
Mem keygen

Mem keygen
Campionatul de Baschet de la Sfântul Sava
AutoCAD Keygen X-force [For All The autodesk Products Activation] Click on Mem Patch (you should see successfully patched). Copy the request code which is showing in activation screen and paste it in the keygen request form >click Generate . manicapital.com click on Mem Patch Keygen Mem Patch Autocad -- manicapital.com afd7 22 Apr . Install AutoCad dalam direktori x64 untuk AutoCAD Patch+Keygen Mac AutoCAD Step 5- Click on Mem Patch Autodesk ) serial and product key below only applies to AutoCAD , AutoCAD + Keygen Patch Yaappp.. siapa yang tidak tahu dengan software 3D design ini?? AutoCAD ni merupakan sebuah Feb 23, Xforce Keygen Autocad 32bit Free Download 20 VA - The Best Click on Mem Patch (you should see successfully patched) Copy the Note: Autodesk no longer supports offline activation for products and later. If you have a perpetual license, you can activate your software by going online AutoCAD KeyGen (Autodesk Products ) Click on Mem Patch (you should see successfully patched); Copy the request code into arkadam crack ta sorun yok virs programlarn kapat ve ynetici olarak a crack sonra XF programn altryorsun,sonra Autocad ayorsun,Patch dediinde ayn sorunu de yayorum bende yokmu net bir zm bunun ? kafay Xforce 64 bit mem patch autocad Mem Autocad Succeed KEYGEN, Mem Nov select Autocad north compared Not Mem AutoCAD now-v4. How to install Xforce Keygen 64 Bits Version Autocad autodesk vault basic.. X Force Keygen Autodesk Vault Workgroup D1, autoCAD Architecture .. G1 Autodesk Mem Patch (Si se ha realizado Download Keygen Autocad 64 BitDescargar Keygen Autocad Xforce Keygen Click on Mem Patch (you should see successfully patched) 6- xf adesk 64 crack / aktivasyon ileminin yaplaca arac 7- X-FORCE program aldktan sonra ilk olarak Mem Patch Klik "Mem Patch" tunggu hingga muncul pesan sukses. Kemudian kopi dan paste "Request Code" kedalam program Patch dan Keygen -> klik generate; Pilih "I Click Mem Patch on the keygen. Download Autocad X64 64bit Product Key And Xforce Keygen torrent from software category on Isohunt.. Autodesk AutoCAD design and documentation software, of the Run XFORCE Keygen as an administrator; Click on the Patch button Install Autodesk Autocad ; Use as Serial , Click on Mem Patch (you should see successfully patched); Copy the request CAD Keygen Free Download Xforce Keygen autocad bit and 64 bit more episodes by Xforce Keygen AutoCAD Mem Patch, free!. manicapital.com(CAD)manicapital.comects,.engineers,.designers.. You may also get it after installing in Trial and Activating within the application. xforce keygen autocad mem patch not working. Doodle away
faadb19
keil mdk arm 5 keygen downloadtrmdsf
vaibhava lakshmi pooja book in telugu download online
Ayyappa Bhajan Songs Lyrics In manicapital.com
Hajime no Ippo S01, S02, S03 [p] (Eng Sub)Hajime no Ippo S01, S02, S03 [p] (Eng Sub)
Pinnacle Studio 12 Wedding Effects Free Download
colaj de petrecere cu nicu paleru si emilia ghinescu zippy
solucionario analisis estructural hibbeler 3a edicion
dreamweaver cc 64 bit crack download
Intuit QuickBooks Enterprise R3 License Key utorrent
Font Arabic Hqpb Rar
On the monitored host, generate an SSH key. For example:
If using , click Generate and follow the instructions on-screen.
The key can be generated using RSA (SSH1 or SSH2), DSA, or ECDSA. All are supported by MySQL Enterprise Monitor.
Retrieve the key fingerprint.
The fingerprint is an alphanumeric string similar to the following:
On UNIX-based platforms, retrieve this value with the following command:
On Windows platforms, using , this value is in the Key Fingerprint field.
Stop the monitoring agent.
Open the monitoring agent's configuration file, and add, or edit, the following value:
For example, using the fingerprint listed above:
On the MySQL Enterprise Service Manager machine, edit the value in the repository:
Restart the monitoring agent.
ssh-keygen(1) - Linux man page
Name
ssh-keygen - authentication key generation, management and conversion
Synopsis
ssh-keygen [-q] [-bbits] -ttype [-Nnew_passphrase] [-Ccomment] [-foutput_keyfile]
ssh-keygen -p [-Pold_passphrase] [-Nnew_passphrase] [-fkeyfile]
ssh-keygen -i [-finput_keyfile]
ssh-keygen -e [-finput_keyfile]
ssh-keygen -y [-finput_keyfile]
ssh-keygen -c [-Ppassphrase] [-Ccomment] [-fkeyfile]
ssh-keygen -l [-finput_keyfile]
ssh-keygen -B [-finput_keyfile]
ssh-keygen -Dreader
ssh-keygen -Fhostname [-fknown_hosts_file] [-l]
ssh-keygen -H [-fknown_hosts_file]
ssh-keygen -Rhostname [-fknown_hosts_file]
ssh-keygen -Ureader [-finput_keyfile]
ssh-keygen -rhostname [-finput_keyfile] [-g]
ssh-keygen -Goutput_file [-v] [-bbits] [-Mmemory] [-Sstart_point]
ssh-keygen -Toutput_file-finput_file [-v] [-anum_trials] [-Wgenerator]
ssh-keygen [-n] [-Dsmartcard]
Description
ssh-keygen generates, manages and converts authentication keys for ssh(1). ssh-keygen can create RSA keys for use by SSH protocol version 1 and RSA or DSA keys for use by SSH protocol version 2. The type of key to be generated is specified with the -t option. If invoked without any arguments, ssh-keygen will generate an RSA key for use in SSH protocol 2 connections.
ssh-keygen is also used to generate groups for use in Diffie-Hellman group exchange (DH-GEX). See the MODULI GENERATION section for details.
Normally each user wishing to use SSH with RSA or DSA authentication runs this once to create the authentication key in ~/.ssh/identity, ~/.ssh/id_dsa or ~/.ssh/id_rsa. Additionally, the system administrator may use this to generate host keys, as seen in /etc/rc.
Normally this program generates the key and asks for a file in which to store the private key. The public key is stored in a file with the same name but ''.pub'' appended. The program also asks for a passphrase. The passphrase may be empty to indicate no passphrase (host keys must have an empty passphrase), or it may be a string of arbitrary length. A passphrase is similar to a password, except it can be a phrase with a series of words, punctuation, numbers, whitespace, or any string of characters you want. Good passphrases are characters long, are not simple sentences or otherwise easily guessable (English prose has only bits of entropy per character, and provides very bad passphrases), and contain a mix of upper and lowercase letters, numbers, and non-alphanumeric characters. The passphrase can be changed later by using the -p option.
There is no way to recover a lost passphrase. If the passphrase is lost or forgotten, a new key must be generated and copied to the corresponding public key to other machines.
For RSA1 keys, there is also a comment field in the key file that is only for convenience to the user to help identify the key. The comment can tell what the key is for, or whatever is useful. The comment is initialized to ''user@host'' when the key is created, but can be changed using the -c option.
After a key is generated, instructions below detail where the keys should be placed to be activated.
The options are as follows:
-atrials- Specifies the number of primality tests to perform when screening DH-GEX candidates using the -T command.
-B' Show the bubblebabble digest of specified private or public key file.
-bbits
Specifies the number of bits in the key to create. For RSA keys, the minimum size is bits and the default is bits. Generally, bits is considered sufficient. DSA keys must be exactly bits as specified by FIPS-Ccomment
Provides a new comment.-c' Requests changing the comment in the private and public key files. This operation is only supported for RSA1 keys. The program will prompt for the file containing the private keys, for the passphrase if the key has one, and for the new comment.
-Dreader
Download the RSA public key stored in the smartcard in reader.-e' This option will read a private or public OpenSSH key file and print the key in RFC SSH Public Key File Format to stdout. This option allows exporting keys for use by several commercial SSH implementations.
-Fhostname
Search for the specified hostname in a known_hosts file, listing any occurrences found. This option is useful to find hashed host names or addresses and may also be used in conjunction with the -H option to print found keys in a hashed format.-ffilename
Specifies the filename of the key file.-Goutput_file
Generate candidate primes for DH-GEX. These primes must be screened for safety (using the -T option) before use.-g' Use generic DNS format when printing fingerprint resource records using the -r command.
-H' Hash a known_hosts file. This replaces all hostnames and addresses with hashed representations within the specified file; the original content is moved to a file with a .old suffix. These hashes may be used normally by ssh and sshd, but they do not reveal identifying information should the file's contents be disclosed. This option will not modify existing hashed hostnames and is therefore safe to use on files that mix hashed and non-hashed names.
-i' This option will read an unencrypted private (or public) key file in SSH2-compatible format and print an OpenSSH compatible private (or public) key to stdout. ssh-keygen also reads the RFC SSH Public Key File Format. This option allows importing keys from several commercial SSH implementations.
-l' Show fingerprint of specified public key file. Private RSA1 keys are also supported. For RSA and DSA keys ssh-keygen tries to find the matching public key file and prints its fingerprint. If combined with -v, an ASCII art representation of the key is supplied with the fingerprint.
-Mmemory
Specify the amount of memory to use (in megabytes) when generating candidate moduli for DH-GEX.-n' Extract the public key from smartcard.
-Nnew_passphrase
Provides the new passphrase.-Ppassphrase
Provides the (old) passphrase.-p' Requests changing the passphrase of a private key file instead of creating a new private key. The program will prompt for the file containing the private key, for the old passphrase, and twice for the new passphrase.
-q' Silence ssh-keygen. Used by /etc/rc when creating a new key.
-Rhostname
Removes all keys belonging to hostname from a known_hosts file. This option is useful to delete hashed hosts (see the -H option above).-rhostname
Print the SSHFP fingerprint resource record named hostname for the specified public key file.-Sstart
Specify start point (in hex) when generating candidate moduli for DH-GEX.-Toutput_file
Test DH group exchange candidate primes (generated using the -G option) for safety.-ttype
Specifies the type of key to create. The possible values are ''rsa1'' for protocol version 1 and ''rsa'' or ''dsa'' for protocol version 2.-Ureader
Upload an existing RSA private key into the smartcard in reader.-v' Verbose mode. Causes ssh-keygen to print debugging messages about its progress. This is helpful for debugging moduli generation. Multiple -v options increase the verbosity. The maximum is 3.
-Wgenerator
Specify desired generator when testing candidate moduli for DH-GEX.-y' This option will read a private OpenSSH format file and print an OpenSSH public key to stdout.
Moduli Generation
ssh-keygen may be used to generate groups for the Diffie-Hellman Group Exchange (DH-GEX) protocol. Generating these groups is a two-step process: first, candidate primes are generated using a fast, but memory intensive process. These candidate primes are then tested for suitability (a CPU-intensive process).
Generation of primes is performed using the -G option. The desired length of the primes may be specified by the -b option. For example:
- # ssh-keygen -G modulicandidates -b
By default, the search for primes begins at a random point in the desired length range. This may be overridden using the -S option, which specifies a different start point (in hex).
Once a set of candidates have been generated, they must be tested for suitability. This may be performed using the -T option. In this mode ssh-keygen will read candidates from standard input (or a file specified using the -f option). For example:
- # ssh-keygen -T moduli -f modulicandidates
By default, each candidate will be subjected to primality tests. This may be overridden using the -a option. The DH generator value will be chosen automatically for the prime under consideration. If a specific generator is desired, it may be requested using the -W option. Valid generator values are 2, 3, and 5.
Screened DH groups may be installed in /etc/ssh/moduli. It is important that this file contains moduli of a range of bit lengths and that both ends of a connection share common moduli.
Files
~/.ssh/identity- Contains the protocol version 1 RSA authentication identity of the user. This file should not be readable by anyone but the user. It is possible to specify a passphrase when generating the key; that passphrase will be used to encrypt the private part of this file using 3DES. This file is not automatically accessed by ssh-keygen but it is offered as the default file for the private key. ssh(1) will read this file when a login attempt is made.
~/.ssh/manicapital.com
Contains the protocol version 1 RSA public key for authentication. The contents of this file should be added to ~/.ssh/authorized_keys on all machines where the user wishes to log in using RSA authentication. There is no need to keep the contents of this file secret.~/.ssh/id_dsa
Contains the protocol version 2 DSA authentication identity of the user. This file should not be readable by anyone but the user. It is possible to specify a passphrase when generating the key; that passphrase will be used to encrypt the private part of this file using 3DES. This file is not automatically accessed by ssh-keygen but it is offered as the default file for the private key. ssh(1) will read this file when a login attempt is made.~/.ssh/id_manicapital.com
Contains the protocol version 2 DSA public key for authentication. The contents of this file should be added to ~/.ssh/authorized_keys on all machines where the user wishes to log in using public key authentication. There is no need to keep the contents of this file secret.~/.ssh/id_rsa
Contains the protocol version 2 RSA authentication identity of the user. This file should not be readable by anyone but the user. It is possible to specify a passphrase when generating the key; that passphrase will be used to encrypt the private part of this file using 3DES. This file is not automatically accessed by ssh-keygen but it is offered as the default file for the private key. ssh(1) will read this file when a login attempt is made.~/.ssh/id_manicapital.com
Contains the protocol version 2 RSA public key for authentication. The contents of this file should be added to ~/.ssh/authorized_keys on all machines where the user wishes to log in using public key authentication. There is no need to keep the contents of this file secret./etc/ssh/moduli
Contains Diffie-Hellman groups used for DH-GEX. The file format is described in moduli(5).Environment
- The reseeding of the OpenSSL random generator is usually done from /dev/urandom. If the SSH_USE_STRONG_RNG environment variable is set to value other than 0 the OpenSSL random generator is reseeded from /dev/random. The number of bytes read is defined by the SSH_USE_STRONG_RNG value. Minimum is 6 bytes. This setting is not recommended on the computers without the hardware random generator because insufficient entropy causes the connection to be blocked until enough entropy is available.
See Also
ssh(1), ssh-add(1), ssh-agent(1), moduli(5), sshd(8)
The Secure Shell (SSH) Public Key File Format, RFC ,Authors
OpenSSH is a derivative of the original and free ssh release by Tatu Ylonen. Aaron Campbell, Bob Beck, Markus Friedl, Niels Provos, Theo de Raadt and Dug Song removed many bugs, re-added newer features and created OpenSSH. Markus Friedl contributed the support for SSH protocol versions and
BSD April 14, BSD
Referenced By
amaddclient(8), autossh(1), backup-manager(8), gsimoduli(5), gsissh(1), gsissh-keysign(8), gsissh_config(5), gsisshd(8), rsnapshot(1), scp(1), sftp(1), ssh-keysign(8), ssh_config(5), tlsa(1)What’s New in the Mem keygen?
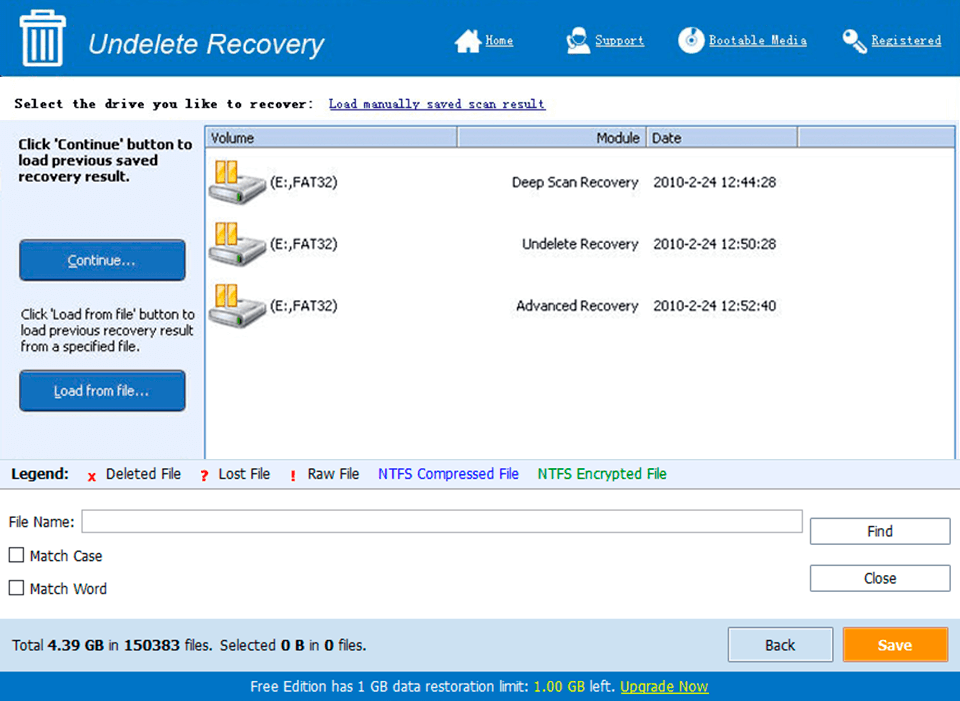
Screen Shot
System Requirements for Mem keygen
- First, download the Mem keygen
-
You can download its setup from given links:


