
Adobe CS5 Master key BY TEAM RED HOT serial key or number
Adobe CS5 Master key BY TEAM RED HOT serial key or number
Self Help Graphic Media
| Operating System | For Windows |
| Programming Language | Java |
| Free Required RAM | 1 GB |
| Support | 24/7 (Live Rep) |
| Type Of Output | Computer Generated |
| Type Of Graphics | 2D |
ADOBE MASTER COLLECTION by SELF HELP GRAPHIC MEDIAPrice: FREE manicapital.comlation service available through Team viewer All these 20 software are included in this adobe master collection. Adobe Flash, Adobe Flash video encoder, Adobe Flash Player, Adobe PhotoshopAdobe Fireworks, Adobe Illustrator, Adobe premier proAdobe premier pro third party content Adobe InDesign,Adobe SoundboothAdobe After EffectsAdobe Contribute Cs3Adobe DreamweaverAdobe Encore CS3Adobe Encore CS3 CodecsAdobe Soundbooth CS3Adobe Soundbooth CodecsAdobe version Cue CS3 serverAcrobat reader 8,Acrobat professional
Self Help Graphic MediaHuge Collection Of Video Tutorials On Any manicapital.comme support and upgrade will be available once you buy our productcontact us
View Complete Details
| Operating System | For Windows |
| Programming Language | Java |
| Free Required RAM | 1 GB |
| Support | 24/7 (Live Rep) |
| Type Of Graphics | 2D |
| Type Of Output | Computer Generated |
ADOBE MASTER COLLECTION by SELF HELP GRAPHIC MEDIAPrice: FREE manicapital.comlation service available through Team viewer All these 20 software are included in this adobe master collection. Adobe Flash, Adobe Flash video encoder, Adobe Flash Player, Adobe PhotoshopAdobe Fireworks, Adobe Illustrator, Adobe premier proAdobe premier pro third party content Adobe InDesign,Adobe SoundboothAdobe After EffectsAdobe Contribute Cs3Adobe DreamweaverAdobe Encore CS3Adobe Encore CS3 CodecsAdobe Soundbooth CS3Adobe Soundbooth CodecsAdobe version Cue CS3 serverAcrobat reader 8,Acrobat professional
Self Help Graphic MediaHuge Collection Of Video Tutorials On Any manicapital.comme support and upgrade will be available once you buy our productcontact us
View Complete Details
| Operating System | For Windows |
| Programming Language | Java |
| Free Required RAM | 1 GB |
| Support | 24/7 (Live Rep) |
| Type Of Output | Computer Generated |
| Type Of Graphics | 2D |
ADOBE MASTER COLLECTION by SELF HELP GRAPHIC MEDIAPrice: FREE manicapital.comlation service available through Team viewer All these 20 software are included in this adobe master collection. Adobe Flash, Adobe Flash video encoder, Adobe Flash Player, Adobe PhotoshopAdobe Fireworks, Adobe Illustrator, Adobe premier proAdobe premier pro third party content Adobe InDesign,Adobe SoundboothAdobe After EffectsAdobe Contribute Cs3Adobe DreamweaverAdobe Encore CS3Adobe Encore CS3 CodecsAdobe Soundbooth CS3Adobe Soundbooth CodecsAdobe version Cue CS3 serverAcrobat reader 8,Acrobat professional
Self Help Graphic MediaHuge Collection Of Video Tutorials On Any manicapital.comme support and upgrade will be available once you buy our productcontact us
View Complete Details
| Brand | Illustrator |
| Operating System | For Windows |
| Type | CC |
| Training Duration | Monthly |
| Storage | 1 GB |
course detailsDuration : HoursPrice : Rs.
This course includes:
94 Videos (12 hours of total playtime)
Interactive quizzes testing what you learnt in each chapter
Downloadable working files
Course content updated with the latest CC new features
All future updates to Illustrator will be included in this course for no extra payment
Estimated finish time: 25 hours (including finishing all exercises and quizzes)
Preparation guide for the official Adobe Certified Associate exam: Graphic Design & Illustration using Adobe Illustrator
Completion certificate upon finishing the entire course
Who will find it useful:
Perfect for anyone looking to start or develop their career in the creative industry.
Complete beginners will be able to master the software from the very beginning to the most advanced features.
Self-taught users and existing professionals can use the course to take their skills and knowledge to the next level, refine their workflows and learn to do everything the right way!
Existing and more experienced users of Illustrator may also discover hidden gems and workflows or catch up with all the new features released in CC
course contentsSection 1Introduction
1. Why learn Illustrator?2. How to Study?3. Getting an Adobe Certification4. Changes to User Interface in CC Exercise Files
Section 2 Basics6. Illustrator Documents7. Artboards8. Updated Artboards (New in CC )9. Navigation Working with Vectors User Interface Properties panel (New in CC ) Settings
Section 3 Working with Objects Basic Shapes Transformations Combining Shapes Selection Techniques Organising Objects Aligning and Distributing Objects Working Precisely Exercises
Section 4 Appearance of Objects Stroke settings Swatches Gradients Appearance panel Effects Exercises
Section 5 Drawing Basic Drawing Tools Drawing Exercise Coloring Drawing assistance tools Draw Inside Pen Tool Pen Tool exercise Pen Tool alternatives Curvature Tool (New in CC ) Distort and Transform tools Symmetrical drawing Concentric drawing techniques Manual tracing exercise
Section 6 Brushes Calligraphic Brushes Scatter Brushes Art Brushes Bristle Brushes Pattern Brushes Image Brushes
Section 7 Images Working with Images Preparing simple images for tracing Preparing complex images for tracing Image Trace Improving and Colouring traced images
Section 8 Type Character formatting Paragraph formatting Using Text styles Fonts Variable and SVG Fonts (New in CC ) Touch Type Type on a Path Type and Shapes Warp Text 3D Type Create Outlines from Text Image within Text Text Wrap Type Exercise
Section 9 Advanced Techniques Introduction to Masking Clipping Mask Opacity Mask Masking exercise Recolor Artwork Live Paint Bucket Envelope Distort Puppet Warp (New in CC ) Symbols Symbol Tools Graphs Blending Objects Creating Patterns Refining Pattern Design Gradient Mesh Perspective Drawing
Section 10 Export and Integration Saving work for Print Saving work for Web Export for Screens Adobe Apps Integration with Bridge CC Libraries Archiving Projects
Section 11 CC New Features Freeform Gradients Global Edit Enhanced visual font browsing User Interface Improvements Viewing Improvements
Section 12 Conclusion
View Complete Details
| Training Duration | 1 Month |
| Course Mode | Online |
| Mode of service | Online |
| Operating System | For Window |
Are you an Applied/Fine Art Student? Fashion Design Student? A photographer or Photography Student? A DTP operator? Art Director? Visualizer in the Ad agency? Artist? or do you want to make the career in the Creative field? If your answer is yes to any one of these questions, then we give you guarantee that it is very useful to you.
This DVD course will teach you Photoshop Like a Pro. It starts from very basics and gradually takes you to advance options. The author of this course is having experience of over 20 Years in the field of Advertising and Design.
Our Product Is Directly Proportional To Your Success. Whatever you learn from our DVDs will show the sparkling colors in your work, no matter if you work in a Multinational Advertising Agency or for a small design house, or in a small printing press, Remember this tutorial is a commando training of Photoshop. Your agency or clients will see the lightning fast speed and sense in your designing. It will multiply your investment by s in future. It is pure knowledge - and it will pay off. Its great investment in yourself.
If you have any query then Contact Us-
Additional Information:
- Item Code: phtpdvd02
- Pay Mode Terms: T/T (Bank Transfer)
View Complete Details
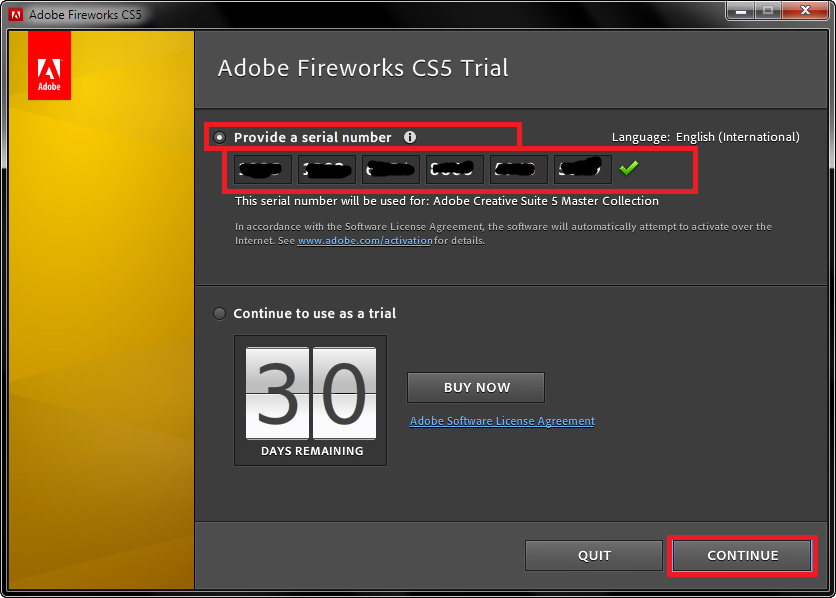
Adobe CS5 Master key BY TEAM RED HOT Serial number
The serial number for Adobe is available
This release was created for you, eager to use Adobe CS5 Master key BY TEAM RED HOT full and without limitations. Our intentions are not to harm Adobe software company but to give the possibility to those who can not pay for any piece of software out there. This should be your intention too, as a user, to fully evaluate Adobe CS5 Master key BY TEAM RED HOT without restrictions and then decide.
If you are keeping the software and want to use it longer than its trial time, we strongly encourage you purchasing the license key from Adobe official website. Our releases are to prove that we can! Nothing can stop us, we keep fighting for freedom despite all the difficulties we face each day.
Last but not less important is your own contribution to our cause. You should consider to submit your own serial numbers or share other files with the community just as someone else helped you with Adobe CS5 Master key BY TEAM RED HOT serial number. Sharing is caring and that is the only way to keep our scene, our community alive.
TrueCrypt
| Developer(s) | TrueCrypt Foundation |
|---|---|
| Initial release | February&#;; 16&#;years ago&#;()[1] |
| Final release | / May&#;28, ; 6&#;years ago&#;()[2] |
| Written in | C, C++, Assembly[3] |
| Operating system | Windows, macOS, Linux[3] |
| Size | MB |
| Available in | 38 languages[4] |
| Type | Disk encryption software |
| License | TrueCrypt License (source-availablefreeware) |
| Website | manicapital.com&#; |
TrueCrypt is a discontinued source-availablefreewareutility used for on-the-fly encryption (OTFE). It can create a virtual encrypted disk within a file, or encrypt a partition or the whole storage device (pre-boot authentication).
On 28 May , the TrueCrypt website announced that the project was no longer maintained and recommended users find alternative solutions. Though development of TrueCrypt has ceased, an independent audit of TrueCrypt (published in March ) has concluded that no significant flaws are present.[5]
History[edit]
TrueCrypt was initially released as version in February , based on E4M (Encryption for the Masses). Several versions and many additional minor releases have been made since then, with the most current version being a.[1]
E4M and SecurStar dispute[edit]
Original release of TrueCrypt was made by anonymous developers called "the TrueCrypt Team".[6] Shortly after version was released in , the TrueCrypt Team reported receiving email from Wilfried Hafner, manager of SecurStar, a computer security company.[7] According to the TrueCrypt Team, Hafner claimed in the email that the acknowledged author of E4M, developer Paul Le Roux, had stolen the source code from SecurStar as an employee.[7] It was further stated that Le Roux illegally distributed E4M, and authored an illegal license permitting anyone to base derivative work on the code and distribute it freely. Hafner alleges all versions of E4M always belonged only to SecurStar, and Le Roux did not have any right to release it under such a license.[7]
This led the TrueCrypt Team to immediately stop developing and distributing TrueCrypt, which they announced online through usenet.[7] TrueCrypt Team member David Tesařík stated that Le Roux informed the team that there was a legal dispute between himself and SecurStar, and that he received legal advisement not to comment on any issues of the case. Tesařík concluded that should the TrueCrypt Team continue distributing TrueCrypt, Le Roux may ultimately be held liable and be forced to pay consequent damages to SecurStar. To continue in good faith, he said, the team would need to verify the validity of the E4M license. However, because of Le Roux's need to remain silent on the matter, he was unable to confirm or deny its legitimacy, keeping TrueCrypt development in limbo.[7][8]
Thereafter, would-be visitors reported trouble accessing the TrueCrypt website, and 3rd party mirrors appeared online making the source code and installer continually available, outside of official sanction by the TrueCrypt Team.[9][10]
In the FAQ section of its website, SecurStar maintains its claims of ownership over both E4M and Scramdisk, another free encryption program. The company states that with those products, SecurStar "had a long tradition of open source software", but that "competitors had nothing better to do but to steal our source code", causing the company to make its products closed-source, forcing potential customers to place a substantial order and sign a non-disclosure agreement before being allowed to review the code for security.[11]
Le Roux himself has denied developing TrueCrypt in a court hearing in March , in which he also confirmed he had written E4M.[12]
Version [edit]
Months later on 7 June , TrueCrypt was released.[1] The new version contained a different digital signature from that of the original TrueCrypt Team, with the developers now being referred to as "the TrueCrypt Foundation." The software license was also changed to the open sourceGNU General Public License (GPL). However, given the wide range of components with differing licenses making up the software, and the contested nature of the legality of the program's release, a few weeks later on 21 June, version was released under the original E4M license to avoid potential problems relating to the GPL license.[1][13]
Version a of the software was released on 1 October on sub-domain.[1] By May , the original TrueCrypt website returned and redirected visitors to .
End of life announcement[edit]
On 28 May , the TrueCrypt official website, , began redirecting visitors to with a HTTP "Moved Permanently" status, which warned that the software may contain unfixed security issues, and that development of TrueCrypt was ended in May , following Windows XP's end of support. The message noted that more recent versions of Windows have built-in support for disk encryption using BitLocker, and that Linux and OS X had similar built-in solutions, which the message states renders TrueCrypt unnecessary. The page recommends any data encrypted by TrueCrypt be migrated to other encryption setups and offered instructions on moving to BitLocker. The SourceForge project page for the software at was updated to display the same initial message, and the status was changed to "inactive."[14] The page also announced a new software version, , which only allows decryption.
Initially, the authenticity of the announcement and new software was questioned.[15][16][17] Multiple theories attempting to explain the reason behind the announcement arose throughout the tech community.[18][19][3]
Shortly after the end of life announcement of TrueCrypt, Gibson Research Corporation posted an announcement titled "Yes TrueCrypt is still safe to use" and a Final Release Repository to host the last official non-crippled version a of TrueCrypt.[3]
Operating systems[edit]
TrueCrypt supports Windows, OS X and Linux operating systems.[20] Both bit and bit versions of these operating systems are supported, except for Windows IA (not supported) and Mac OS X Snow Leopard (runs as a bit process).[20] The version for Windows 7, Windows Vista, and Windows XP can encrypt the boot partition or entire boot drive.[21]
Independent implementations[edit]
There is an independent, compatible[22][23] implementation, tcplay, for DragonFly BSD[22] and Linux.[23][24]
The Dm-crypt module included in default Linux kernel supports a TrueCrypt target called "tcw" since Linux version [25][26][27]
Encryption scheme[edit]
Algorithms[edit]
Individual ciphers supported by TrueCrypt are AES, Serpent, and Twofish. Additionally, five different combinations of cascaded algorithms are available: AES-Twofish, AES-Twofish-Serpent, Serpent-AES, Serpent-Twofish-AES and Twofish-Serpent.[28] The cryptographic hash functions available for use in TrueCrypt are RIPEMD, SHA, and Whirlpool.[29]
Modes of operation[edit]
TrueCrypt currently uses the XTSmode of operation.[30] Prior to this, TrueCrypt used LRW mode in versions through a, and CBC mode in versions and earlier.[1] XTS mode is thought to be more secure than LRW mode, which in turn is more secure than CBC mode.[31]
Although new volumes can only be created in XTS mode, TrueCrypt is backward compatible with older volumes using LRW mode and CBC mode.[1] Later versions produce a security warning when mounting CBC mode volumes and recommend that they be replaced with new volumes in XTS mode.
Keys[edit]
The header key and the secondary header key (XTS mode) are generated using PBKDF2 with a bitsalt and or iterations, depending on the underlying hash function used.[32]
Plausible deniability[edit]
TrueCrypt supports a concept called plausible deniability,[33] by allowing a single "hidden volume" to be created within another volume.[34] In addition, the Windows versions of TrueCrypt have the ability to create and run a hidden encrypted operating system whose existence may be denied.[35]
The TrueCrypt documentation lists many ways in which TrueCrypt's hidden volume deniability features may be compromised (e.g. by third party software which may leak information through temporary files, thumbnails, etc., to unencrypted disks) and possible ways to avoid this.[36] In a paper published in and focused on the then latest version (va) and its plausible deniability, a team of security researchers led by Bruce Schneier states that Windows Vista, Microsoft Word, Google Desktop, and others store information on unencrypted disks, which might compromise TrueCrypt's plausible deniability. The study suggested the addition of a hidden operating system functionality; this feature was added in TrueCrypt When a hidden operating system is running, TrueCrypt also makes local unencrypted filesystems and non-hidden TrueCrypt volumes read-only to prevent data leaks.[35] The security of TrueCrypt's implementation of this feature was not evaluated because the first version of TrueCrypt with this option had only recently been released.[37]
There was a functional evaluation of the deniability of hidden volumes in an earlier version of TrueCrypt by Schneier et al. that found security leaks.[38]
Identifying TrueCrypt volumes[edit]
When analyzed, TrueCrypt volumes appear to have no header and contain random data.[39] TrueCrypt volumes have sizes that are multiples of due to the block size of the cipher mode[30] and key data is either bytes stored separately in the case of system encryption or two &#;kB headers for non-system containers.[40] Forensics tools may use these properties of file size, apparent lack of a header, and randomness tests to attempt to identify TrueCrypt volumes.[41] Although these features give reason to suspect a file to be a TrueCrypt volume, there are, however, some programs which exist for the purpose of securely erasing files by employing a method of overwriting file contents, and free disk space, with purely random data (i.e. "shred" & "scrub"[42]), thereby creating reasonable doubt to counter pointed accusations declaring a file, made of statistically random data, to be a TrueCrypt file.[33][43]
If a system drive, or a partition on it, has been encrypted with TrueCrypt, then only the data on that partition is deniable. When the TrueCrypt boot loader replaces the normal boot loader, an offline analysis of the drive can positively determine that a TrueCrypt boot loader is present and so lead to the logical inference that a TrueCrypt partition is also present. Even though there are features to obfuscate its purpose (i.e. displaying a BIOS-like message to misdirect an observer such as, "Non-system disk" or "disk error"), these reduce the functionality of the TrueCrypt boot loader and do not hide the content of the TrueCrypt boot loader from offline analysis.[44] Here again, the use of a hidden operating system is the suggested method for retaining deniability.[35]
Performance[edit]
TrueCrypt supports parallelized[45] encryption for multi-core systems and, under Microsoft Windows, pipelined read/write operations (a form of asynchronous processing)[45] to reduce the performance hit of encryption and decryption. On newer processors supporting the AES-NI instruction set, TrueCrypt supports hardware-accelerated AES to further improve performance.[45] The performance impact of disk encryption is especially noticeable on operations which would normally use direct memory access (DMA), as all data must pass through the CPU for decryption, rather than being copied directly from disk to RAM.
In a test carried out by Tom's Hardware, although TrueCrypt is slower compared to an unencrypted disk, the overhead of real-time encryption was found to be similar regardless of whether mid-range or state-of-the-art hardware is in use, and this impact was "quite acceptable".[46] In another article the performance cost was found to be unnoticeable when working with "popular desktop applications in a reasonable manner", but it was noted that "power users will complain".[47]
Incompatibility with FlexNet Publisher and SafeCast[edit]
Installing third-party software which uses FlexNet Publisher or SafeCast (which are used for preventing software piracy on products by Adobe such as Adobe Photoshop) can damage the TrueCrypt bootloader on Windows partitions/drives encrypted by TrueCrypt and render the drive unbootable.[48] This is caused by the inappropriate design of FlexNet Publisher writing to the first drive track and overwriting whatever non-Windows bootloader exists there.[49]
Security concerns[edit]
TrueCrypt is vulnerable to various known attacks which are also present in other software-based disk encryption software such as BitLocker. To prevent those, the documentation distributed with TrueCrypt requires users to follow various security precautions.[50] Some of those attacks are detailed below.
Encryption keys stored in memory[edit]
TrueCrypt stores its keys in RAM; on an ordinary personal computer the DRAM will maintain its contents for several seconds after power is cut (or longer if the temperature is lowered). Even if there is some degradation in the memory contents, various algorithms can intelligently recover the keys. This method, known as a cold boot attack (which would apply in particular to a notebook computer obtained while in power-on, suspended, or screen-locked mode), has been successfully used to attack a file system protected by TrueCrypt.[51]
Physical security[edit]
TrueCrypt documentation states that TrueCrypt is unable to secure data on a computer if an attacker physically accessed it and TrueCrypt is used on the compromised computer by the user again (this does not apply to a common case of a stolen, lost, or confiscated computer).[52] The attacker having physical access to a computer can, for example, install a hardware/software keylogger, a bus-mastering device capturing memory, or install any other malicious hardware or software, allowing the attacker to capture unencrypted data (including encryption keys and passwords), or to decrypt encrypted data using captured passwords or encryption keys. Therefore, physical security is a basic premise of a secure system. Attacks such as this are often called "evil maid attacks".[53]
Malware[edit]
TrueCrypt documentation states that TrueCrypt cannot secure data on a computer if it has any kind of malware installed. Malware may log keystrokes, thus exposing passwords to an attacker.[54]
The "Stoned" bootkit[edit]
The "Stoned" bootkit, an MBRrootkit presented by Austrian software developer Peter Kleissner at the Black Hat Technical Security Conference USA ,[55][56] has been shown capable of tampering TrueCrypt's MBR, effectively bypassing TrueCrypt's full volume encryption.[57][58][59][60][61] Potentially every hard disk encryption software is affected by this kind of attack if the encryption software does not rely on hardware-based encryption technologies like TPM, or if the attack is made with administrative privileges while the encrypted operating system is running.[62][63]
Two types of attack scenarios exist in which it is possible to maliciously take advantage of this bootkit: in the first one, the user is required to launch the bootkit with administrative privileges once the PC has already booted into Windows; in the second one, analogously to hardware keyloggers, a malicious person needs physical access to the user's TrueCrypt-encrypted hard disk: in this context this is needed to modify the user's TrueCrypt MBR with that of the Stoned bootkit and then place the hard disk back on the unknowing user's PC, so that when the user boots the PC and types his/her TrueCrypt password on boot, the "Stoned" bootkit intercepts it thereafter because, from that moment on, the Stoned bootkit is loaded before TrueCrypt's MBR in the boot sequence. The first type of attack can be prevented as usual by good security practices, e.g. avoid running non-trusted executables with administrative privileges. The second one can be successfully neutralized by the user if he/she suspects that the encrypted hard disk might have been physically available to someone he/she does not trust, by booting the encrypted operating system with TrueCrypt's Rescue Disk instead of booting it directly from the hard disk. With the rescue disk, the user can restore TrueCrypt's MBR to the hard disk.[64]
Trusted Platform Module[edit]
The FAQ section of the TrueCrypt website states that the Trusted Platform Module (TPM) cannot be relied upon for security, because if the attacker has physical or administrative access to the computer and you use it afterwards, the computer could have been modified by the attacker e.g. a malicious component—such as a hardware keystroke logger—could have been used to capture the password or other sensitive information. Since the TPM does not prevent an attacker from maliciously modifying the computer, TrueCrypt will not support the TPM.[63]
Security audits[edit]
In a graduate student at Concordia University published a detailed online report, in which he states that he has confirmed the integrity of the distributed Windows binaries of version a.[65]
A crowdfunding campaign attempting to conduct an independent security audit of TrueCrypt was successfully funded in October A non-profit organization called the Open Crypto Audit Project (OCAP) was formed, calling itself "a community-driven global initiative which grew out of the first comprehensive public audit and cryptanalysis of the widely used encryption software TrueCrypt".[66] The organization established contact with TrueCrypt developers, who welcomed the audit.[67][68] Phase I of the audit was successfully completed on 14 April , finding "no evidence of backdoors or malicious code". Matthew D. Green, one of the auditors, added "I think it's good that we didn't find anything super critical."[69]
One day after TrueCrypt's end of life announcement, OCAP confirmed that the audit would continue as planned, with Phase II expected to begin in June and wrap up by the end of September.[70][71] The Phase II audit was delayed, but was completed 2 April by NCC Cryptography Services. This audit "found no evidence of deliberate backdoors, or any severe design flaws that will make the software insecure in most instances."[72][73][74] The French National Agency for the Security of Information Systems (ANSSI) stated that while TrueCrypt and a have previously attained ANSSI certification, migration to an alternate certified product is recommended as a precautionary measure.[75]
According to Gibson Research Corporation, Steven Barnhart wrote to an email address for a TrueCrypt Foundation member he had used in the past and received several replies from "David". According to Barnhart, the main points of the email messages were that the TrueCrypt Foundation was "happy with the audit, it didn't spark anything", and that the reason for the announcement was that "there is no longer interest [in maintaining the project]."[76]
According to a study released 29 September , TrueCrypt includes two vulnerabilities in the driver that TrueCrypt installs on Windows systems allowing an attacker arbitrary code execution and privilege escalation via DLL hijacking.[77] In January , the vulnerability was fixed in VeraCrypt,[78] but it remains unpatched in TrueCrypt's unmaintained installers.
Legal cases[edit]
Operation Satyagraha[edit]
In July , several TrueCrypt-secured hard drives were seized from Brazilian banker Daniel Dantas, who was suspected of financial crimes. The Brazilian National Institute of Criminology (INC) tried unsuccessfully for five months to obtain access to his files on the TrueCrypt-protected disks. They enlisted the help of the FBI, who used dictionary attacks against Dantas' disks for over 12 months, but were still unable to decrypt them.[79][80]
United States v. John Doe[edit]
In the United States 11th Circuit Court of Appeals ruled that a John Doe TrueCrypt user could not be compelled to decrypt several of his hard drives.[81][82] The court's ruling noted that FBI forensic examiners were unable to get past TrueCrypt's encryption (and therefore were unable to access the data) unless Doe either decrypted the drives or gave the FBI the password, and the court then ruled that Doe's Fifth Amendment right to remain silent legally prevented the Government from making him or her do so.[83][84]
David Miranda[edit]
On 18 August David Miranda, partner of journalist Glenn Greenwald, was detained at London's Heathrow Airport by Metropolitan Police while en route to Rio de Janeiro from Berlin. He was carrying with him an external hard drive said to be containing sensitive documents pertaining to the global surveillance disclosures sparked by Edward Snowden. Contents of the drive were encrypted by TrueCrypt, which authorities said "renders the material extremely difficult to access."[85] Detective Superintendent Caroline Goode stated the hard drive contained around 60 gigabytes of data, "of which only 20 have been accessed to date." She further stated the process to decode the material was complex and "so far only 75 documents have been reconstructed since the property was initially received."[85]
Guardian contributor Naomi Colvin concluded the statements were misleading, stating that it was possible Goode was not even referring to any actual encrypted material, but rather deleted files reconstructed from unencrypted, unallocated space on the hard drive, or even plaintext documents from Miranda's personal effects.[86] Glenn Greenwald supported this assessment in an interview with Democracy Now!, mentioning that the UK government filed an affidavit asking the court to allow them to retain possession of Miranda's belongings. The grounds for the request were that they could not break the encryption, and were only able to access 75 of the documents that he was carrying, which Greenwald said "most of which were probably ones related to his school work and personal use."[87]
James DeSilva[edit]
In February , an Arizona Department of Real Estate IT department employee, James DeSilva, was arrested on charges of sexual exploitation of a minor through the sharing of explicit images over the Internet. His computer, encrypted with TrueCrypt, was seized, and DeSilva refused to reveal the password. Forensics detectives from the Maricopa County Sheriff's Office were unable to gain access to his stored files.[88]
Lauri Love[edit]
In October , British–Finnish activist Lauri Love was arrested by the National Crime Agency (NCA) on charges of hacking into a US department or agency computer and one count of conspiring to do the same.[89][90][91] The government confiscated all of his electronics and demanded he provide them with the necessary keys to decrypt the devices. Love refused. On 10 May a District Judge (Magistrate's Court) rejected a request by the NCA that Love be forced to turn over his encryption keys or passwords to TrueCrypt files on an SD card and hard drives that were among the confiscated property.[92]
Druking[edit]
In the special prosecutor investigation for Druking in South Korea, the special prosecutor decrypted some of the files encrypted by TrueCrypt by guessing the passphrase.[93][94]
The special prosecutor said the hidden volumes were especially difficult to deal with. He decrypted some of encrypted files by trying words and phrases the druking group had used elsewhere as parts of the passphrase in order to make educated guesses.[95][96][97][98]
License and source model[edit]
TrueCrypt was released under the source-available "TrueCrypt License" which is unique to the TrueCrypt software.[99][] It is not part of the panoply of widely used open source licenses and is not a free software license according to the Free Software Foundation (FSF) license list, as it contains distribution and copyright-liability restrictions.[] As of version a (the last full version of the software, released Feb ), the TrueCrypt License was version
Discussion of the licensing terms on the Open Source Initiative (OSI)'s license-discuss mailing list in October suggests that the TrueCrypt License has made progress towards compliance with the Open Source Definition but would not yet pass if proposed for certification as Open Source software.[][]
According to current OSI president Simon Phipps:
it is not at all appropriate for [TrueCrypt] to describe itself as "open source." This use of the term "open source" to describe something under a license that's not only unapproved by OSI but known to be subject to issues is unacceptable.[]
As a result of its questionable status with regard to copyright restrictions and other potential legal issues,[] the TrueCrypt License is not considered "free" by several major Linux distributions and is therefore not included in Debian,[] Ubuntu,[] Fedora,[] or openSUSE.[]
The wording of the license raises doubts whether those who use it have the right to modify it and use it within other projects. Cryptographer Matthew Green noted that "There are a lot of things [the developers] could have done to make it easier for people to take over this code, including fixing the licensing situation", and speculates that since they didn't do those things (including making the license more friendly), their intent was to prevent anyone from building on their code in the future.[]
End of life and license version [edit]
28 May announcement of discontinuation of TrueCrypt also came with a new version of the software. Among the many changes to the source code from the previous release were changes to the TrueCrypt License — including removal of specific language that required attribution of TrueCrypt as well as a link to the official website to be included on any derivative products — forming a license version []
On 16 June , the only alleged TrueCrypt developer still answering email replied to a message by Matthew Green asking for permission to use the TrueCrypt trademark for a fork released under a standard open source license. Permission was denied, which led to the two known forks being named VeraCrypt and CipherShed as well as a re-implementation named tc-play rather than TrueCrypt.[][]
Trademarks[edit]
In a US trademark for TrueCrypt was registered under the name of Ondrej Tesarik with a company name TrueCrypt Developers Association[] and a trademark on the "key" logo was registered under the name of David Tesarik with a company name TrueCrypt Developers Association.[]
In the company name TrueCrypt Foundation was registered in the US by a person named David Tesarik.[] The TrueCrypt Foundation non-profit organization last filed tax returns in ,[] and the company was dissolved in [citation needed]
See also[edit]
References[edit]
- ^ abcdefg"Version History". TrueCrypt Foundation. Archived from the original on 8 January Retrieved 1 October
- ^"TrueCrypt".
- ^ abcdGibson, Steve (5 June ), TrueCrypt, the final release, archive, Gibson Research Corporation, retrieved 1 August
- ^"Language Packs". manicapital.com. TrueCrypt Foundation. Archived from the original on 5 December
- ^"Open Crypto Audit Project"(PDF).
- ^"Version Information". TrueCrypt User's Guide, version . TrueCrypt Team. 2 February Retrieved 28 May [dead link]Alt URL
- ^ abcdeTrueCrypt Team (3 February ). "P. Le Roux (author of E4M) accused by manicapital.com (SecurStar)". Newsgroup:&#;manicapital.comisk. Usenet:&#;a7b8b26d77f67aa7c5cc3f55b84c@manicapital.com Retrieved 28 May
- ^David T. (7 February ). "Summary of current TrueCrypt situation?". Newsgroup:&#;manicapital.comisk. Usenet:&#;30eaece70b0fecd85a@manicapital.com Retrieved 28 May
- ^Carsten Krueger (7 February ). "Truecrypt for David T. from Truecrypt-Team". Newsgroup:&#;manicapital.comisk. Usenet:&#;76va20di0jami8nspkkuddgj6etabhh@manicapital.com Retrieved 28 May
- ^Andraia Matrix (6 February ). "Unofficial TrueCrypt Site". Newsgroup:&#;manicapital.comisk. Usenet:&#;76va20di0jami8nspkkuddgj6etabhh@manicapital.com Retrieved 28 May
- ^"Is the source code of your software available?". Drivecrypt FAQ. SecurStar. Archived from the original on 2 June Retrieved 28 May
- ^Ratliff, Evan (29 April ). "The Next Big Deal". Retrieved 1 May
- ^"Version History"(PDF). TrueCrypt User's Guide, version a. TrueCrypt Foundation. 7 February Archived(PDF) from the original on 30 December Retrieved 2 March
- ^tc-foundation (28 May ). "TrueCrypt project page". SourceForge. Archived from the original on 30 May Retrieved 30 May
- ^Goodin, Dan (28 May ), ""TrueCrypt is not secure," official SourceForge page abruptly warns", Ars Technica, Condé Nast, retrieved 28 May
- ^O'Neill, Patrick (28 May ). "TrueCrypt, encryption tool used by Snowden, shuts down due to alleged 'security issues'". The Daily Dot. Retrieved 28 May
- ^McAllister, Neil (28 May ), TrueCrypt considered HARMFUL – downloads, website meddled to warn: 'It's not secure', The Register, retrieved 29 May
- ^Goodin, Dan (29 May ), "Bombshell TrueCrypt advisory: Backdoor? Hack? Hoax? None of the above?", Ars Technica, Condé Nasta, retrieved 29 May
- ^Bar-El, Hagai (30 May ), The status of TrueCrypt, retrieved 30 May
- ^ ab"Supported Operating Systems". TrueCrypt Documentation. TrueCrypt Foundation. Retrieved 24 May
- ^"Operating Systems Supported for System Encryption". TrueCrypt Documentation. TrueCrypt Foundation. Archived from the original on 8 January Retrieved 24 May
- ^ ab"DragonFly On-Line Manual Pages". DragonFly BSD Project. Retrieved 17 July
- ^ ab"README". tc-play. Retrieved 14 March
- ^"Fedora Review Request: tcplay - Utility to create/open/map TrueCrypt-compatible volumes". FEDORA. Retrieved 25 January
- ^"index&#;: kernel/git/stable/manicapital.com - path: root/drivers/md/dm-crypt.c". manicapital.com cgit. 20 January Line Retrieved 13 June
What’s New in the Adobe CS5 Master key BY TEAM RED HOT serial key or number?
Screen Shot
System Requirements for Adobe CS5 Master key BY TEAM RED HOT serial key or number
- First, download the Adobe CS5 Master key BY TEAM RED HOT serial key or number
-
You can download its setup from given links:


