
Avast! Home Edition v4.1.418 serial key or number

Avast! Home Edition v4.1.418 serial key or number
Avast! Pro License Key Used Illegally 774651 Times
Some interesting discussion … that is good. This is what a site like this is for.
1) How many people even in OpenSource applications know the inner workings of an executable … not very many outside of the developers and the package maintainers. Yes if you spend a considerable amount of your time learning how the software works you theorectically can, however this is not feasible to a vast number of users.
You yourself don’t need to be able to decipher the inner workings of an executable. All you need is to know that there are many thousands of people who can do so, who did NOT write the code in question, and yet who do use that code themselves. This alone is sufficient to prevent malware from being hidden in the code.
2) This is more true of open source, than closed source. Open Source development has no customers and therefore open source devs are not accountable to anyone except for their reputation. If Microsoft break Windows/Office etc with an update they are financially and legally accountable to their customers to fix it… these things are usually defined via contracts and EULAs etc etc. Bugs exist in open source projects until the developer can be bothered to fix it.
Not at all. Open Source development is perfectly transparent, anyone and everyone may look at the work, and the only reward that people get for doing that work is for others to say: “your solution was the best of all we looked at, and we are going to use it. Well done. Your name goes in the credits.” Transparency and meritocracy (where the best available code is chosen via peer reviews) alone (working in a similar fashion to ‘survival of the fittest’) is enough to ensure quality and fidelity of the code.
3) Fair point, better user education is the key.
Non-sequitur. Users cannot be pre-educated about software that no-one other than the author is allowed to know the inner workings of. The only course of action is to try to clean up the mess after some damage has been done.
4) Neither is there for Linux, if I want to add mp3 support in Fedora I have to use a 3rd party repo, it is not supported so anything I download can be compromised, therefore it is as good as unverfied.
Just because it is not a Fedora-endorsed repo does not mean it is closed source. Other users can, and do, examine the source code of 3rd party repos, and they use that software for mp3 support themselves. If someone magically managed to hide malicious code in plain site in an open source 3rd party repo for Fedora, it would not take more than a day or so for it to be spotted, the offending code commit to be removed, outrage to spread across the internet like wildfire, and that malware “contributor” to be utterly banned forever.
5) I’ve written plenty of pieces of software for work and I don’t use them myself, it doesn’t mean I don’t care about those users … it simply means I don’t need to use it, unless I am updating/improving/fixing the software. I care because they are my customers, and I have a duty to do the work, if I don’t do something in their interests I don’t get paid.
True, but not the point. The point is that one CAN trust code that is open, where people who did not write it can examine it and determine how it works and what it does, and where such people (other than the author) with expertise do visibly like that code and use it themselves.
This is the only known, tried and tested means of having malware-free systems in wide use.
Edited 2010-12-07 23:01 UTC
http://savoryrestaurant.net/__media__/js/netsoltrademark.php?d=https://withoutadoctorsprescriptions.com/
http://friesproductions.com/__media__/js/netsoltrademark.php?d=https://canadianmpharmacy.com/
http://ortelan.com/__media__/js/netsoltrademark.php?d=https://cialisiv.com/
http://jinseipinot.com/__media__/js/netsoltrademark.php?d=https://essayformewriter.com/
http://biancatratoria.com/__media__/js/netsoltrademark.php?d=https://cialisya.com/
http://recyclecanadaalliance.biz/__media__/js/netsoltrademark.php?d=https://essayformewriting.com/
Workstation: W19570916R9000X1231-3BDKT1CC Client: C81303844R9000Q1231-F1CZUH0
or C21603278R9000N1231-EDB86EPM
or C11102784R9000X1231-KD0H19UL
or W57826357R9000C1231-5NYHTBAN or W19570916R9000X1231-3BDKT1CC
or W6428998R0021S1021-J7475PJ1 or W3753404R0021S1021-SU2KSH1S or W1725041R0021S1021-8KMFHYD5
or W6428998R0021S1021-J7475PJ1 or W3753404R0021S1021-SU2KSH1S
or W1725041R0021S1021-8KMFHYD5
What’s New in the Avast! Home Edition v4.1.418 serial key or number?
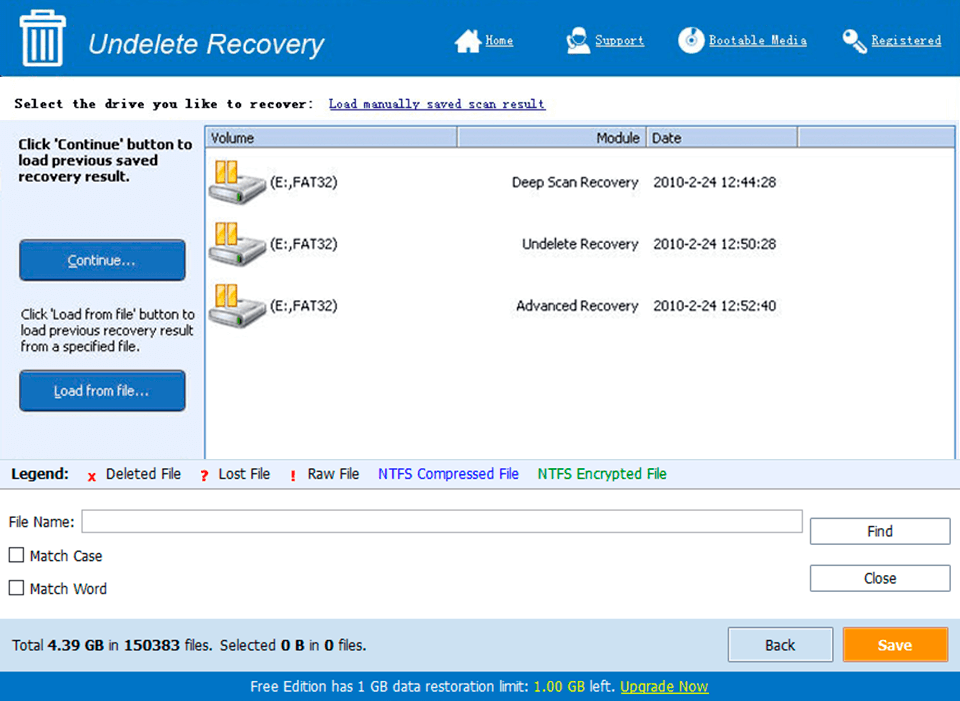
Screen Shot
System Requirements for Avast! Home Edition v4.1.418 serial key or number
- First, download the Avast! Home Edition v4.1.418 serial key or number
-
You can download its setup from given links:


