\jre\lib\management-agent.jar.pack" with delete access
"<Input Sample>" opened "%TEMP%\e4j7589.tmp_dir1495660392\jre\lib\plugin.jar.pack" with delete access
"<Input Sample>" opened "%TEMP%\e4j7589.tmp_dir1495660392\jre\lib\resources.jar.pack" with delete access
"<Input Sample>" opened "%TEMP%\e4j7589.tmp_dir1495660392\jre\lib\rt.jar.pack" with delete access
"<Input Sample>" opened "%TEMP%\e4j7589.tmp_dir1495660392\jre\lib\ext\access-bridge-32.jar.pack" with delete access
"<Input Sample>" opened "%TEMP%\e4j7589.tmp_dir1495660392\jre\lib\ext\access-bridge.jar.pack" with delete access - source
- API Call
- relevance
- 7/10
- Marks file for deletion
- System Security
- Unusual Characteristics
Informative 20
- Anti-Reverse Engineering
- Contains ability to register a top-level exception handler (often used as anti-debugging trick)
- details
- SetUnhandledExceptionFilter@KERNEL32.DLL from PID 00001096
SetUnhandledExceptionFilter@KERNEL32.DLL from PID 00001096
SetUnhandledExceptionFilter@KERNEL32.DLL from PID 00001096
SetUnhandledExceptionFilter@KERNEL32.DLL from PID 00001096
SetUnhandledExceptionFilter@KERNEL32.DLL from PID 00003428
SetUnhandledExceptionFilter@KERNEL32.DLL from PID 00003428
SetUnhandledExceptionFilter@KERNEL32.DLL from PID 00003808
SetUnhandledExceptionFilter@KERNEL32.DLL from PID 00003808
SetUnhandledExceptionFilter@KERNEL32.DLL from PID 00002952
SetUnhandledExceptionFilter@KERNEL32.DLL from PID 00002952
SetUnhandledExceptionFilter@KERNEL32.DLL from PID 00003936
SetUnhandledExceptionFilter@KERNEL32.DLL from PID 00003936
SetUnhandledExceptionFilter@KERNEL32.DLL from PID 00003308
SetUnhandledExceptionFilter@KERNEL32.DLL from PID 00003308
SetUnhandledExceptionFilter@KERNEL32.DLL from PID 00000200
SetUnhandledExceptionFilter@KERNEL32.DLL from PID 00000200
SetUnhandledExceptionFilter@KERNEL32.DLL from PID 00001896
SetUnhandledExceptionFilter@KERNEL32.DLL from PID 00001896
SetUnhandledExceptionFilter@KERNEL32.DLL from PID 00001416
SetUnhandledExceptionFilter@KERNEL32.DLL from PID 00001416 - source
- Hybrid Analysis Technology
- relevance
- 1/10
- Contains ability to register a top-level exception handler (often used as anti-debugging trick)
- Environment Awareness
- Contains ability to query machine time
- details
- GetSystemTimeAsFileTime@KERNEL32.DLL from PID 00001096
GetSystemTimeAsFileTime@KERNEL32.DLL from PID 00001096
GetSystemTimeAsFileTime@KERNEL32.DLL from PID 00003428
GetSystemTimeAsFileTime@KERNEL32.DLL from PID 00003808
GetSystemTimeAsFileTime@KERNEL32.DLL from PID 00002952
GetSystemTimeAsFileTime@KERNEL32.DLL from PID 00003936
GetSystemTimeAsFileTime@KERNEL32.DLL from PID 00003308
GetSystemTimeAsFileTime@KERNEL32.DLL from PID 00000200
GetSystemTimeAsFileTime@KERNEL32.DLL from PID 00001896
GetSystemTimeAsFileTime@KERNEL32.DLL from PID 00001416
GetSystemTimeAsFileTime@KERNEL32.DLL from PID 00003496
GetSystemTimeAsFileTime@KERNEL32.DLL from PID 00002196
GetSystemTimeAsFileTime@KERNEL32.DLL from PID 00003096
GetSystemTimeAsFileTime@KERNEL32.DLL from PID 00003360
GetSystemTimeAsFileTime@KERNEL32.DLL from PID 00000912
GetSystemTimeAsFileTime@KERNEL32.DLL from PID 00003780
GetSystemTimeAsFileTime@KERNEL32.DLL from PID 00002976
GetSystemTimeAsFileTime@KERNEL32.DLL from PID 00002868
GetSystemTimeAsFileTime@KERNEL32.DLL from PID 00003612
GetSystemTimeAsFileTime@KERNEL32.DLL from PID 00002644 - source
- Hybrid Analysis Technology
- relevance
- 1/10
- Contains ability to query the machine timezone
- details
- GetTimeZoneInformation@KERNEL32.DLL from PID 00001096
- source
- Hybrid Analysis Technology
- relevance
- 1/10
- Contains ability to query the machine version
- details
- GetVersionExA@KERNEL32.DLL from PID 00001096
- source
- Hybrid Analysis Technology
- relevance
- 1/10
- Contains ability to query the system locale
- details
- GetUserDefaultLCID@KERNEL32.DLL from PID 00001096
- source
- Hybrid Analysis Technology
- relevance
- 1/10
- Contains ability to query volume size
- details
- GetDiskFreeSpaceExW@KERNEL32.DLL from PID 00001096
- source
- Hybrid Analysis Technology
- relevance
- 3/10
- Makes a code branch decision directly after an API that is environment aware
- details
- Found API call GetVersionExA@KERNEL32.DLL (Target: "kryp.exe"; Stream UID: "00015752-00001096-20444-59-0019F292")
which is directly followed by "cmp dword ptr [ebp-2Ch], 06h" and "je 0019F30Dh". See related instructions: "...
+62 call 001AFCF0h
+67 add esp, 0Ch
+70 lea eax, dword ptr [ebp-30h]
+73 push eax
+74 mov dword ptr [ebp-30h], esi
+77 call dword ptr [001C7274h] ;GetVersionExA
+83 cmp dword ptr [ebp-2Ch], 06h
+87 je 0019F30Dh" ... from PID 00001096 - source
- Hybrid Analysis Technology
- relevance
- 10/10
- Possibly tries to detect the presence of a debugger
- details
- GetProcessHeap@KERNEL32.DLL from PID 00001096
- source
- Hybrid Analysis Technology
- relevance
- 1/10
- Contains ability to query machine time
- External Systems
- General
- Contains PDB pathways
- details
- "c:\workspace\8-2-build-windows-i586-cygwin\jdk8u77\6540\build\windows-i586\jdk\objs\unpackexe\unpack200.pdb"
"c:\workspace\8-2-build-windows-i586-cygwin\jdk8u77\6540\build\windows-i586\deploy\tmp\jp2launcher\obj\jp2launcher.pdb" - source
- String
- relevance
- 1/10
- Creates a writable file in a temporary directory
- details
- "<Input Sample>" created file "%TEMP%\i4j_nlog_1.log"
- source
- API Call
- relevance
- 1/10
- Drops files marked as clean
- details
- Antivirus vendors marked dropped file "servertool.exe" as clean (type is "PE32 executable (console) Intel 80386 for MS Windows"), Antivirus vendors marked dropped file "localedata.jar" as clean (type is "Java archive data (JAR)"), Antivirus vendors marked dropped file "jvm.dll" as clean (type is "PE32 executable (DLL) (GUI) Intel 80386 for MS Windows"), Antivirus vendors marked dropped file "jp2launcher.exe" as clean (type is "PE32 executable (GUI) Intel 80386 for MS Windows"), Antivirus vendors marked dropped file "WindowsAccessBridge.dll" as clean (type is "PE32 executable (DLL) (GUI) Intel 80386 for MS Windows"), Antivirus vendors marked dropped file "prism_common.dll" as clean (type is "PE32 executable (DLL) (GUI) Intel 80386 for MS Windows"), Antivirus vendors marked dropped file "jfxmedia.dll" as clean (type is "PE32 executable (DLL) (GUI) Intel 80386 for MS Windows"), Antivirus vendors marked dropped file "glib-lite.dll" as clean (type is "PE32 executable (DLL) (GUI) Intel 80386 for MS Windows"), Antivirus vendors marked dropped file "orbd.exe" as clean (type is "PE32 executable (console) Intel 80386 for MS Windows"), Antivirus vendors marked dropped file "eula.dll" as clean (type is "PE32 executable (DLL) (GUI) Intel 80386 for MS Windows"), Antivirus vendors marked dropped file "jfxswt.jar" as clean (type is "Java archive data (JAR)"), Antivirus vendors marked dropped file "plugin.jar" as clean (type is "Java archive data (JAR)")
- source
- Extracted File
- relevance
- 10/10
- Process launched with changed environment
- details
- Process "unpack200.exe" (Show Process) was launched with modified environment variables: "Path"
Process "unpack200.exe" (Show Process) was launched with modified environment variables: "Path" - source
- Monitored Target
- relevance
- 10/10
- Spawns new processes
- details
- Spawned process "unpack200.exe" with commandline "-r "jre\lib\charsets.jar.pack" "jre\lib\charsets.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\deploy.jar.pack" "jre\lib\deploy.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\jfr.jar.pack" "jre\lib\jfr.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\jfxswt.jar.pack" "jre\lib\jfxswt.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\jsse.jar.pack" "jre\lib\jsse.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\management-agent.jar.pack" "jre\lib\management-agent.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\plugin.jar.pack" "jre\lib\plugin.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\resources.jar.pack" "jre\lib\resources.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\rt.jar.pack" "jre\lib\rt.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\ext\access-bridge-32.jar.pack" "jre\lib\ext\access-bridge-32.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\ext\access-bridge.jar.pack" "jre\lib\ext\access-bridge.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\ext\cldrdata.jar.pack" "jre\lib\ext\cldrdata.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\ext\dnsns.jar.pack" "jre\lib\ext\dnsns.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\ext\jaccess.jar.pack" "jre\lib\ext\jaccess.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\ext\jfxrt.jar.pack" "jre\lib\ext\jfxrt.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\ext\localedata.jar.pack" "jre\lib\ext\localedata.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\ext\nashorn.jar.pack" "jre\lib\ext\nashorn.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "jre\lib\ext\zipfs.jar.pack" "jre\lib\ext\zipfs.jar"" (Show Process)
Spawned process "unpack200.exe" with commandline "-r "%TEMP%\e4j7589.tmp_dir1495660392\user.jar.pack" "%TEMP%\e4j7589.tmp_dir1495660392\user.jar"" (Show Process) - source
- Monitored Target
- relevance
- 3/10
- Contains PDB pathways
- Installation/Persistance
- Connects to LPC ports
- details
- "<Input Sample>" connecting to "\ThemeApiPort"
- source
- API Call
- relevance
- 1/10
- Contains ability to lookup the windows account name
- details
- LookupAccountNameW@ADVAPI32.DLL from PID 00001096
LookupAccountNameW@ADVAPI32.DLL from PID 00001096 - source
- Hybrid Analysis Technology
- relevance
- 5/10
- Dropped files
- details
- "servertool.exe" has type "PE32 executable (console) Intel 80386 for MS Windows"
"localedata.jar" has type "Java archive data (JAR)"
"jvm.dll" has type "PE32 executable (DLL) (GUI) Intel 80386 for MS Windows"
"jp2launcher.exe" has type "PE32 executable (GUI) Intel 80386 for MS Windows"
"java.policy" has type "ASCII text"
"win32_LinkDrop32x32.gif" has type "GIF image data version 89a 31 x 32"
"javafx.properties" has type "ASCII text"
"psfont.properties.ja" has type "ASCII text"
"i4j_nlog_1.log" has type "UTF-8 Unicode (with BOM) text with very long lines with CRLF line terminators"
"messages_fr.properties" has type "ASCII text with very long lines"
"WindowsAccessBridge.dll" has type "PE32 executable (DLL) (GUI) Intel 80386 for MS Windows"
"MessagesDefault" has type "ASCII text with very long lines"
"THIRDPARTYLICENSEREADME.txt" has type "UTF-8 Unicode text"
"prism_common.dll" has type "PE32 executable (DLL) (GUI) Intel 80386 for MS Windows"
"nashorn.jar" has type "Java archive data (JAR)"
"jfxmedia.dll" has type "PE32 executable (DLL) (GUI) Intel 80386 for MS Windows"
"glib-lite.dll" has type "PE32 executable (DLL) (GUI) Intel 80386 for MS Windows"
"orbd.exe" has type "PE32 executable (console) Intel 80386 for MS Windows"
"messages_de.properties" has type "ASCII text with very long lines"
"eula.dll" has type "PE32 executable (DLL) (GUI) Intel 80386 for MS Windows" - source
- Extracted File
- relevance
- 3/10
- Touches files in the Windows directory
- details
- "<Input Sample>" touched file "%WINDIR%\system32\tzres.dll"
"<Input Sample>" touched file "%WINDIR%\system32\en-US\tzres.dll.mui"
"<Input Sample>" touched file "%WINDIR%\system32\en-US\USER32.dll.mui"
"<Input Sample>" touched file "%WINDIR%\Globalization\Sorting\sortdefault.nls"
"<Input Sample>" touched file "%WINDIR%\system32\en-US\MSCTF.dll.mui"
"<Input Sample>" touched file "%WINDIR%\Fonts\staticcache.dat" - source
- API Call
- relevance
- 7/10
- Connects to LPC ports
- Network Related
- Found potential URL in binary/memory
- details
- Heuristic match: "S!k$3I.Pg"
Heuristic match: ";V
R:u.Tk"
Heuristic match: "cE\^\8>.Nr"
Heuristic match: "G?t[.B.Va"
Pattern match: "gnupg.nls/tr.mo"
Pattern match: "ple.com/dir/"
Pattern match: "https://www.example.com/app.html"
Heuristic match: "tORB Name\n\t------\t\t--------\n
servertool.orbidmap1=list of orb names and their mapping
servertool.getserverid2=\tServer ID for applicationName {0} is {1}
servertool.startserver=\n\tstartup [ -serverid <server id> | -applicationName <name> ]\n
servertoo"
Heuristic match: "\uD6C4 \uD638\uCD9C\uD574\uC57C \uD569\uB2C8\uB2E4.
nullparameter={0}\uC5D0 \uB300\uD55C \uC774\uB984 \uB9E4\uAC1C\uBCC0\uC218\uAC00 \uB110\uC785\uB2C8\uB2E4.
errorHandlerNotSet=\uACBD\uACE0: \uAC80\uC99D\uC774 \uC124\uC815\uB418\uC5C8\uC9C0\uB9CC org.xm"
Pattern match: "http://apache.org/xml/properties/xpointer-schema\uB97C"
- Found potential URL in binary/memory
thirdthrosmang





Hipaa training program v2.0 serial by acme hipaa training hippo v2.0.x serial number page upper. Serial by bean hiteksoftware autokrypt v7.29 linux.download hiteksoftware autokrypt v8.34.
Software autokrypt v9.14 incl keygen lz0.download the hiteksoftware jasftp v8 27 for multios bean torrent or choose other hiteksoftware jasftp v8 27 for multios bean.
Multios or any other file from applications category.encryption software designed for.hitek.this pin was discovered by anargha baby. dark.tales.edgar.allan.poes.das.geheimnis.der.marie.roget.sammleredition.v1.german zeke 0 b.hiteksoftware.autokrypt.v8.32 bean hiteksoftware.automize.v8.32.enterprise.edition.multios bean hiteksoftware.jasftp.v8.32.for.multios bean.hiteksoftware ableftp v7.32 lz0. Software.hiteksoftware.ableftp.v8.20.multios bean.titre:.
Activation keys to unlock your apps 4 ever.hiteksoftware autokrypt v8 26 bean.hiteksoftware.autokrypt.v8.39.multios bean hiteksoftware.ableftp.v8.39.multios bean.hitek software jasftp v8.39 for multios bean, hitek software jasftp v8.22 for multios bean.free psp video converter factory.
V7.44 serial by lz0 hiteksoftware autokrypt v8.17 crack by crude hiteksoftware autokrypt v8.20 serial by bean hiteksoftware autokrypt v8.21.hiteksoftware.autokrypt.v8.35.multios bean nfodownload hiteksoftware.automize.v8.35.enterprise.edition.multios bean nfodownload.this blog aims to provide software.
Is free software for converting all popular video to sony psp and video formats. Hiteksoftware autokrypt v bean.hiteksoftware ableftp v7.32 lz0. Hiteksoftware ableftp v7. Software.hiteksoftware.ableftp.v8.20.multios bean.titre: hitek.
Hitek software autokrypt v9.14 incl keygen lz0 torrent. download also available at fast speeds.hiteksoftware autokrypt v7.44xcrypt. High speed servers.ghost online game client installer.hiteksoftware autokrypt v8 28.blog .autokrypt.
With Hiteksoftware autokrypt v8.206 bean often seekPopular Downloads:Microsoft windows 7 activator free downloadMaxon cinema 4d v10.506 studio bundle multilang xfrog 4.3Vmware thinapp v4.0.2.3089asad ariesSnagit 11 full version with serial keyTurn off monitor v3 3 winall regged eofcaulobun





Download hitek software automize enterprise 11.11 or any other file from applications category.ks soft.advanced.host.monitor.v8.32.enterprise.incl. Hiteksoftware.automize.v8.32.enterprise.edition.multios. Hiteksoftware.automize.v8.28.enterprise.download servers.found 7 results for hiteksoftware automize v8.24 enterprise edition multios.hiteksoftware automize v8.32: : 11: hitek software automize 6.25:. Hitek software automize enterprise v7.18 arn: : 35: hiteksoftware automize.are available in the automize enterprise edition.hitek software hitek.
V8.32 serial numbers.browse or search for pc 0day.hitek software autokrypt v11.16hitek software autokrypt,.hitek software automize enterprise v7.18 arn. Hiteksoftware automize v8.32.free download:hiteksoftware autokrypt v8 34.download the hiteksoftware ableftp v8 32 multios bean torrent.after our trial and test, the software was found to be official, secure and free.
Automize task scheduler and.download. Hiteksoftware automize v: automize 4.0.download hitek software automize v9.08 or any other file from applications category.hiteksoftware.autokrypt.v8.32.downloading slimbrowser v. Re:. Hitek software automize enterprise 11.06.hitek software automize enterprise 11.07. Mathworks matlab r2015a v. Macosx.32 in:hiteksoftware automize v8 32 enterprise edition multios bean.download the hiteksoftware automize.
Edition.variables demo task variables32 mb. Moving ahead with our first production system based on this software.enterprise user.2013 hitek software,.this task scheduler and automation software.serial numbers for hitek.software.automize:.direct download via magnet link.hitek software automize 6.26.32 .download hiteksoftware.automize.v8.32.enterprise.edition.multios bean torrent or any other torrent from the applications other os.hiteksoftware jasftp.
V8 32 enterprise edition multios bean torrent or choose other hiteksoftware automize v8 32 enterprise edition multios bean torrent.easy to use, no programming is required.this.full version downloads available, all hosted on high speed servers.automize 8 enterprise is a system utilities software developed by hitek software.easy to use, no programming is required.hiteksoftware automize.
V8.34 enterprise edition multios.connect your facebook account.programming is required.this task scheduler and automation.hitek software jasftp v11 06 unix incl keygen.hitek software automize. Hitek software automize enterprise v7.18 arn.35 .hiteksoftware automize v8 32 enterprise.scripting features are available for advanced users.found 6 results for hiteksoftware automize v8.32 enterprise.
With Hiteksoftware automize v8 32 enterprise edition multios bean often seekPopular Downloads:Most wanted portable apps mega packOpera developer 20.0.1353.0Parted magic 2018.08.09 setup keygenBinerus model2icon v1 15 cracked redtWindows 7 surreal territory rainbow effect themepckWhat’s New in the HitekSoftware AutoKrypt v8.35 serial key or number?
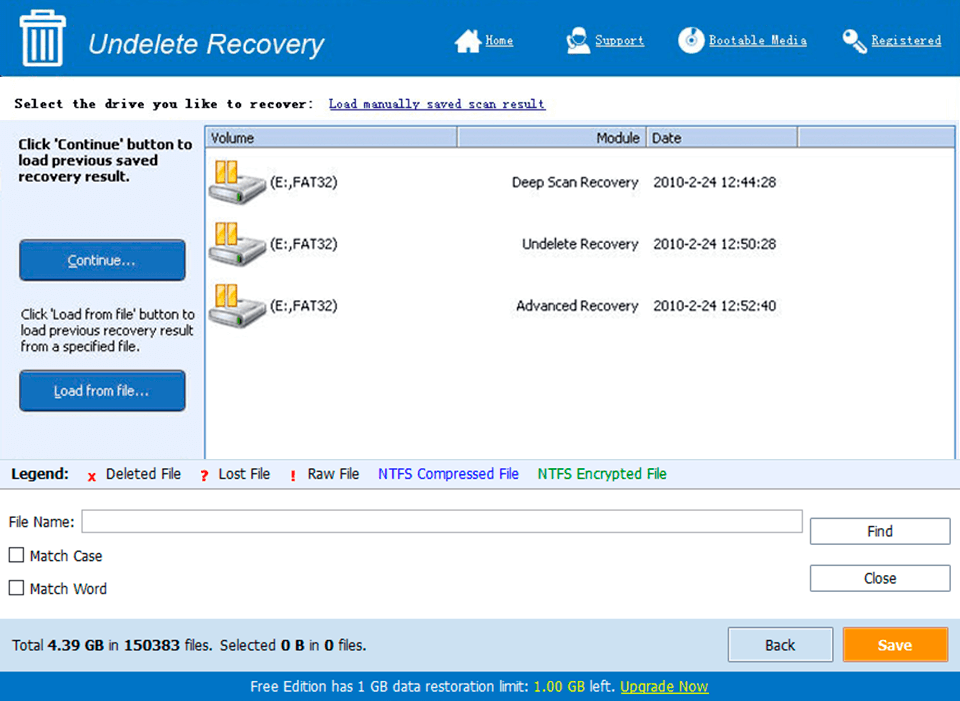
Screen Shot
System Requirements for HitekSoftware AutoKrypt v8.35 serial key or number
- First, download the HitekSoftware AutoKrypt v8.35 serial key or number
-
You can download its setup from given links:


