
101 Bluck Email Direct Sender 2.0.81 serial key or number

101 Bluck Email Direct Sender 2.0.81 serial key or number
CompTIA Security+ Certification Guide: Master IT security essentials and exam topics for CompTIA Security+ SY0-501 certification [Paperback ed.] 1789348013, 9781789348019
Citation preview
CompTIA Security+ Certification Guide
Master IT security essentials and exam topics for CompTIA Security+ SY0-501 certification
Ian Neil
BIRMINGHAM - MUMBAI
CompTIA Security+ Certification Guide Copyright © 2018 Packt Publishing All rights reserved. No part of this book may be reproduced, stored in a retrieval system, or transmitted in any form or by any means, without the prior written permission of the publisher, except in the case of brief quotations embedded in critical articles or reviews. Every effort has been made in the preparation of this book to ensure the accuracy of the information presented. However, the information contained in this book is sold without warranty, either express or implied. Neither the author, nor Packt Publishing or its dealers and distributors, will be held liable for any damages caused or alleged to have been caused directly or indirectly by this book. Packt Publishing has endeavored to provide trademark information about all of the companies and products mentioned in this book by the appropriate use of capitals. However, Packt Publishing cannot guarantee the accuracy of this information. Commissioning Editor: Gebin George Acquisition Editor: Rahul Nair Content Development Editor: Arjun Joshi Technical Editor: Varsha Shivhare Copy Editor: Safis Editing Project Coordinator: Kinjal Bari Proofreader: Safis Editing Indexer: Tejal Daruwale Soni Graphics: Jisha Chirayil Production Coordinator: Shraddha Falebhai First published: September 2018 Production reference: 2191118 Published by Packt Publishing Ltd. Livery Place 35 Livery Street Birmingham B3 2PB, UK. ISBN 978-1-78934-801-9
www.packtpub.com
mapt.io
Mapt is an online digital library that gives you full access to over 5,000 books and videos, as well as industry leading tools to help you plan your personal development and advance your career. For more information, please visit our website.
Why subscribe? Spend less time learning and more time coding with practical eBooks and Videos from over 4,000 industry professionals Improve your learning with Skill Plans built especially for you Get a free eBook or video every month Mapt is fully searchable Copy and paste, print, and bookmark content
Packt.com Did you know that Packt offers eBook versions of every book published, with PDF and ePub files available? You can upgrade to the eBook version at www.packt.com and as a print book customer, you are entitled to a discount on the eBook copy. Get in touch with us at [email protected] for more details. At www.packt.com, you can also read a collection of free technical articles, sign up for a range of free newsletters, and receive exclusive discounts and offers on Packt books and eBooks.
Contributor About the author Ian Neil is one of the world’s top trainers of Security+ 501, who has the ability to break down information into manageable chunks helping no background knowledge. Ian was a finalist of the Learning and Performance Institute Trainer of the Year Awards. He has worked for the US Army in Europe and designed a Security+ course that catered to people from all backgrounds and not just the IT professional, with an extremely successful pass rate. He was instrumental in helping Microsoft get their office in Bucharest off the ground, where he won a recognition award for being one of their top trainers. Ian is an MCT, MCSE, A+, Network+, Security+, CASP, and RESILIA practitioner who over the past 20 years has worked with high-end training providers.
Packt is searching for authors like you If you're interested in becoming an author for Packt, please visit authors.packtpub.com and apply today. We have worked with thousands of developers and tech professionals, just like you, to help them share their insight with the global tech community. You can make a general application, apply for a specific hot topic that we are recruiting an author for, or submit your own idea.
Table of Contents Preface
1
Chapter 1: Understanding Security Fundamentals CIA triad concept Identifying security controls Administrative controls Technical controls Physical controls Preventative controls Deterrent controls Detective controls Corrective controls Compensating controls Access controls
Discretionary access control Least privilege Mandatory access control Linux permissions (not SELinux) Role-based access control Rule-Based Access Control Attribute-based access control Group-based access
Hashing and data integrity Hash practical Hash exercise
Defense in depth model Review questions Answers and explanations Chapter 2: Conducting Risk Analysis Risk management Importance of policy, plans, and procedures Standard operating procedures Agreement types
Personnel management—policies and procedures
Role-based awareness training General security policies
Business impact analysis concepts Privacy threshold assessment/privacy impact assessment Mission-essential functions/identification of critical systems Example
5 6 7 7 8 9 11 11 11 12 12 12 13 14 14 15 17 17 17 17 18 19 19 21 22 24 26 27 27 28 28 29 32 32 33 33 34 34
Table of Contents
Supply chain risk assessment Example
Business impact analysis concepts Calculating loss Example
Risk procedures and concepts Threat assessment Threat actors
Risk treatment
Risk register Qualitative/quantitative risk analysis Review questions Answers and explanations Chapter 3: Implementing Security Policies and Procedures Industry-standard frameworks and reference architecture OSI reference model TCP/IP model Types of frameworks Benchmarks/secure configuration guides
Policies and user guides
Security configuration guides – web servers Network infrastructure device user guides General purpose guides
Implementing data security and privacy practices Destroying data and sanitizing media Data sensitivity labeling and handling Data retention – legal and compliance Data roles
Practical – creating a baseline Review questions Answers and explanations
Chapter 4: Delving into Identity and Access Management Understanding identity and access management concepts Passwords Default/administrator password Passwords – group policy Password recovery Authentication factors Number of factor examples Transitive trust Federation services Shibboleth Single sign-on
[ ii ]
34 35 35 36 36 37 37 38 39 40 41 41 43 45 46 46 47 48 49 49 52 52 53 54 54 56 56 57 58 63 65 67 68 68 68 69 71 71 72 73 74 76 76
Table of Contents
Installing and configuring identity and access services LDAP Kerberos
Internet-based open source authentication
Authentication, authorization, and accounting (AAA) servers Authentication
Learning about identity and access management controls Biometrics Security tokens and devices Certification-based authentication Port-based authentication
Common account management practices Account types Account creation Employees moving departments Disabling an account
Account recertification Account maintenance Account monitoring Security Information and Event Management Group-based access control Credential management User account reviews
Practical exercise – password policy Review questions Answers and explanations Chapter 5: Understanding Network Components OSI – reference model Installing and configuring network components Firewall Router
Access control list– network devices Intrusion-prevention system Intrusion-detection system Modes of detection Modes of operation
Monitoring data
Switch
Layer 3 switch
Proxy server Reverse proxy Remote access Virtual private network using L2TP/IPSec IPSec IPSec – handshake
VPN concentrator
[ iii ]
77 77 79 81 81 82 83 84 86 86 87 87 87 90 90 91 91 91 92 92 95 96 96 97 97 100 104 106 108 108 110 111 112 112 112 113 113 114 115 116 117 118 119 119 120 121
Table of Contents
Site-to-site VPN VPN always on versus on-demand SSL VPN Split tunnelling Load balancer Clustering Data-loss prevention
Security information and event management Mail gateway Cloud-based email Media gateway Hardware security module Software-defined network
Secure network architecture concepts Network address translation Port address translation Network Access Control (NAC) Honeypot Secure Socket Layer accelerators SSL/TLS decryptor Sensor/collector Tap/port mirror DDoS mitigator Segregation/segmentation/isolation Security device/technology placement DMZ device placement LAN device placement
Aggregation switches
Implementing secure protocols Use case
File transfer – use case Remote access – use case Email – use case Name resolution – use case Hostname DNSSEC NETBIOS
Web – use case Voice and video – use case Network address allocation – use case
IP Version 4 IP Version 4 – lease process IP Version 4 lease process – troubleshooting IP Version 6 addressing
Subscription services – use case Routing – use case Time synchronization – use case Directory services – use case
[ iv ]
121 121 122 122 123 125 125 126 127 127 127 127 127 128 129 130 130 132 132 132 133 133 133 133 135 136 136 137 137 140 140 141 142 142 143 144 145 145 146 146 147 148 148 149 151 151 152 153
Table of Contents Active Directory
Switching – use case Simple network management protocol – use case
Implementing wireless security
Wireless access points – controllers Securing access to your wireless access point
Wireless bandwidth/band selection Wireless channels Wireless antenna types and signal strength Wireless coverage Wireless encryption Wireless – Open System Authentication Wireless – WPS Wireless – captive portal Wireless attacks Wireless authentication protocols
Review questions Answers and explanations Chapter 6: Understanding Cloud Models and Virtualization Cloud computing Implementing different cloud deployment models Cloud service models Disk resiliency and redundancy Redundant array of independent disks
Storage area network Understanding cloud storage concepts Exploring virtual networks Virtual desktop infrastructure VDE
Heating, ventilation, and air-conditioning (HVAC) Network environments On-premises Hosted services Cloud-hosting services
Practical exercise – is the cloud cost-effective? Review questions Answers and explanations Chapter 7: Managing Hosts and Application Deployment Deploying mobile devices securely Bring your own device Choose your own device Corporate-owned personally-enabled Virtual desktop infrastructure
[v]
154 155 156 156 157 157 159 159 160 161 161 162 162 162 163 163 164 167 171 172 174 178 183 183 186 188 189 194 194 195 195 196 196 196 197 197 199 201 202 203 204 204 205
Table of Contents
Mobile device connection methods
Mobile device management concepts Accessing the device
Device management Device protection Device data Mobile device enforcement and monitoring Industrial control system Supervisory control and data acquisition
Mobile devices – security implications of embedded systems Special-purpose devices Secure application development and deployment concepts Development life cycle models – waterfall versus Agile Waterfall Agile Agile versus waterfall
DevOps
Secure DevOps Secure coding techniques Code quality and testing
Server-side versus client-side execution and validation Review questions Answers and explanations Chapter 8: Protecting Against Attacks and Vulnerabilities Virus and malware attacks Social engineering attacks Common attacks Application/service attacks
Programming attacks
Example 1—JavaScript—creating a money variable Example 2—JavaScript—setting the day of the month
Hijacking related attacks Driver manipulation Cryptographic attacks Password attacks Wireless attacks Penetration testing
Penetration testing techniques
Vulnerability scanning concepts Credentialed versus non-credentialed scans Penetration testing versus vulnerability scanning Practical exercise—running a vulnerability scanner Review questions [ vi ]
205 207 208 209 209 210 211 213 213 214 216 218 219 219 220 220 221 221 221 224 225 225 228 231 232 236 240 240 246 247 247 250 251 251 252 254 257 257 258 260 260 261 267
Table of Contents
Answers and explanations Chapter 9: Implementing the Public Key Infrastructure PKI concepts Certificate hierarchy Certificate trust Certificate validity Certificate management concepts Certificate types
Asymmetric and symmetric encryption
Encryption explained Digital signatures explained Cryptography algorithms and their characteristics
Symmetric algorithms Asymmetric algorithms Symmetric versus asymmetric analogy XOR encryption
Key-stretching algorithms Cipher modes
Stream versus block cipher analogy
Hashing and data integrity Comparing and contrasting the basic concepts of cryptography Asymmetric – PKI
Asymmetric – weak/depreciated algorithms Asymmetric – ephemeral keys
Symmetric algorithm – modes of operation
Symmetric encryption – streams versus block ciphers Symmetric encryption – confusion Symmetric encryption – secret algorithm Symmetric – session keys
Hashing algorithms Crypto service provider Crypto module Protecting data
Basic cryptographic terminology Obfuscation Pseudo-random number generator Nonce Perfect forward secrecy Security through obscurity Collision Steganography Diffusion Implementation versus algorithm
Common use cases for cryptography Supporting confidentiality
[ vii ]
270 273 274 274 278 279 280 282 284 284 288 289 290 290 292 292 293 293 293 295 296 296 296 297 297 297 297 297 298 298 298 298 299 299 299 300 300 300 300 300 301 301 301 301 302
Table of Contents
Supporting integrity Supporting non-repudiation Supporting obfuscation Low-power devices Low latency High resiliency Supporting authentication Resource versus security constraints
Practical exercises
Practical exercise 1 – building a certificate server Practical exercise 2 – encrypting data with EFS and stealing certificates Practical exercise 3 – revoking the EFS certificate
Review questions Answers and explanations Chapter 10: Responding to Security Incidents Incident response procedures Incident response process
Understanding the basic concepts of forensics Five-minute practical
Software tools for assessing the security posture of an organization Backup utilities Backup types Command-line tools Analyzing and interpreting output from security technologies
Review questions Answers and explanations Chapter 11: Managing Business Continuity Implementing secure systems design Hardware/firmware security Operating systems Securing IT systems Peripherals
The importance of the secure staging deployment concepts Troubleshooting common security issues Misconfigured devices Personnel issues Software issues
Disaster recovery and the continuity of operations concepts Review questions Answers and explanations Chapter 12: Mock Exam 1 [ viii ]
302 302 303 303 303 303 303 304 304 304 305 306 306 309 312 313 314 316 317 322 327 328 329 336 342 345 348 349 350 351 352 353 354 355 357 358 359 360 362 364 366
Table of Contents
Chapter 13: Mock Exam 2 Appendix A: Preparing for the CompTIA Security+ 501 Exam Tips on taking the exam Exam preparation Practical 1—drag and drop—attacks Practical 2—drag and drop—certificates Practical 3—drag and drop—ports/protocols Practical 4—drag and drop—authentication factors Practical 5—drag and drop—general Drag and drop—answers Linux information Appendix B: Acronyms
382
Assessment
425
Other Books You May Enjoy
488
Index
491
[ ix ]
400 400 401 403 403 405 406 407 408 413 414
Preface This book will help you to understand security fundamentals, ranging from the CIA triad right through to identity and access management. This book describes network infrastructure and how it is evolving with the implementation of virtualization, and different cloud models and their storage. You will learn how to secure devices and applications that are used by a company. Refer to www.ianneil501.com for additional exam resources.
Who this book is for This book is designed for anyone who is seeking to pass the CompTIA Security+ SY0-501 exam. It is a stepping stone for anyone who wants to become a security professional or move into cyber security.
What this book covers Chapter 1, Understanding Security Fundamentals, covers some security fundamentals that
will be expanded upon in later chapters.
Chapter 2, Conducting Risk Analysis, looks at the types of threats and vulnerabilities, and at
the roles that different threat actors play.
Chapter 3, Implementing Security Policies and Procedures, looks at reference architectures,
different guides, and how best to dispose of data.
Chapter 4, Delving into Identity and Access Management, looks at different types of
authentication and how to dispose of data. We will first look at the concepts of identity and access management. Chapter 5, Understanding Network Components, examines networking components and how
they could affect the security of your network. We will look at firewalls, switches, and routers.
Preface Chapter 6, Understanding Cloud Models and Virtualization, teaches about virtualization,
deployment, and security issues. We will get acquainted with various cloud models, looking at their deployment and storage environments.
Chapter 7, Managing Hosts and Application Deployment, looks at different mobile devices
and their characteristics, as well as the applications that run on these devices.
Chapter 8, Protecting Against Attacks and Vulnerabilities, explores attacks and vulnerabilities,
taking each type of attack in turn and examining its unique characteristics. This module is probably the most heavily tested module in the Security+ exam. Chapter 9, Implementing Public Key Infrastructure, gets into the different encryption types
and how certificates are issued and used.
Chapter 10, Responding to Security Incidents, deals with incident response, focusing on the
collection of volatile evidence for forensic analysis.
Chapter 11, Managing Business Continuity, turns its attention toward our business
environment to consider the provision of system availability, looking at selecting the most appropriate method for recovery following a disaster. Chapter 12, Mock Exam 1, includes mock questions, along with explanations, which will
help in assessing whether you're ready for the test.
Chapter 13, Mock Exam 2, includes more mock questions, along with explanations, which
will help in assessing whether you're ready for the test.
Appendix A, Preparing for the CompTIA Security+ 501 Exam, is included to help students pass
the Security+ exam first time.
Appendix B, Acronyms, contains full forms of the abbreviations used in all the chapters.
To get the most out of this book This certification guide assumes no prior knowledge of the product.
Download the color images We also provide a PDF file that has color images of the screenshots/diagrams used in this book. You can download it here: http://www.packtpub.com/sites/default/files/ downloads/9781789348019_ColorImages.pdf.
[2]
Preface
Conventions used There are a number of text conventions used throughout this book. CodeInText: Indicates code words in text, database table names, folder names, filenames,
file extensions, pathnames, dummy URLs, user input, and Twitter handles. Here is an example: "For example, if we take the word pass in plaintext, it may then be converted to UDVV; this way it is difficult to understand." Bold: Indicates a new term, an important word, or words that you see onscreen. For example, words in menus or dialog boxes appear in the text like this. Here is an example: "The most common asymmetric algorithms include the Diffie Hellman, which creates a secure session so that symmetric data can flow securely." Warnings or important notes appear like this.
Tips and tricks appear like this.
Get in touch Feedback from our readers is always welcome. General feedback: If you have questions about any aspect of this book, mention the book title in the subject of your message and email us at [email protected] Errata: Although we have taken every care to ensure the accuracy of our content, mistakes do happen. If you have found a mistake in this book, we would be grateful if you would report this to us. Please visit www.packt.com/submit-errata, selecting your book, clicking on the Errata Submission Form link, and entering the details. Piracy: If you come across any illegal copies of our works in any form on the Internet, we would be grateful if you would provide us with the location address or website name. Please contact us at [email protected] with a link to the material. If you are interested in becoming an author: If there is a topic that you have expertise in and you are interested in either writing or contributing to a book, please visit authors.packtpub.com.
[3]
Preface
Reviews Please leave a review. Once you have read and used this book, why not leave a review on the site that you purchased it from? Potential readers can then see and use your unbiased opinion to make purchase decisions, we at Packt can understand what you think about our products, and our authors can see your feedback on their book. Thank you! For more information about Packt, please visit packt.com.
[4]
1 Understanding Security Fundamentals In this chapter, we will look at a number of security fundamentals; some of these will be expanded upon in later chapters. For the exam, you will need to know all of the information in this book as the exam is fairly tricky. We will cover the following exam objectives in this chapter: Explaining the importance of physical security controls: Lighting—signs—fencing/gate/cage—security guards—alarms—safe—secure cabinets/enclosures—protected distribution/protected cabling—Airgap—Mantrap—Faraday cage—lock types—biometrics—barricades/bollards—tokens/cards—environmental controls—HVAC—hot and cold aisles—fire suppression—cable locks—screen filters—cameras—motion detection—logs—infrared detection—key management Given a scenario, implement identity and access management controls: Access control models—MAC—DAC—ABAC—role-based access control—rule-based access control—physical access control—proximity cards—smart cards Comparing and contrasting various types of controls: Deterrent—preventive—detective—corrective—compensating—technic al—administrative—physical Explaining cryptography algorithms and their basic characteristics: Hashing algorithms—MD5—SHA—HMAC—RIPEMD
Understanding Security Fundamentals
Chapter 1
CIA triad concept Most security books start with the basics of security by featuring the CIA triad—this is a model designed to guide policies for information security within an organization. It is a widely used security model and it stands for confidentiality, integrity, and availability, the three key principles that should be used to guarantee having a secure system:
Figure 1: CIA triad
We'll discuss these principles in more depth here:
Confidentiality: Prevents the disclosure of data to unauthorized people so that only authorized people have access to data—this is known as the need to know basis. Only those who should know the contents should be given access. An example would be that your medical history is only available to your doctor and nobody else. We also tend to encrypt data to keep it confidential. Integrity: This means that you know that data has not been altered or tampered with. We use a technique called hashing that takes the data and converts it into a numerical value. If you run the hash when you suspect changes have taken place, and if the numerical value has changed, then the data has been tampered with. Common hashing algorithms in the exam are Secure Hash Algorithm version 1 (SHA1) and Message Digest version 5 (MD5). Availability: Ensures that data is always available; if you wanted to purchase an airplane ticket and the system came back with an error and you could not purchase it, this could be frustrating.
[6]
Understanding Security Fundamentals
Chapter 1
Identifying security controls There are a wide variety of different security controls that are used to mitigate the risk of being attacked; the three main security controls are technical, administrator, and physical. In this section, we are going to look at these in more detail; you need to be familiar with each of these controls and when each of them should be applied. Let's start by looking at the three main controls.
Administrative controls Administrative controls are mainly written by managers to create organizational policies to reduce the risk within companies. An example could be an internet use policy so that the employees realize that the internet can only be used for company business and not used for social media during the working day. Another administrative control would be completing a form if you want to apply for a holiday; the form would be available from the forms library. Administrative controls could be writing a policy, completing a form, and getting your ID badge re-keyed annually.
Some of the administrative measures are as follows: Annual security awareness training: This is an annual event where you are reminded about what you should be doing on a daily basis to keep the company safe. An example would be when you are finished for the day that you clear your desk and lock all documents away; another would remind you that your identity badge should be worn at all times and you should challenge anyone not wearing a badge. Another example is that companies now need their employees to complete cyber security training as the risk is getting greater each day. Annual risk assessment: A company will have a risk register where the financial director will look at all of the risks associated with money and the IT manager will look at all of the risks posed by the IT infrastructure. As technology changes and the hackers get more sophisticated, the risks can become greater.
[7]
Understanding Security Fundamentals
Chapter 1
Penetration testing/vulnerability scanning: A vulnerability scan is not intrusive as it merely checks for vulnerabilities, whereas a penetration test is more intrusive and can exploit vulnerabilities. These will be explained further into this book. Change management: This is a process that a company adopts so that changes don't cause any security risks to the company. A change to one department could impact another department. The Change Advisory Board (CAB) assists with the prioritization and priority of changes; they also look at the financial benefits of the change and they may accept or reject the changes proposed for the benefit of the company. Information technology (IT) evolves rapidly and our processes will need to change to cope with potential security risks associated with newer technology.
Technical controls Technical controls are those implemented by the IT team to reduce the risk to the business. These could include the following: Firewall rules: Firewalls prevent unauthorized access to the network by IP address, application, or protocol. These are covered in depth later in this book. Antivirus/antimalware: This is the most common threat to the business and we must ensure that all servers and desktops are protected and up to date. Screen savers: These log computers off when they are idle, preventing access. Screen filters: These prevent people walking past from reading the data on your screen. Intrusion Prevention Systems (IPS)/Intrusion Detection Systems (IDS): The intrusion detection system monitors the network for any changes and the intrusion prevention system stops the attacks. Technical controls could be installing a screensaver or configuring firewall rules.
[8]
Understanding Security Fundamentals
Chapter 1
Physical controls Physical controls are controls that you can touch, for example: Cable locks: These are attached to laptops to secure them so that nobody can steal them. Laptop safe: Laptops and tablets are expensive, but the data they hold could be priceless, therefore there are safes for the storage of laptops and tablets. Biometric locks: Biometrics are unique to each person; examples would be using their fingerprint, voice, an iris scanner, or facial recognition. Fences/gates: The first line of defense should be a perimeter fence as the openness of many sites renders them highly vulnerable to intruders. Access to the site can be controlled by using a gate either manned by a security guard or with a proximity reader. A timber fence does not provide as much protection as a high steel fence. Burglar alarms: These are set when the premises is not occupied, so when someone tries to break into your premises, it will trigger the alarm and notify the monitoring company or local police. Fire alarms/smoke detectors: In a company, there will be fire alarms or smoke detectors in every room so that when a fire breaks out, and the alarms go off, the people inside the premises are given the opportunity to escape. Lighting: Lighting is installed for two main reasons: the first reason is so that anyone trying to enter your site at night can be seen and the second reason is for safety. Security guards: They check the identity cards of people entering the building to stop unauthorized access. This also helps deter people trying to enter a building illegally. Mantraps: These are turnstile devices that only allow one person in at a time. They maintain a safe and secure environment mainly for a data center. A data center hosts many servers for different companies. Perimeter protection: Fences, gates, and lights could protect the perimeter of your company. We could place bollards in front of a building to stop a car driving through the entrance. These normally protect ATM cash machines from being hit by a vehicle. Internal protection: We could have safes and secure enclosures; the first example would be a toughened glass container or a sturdy mesh, both with locks to reduce access. We could also have protected distribution for cabling; this looks like metal poles that would have network cables inside. Screen filters used on a desktop could prevent someone from reading the screen.
[9]
Understanding Security Fundamentals
Chapter 1
Faraday cage: This is a metal structure, like a metal mesh used to house chickens. The cage prevents wireless or cellular phones from working inside the company. This could be built into the structure of a room used as a secure area. Key management: This is where departmental keys are signed out and signed back in daily to prevent someone taking the keys away and cutting copies of them. Proximity card: These are contactless devices where a smart card or token is put near the proximity card to gain access to a door or building. Tokens: Tokens are small physical devices where you either touch the proximity card to enter a restricted area of a building. Some tokens allow you to open and lock doors by pressing the middle of the token itself; others display a code for a number of seconds before it expires. Environmental controls: Heating, ventilation, and Air-Conditioning (HVAC), and fire suppression systems, are also security controls. In a data center or a server room, the temperature needs to be kept cool or the servers inside will overheat and fail. HVAC systems help provide availability to servers in the data center, ensuring they don't overheat.
AirGap: This is where a device is on your network, but it has a device between it and the other devices on your network. For example, you may want to isolate a computer that can complete a BACS transfer from the other computers in the finance department. Motion detection/cameras: These could be deemed physical controls, but the exam is focused on these being deterrent controls. Log files also note the events and could also be deemed a physical control, but the exam deems them to be detective controls. Barricades: Barricades can be erected across roads to stop traffic entering your site, but will not stop someone getting out of a car and jumping over them. You will need to use them in conjunction with security guards to fully protect your site. Bollards: Bollards are becoming very common as they control access by cars and stop them ramming through a front door. They stop ram raiders from stealing a cash machine or crashing into a jeweler's shop. They can be made from steel or concrete and are placed about four feet apart. In some countries, they are installed to prevent car bombers driving their vehicle into a group of people, maybe inside a shopping mall.
[ 10 ]
Understanding Security Fundamentals
Chapter 1
Preventative controls Preventative controls are in place to deter any attack; this could be having a security guard with a large dog walking around the perimeter of your company. This would make someone trying to break in think twice. Some of the preventive measures that are taken are as follows: Disable user accounts: When someone leaves a company, the first thing that happens is that their account is disabled, as we don't want to lose information that they have access to, and then we change the password so that they cannot access it. We may disable an account while people are on secondment or maternity leave. Operating system hardening: This makes a computer's operating system more secure. It often requires numerous actions such as configuring system and network components properly, turning off features and services that it does not use, and applying the latest software and antivirus updates.
Deterrent controls Deterrent controls could be CCTV and motions sensors. When someone is walking past a building and the motion sensors detect them, it turns lights on to deter them. A building with a sign saying that it is being filmed with CCTV prevents someone from breaking into your premises, as they think they are being filmed, even though there may not be a camera inside—but they don't know that. CCTV and motion sensors as deterrents. CCTV is a form of detective control following an incident, where you review the footage to see how the incident happened.
Detective controls Detective controls are used to investigate an incident that has happened and needs to be investigated; these could include the following: CCTV records events as they happen and from that you can see who has entered a particular room or has climbed through a window at the rear of a building.
[ 11 ]
Understanding Security Fundamentals
Chapter 1
Log files are text files that record events and the times that they occurred; they can log trends and patterns over a period of time. For example, servers, desktops, and firewalls are all events. Once you know the time and date of an event, you can gather information from various log files.
Corrective controls Corrective controls are the actions you take to recover from an incident. You may lose a hard drive that contained data; in that case, you would replace the data from a backup you had previously taken. Fire-suppression systems are another form of corrective control. You may have had a fire in your data center that has destroyed many servers, therefore when you purchase a replacement, you may install an oxygen suppressant system. This method uses argon/nitrogen and sometimes a small element of CO2 to displace the oxygen in the server room. The basis of this method is to reduce the oxygen level to below 15% because it will suppress a fire.
Compensating controls Compensating controls can be called alternative controls; this is a mechanism that is put in place to satisfy the requirements of a security measure that is deemed too difficult or impractical to implement at the present time. It is similar to when you go shopping and you have $100 in cash—once you have spent your cash, you will have to use a credit card as a compensating control. An example of this is where a new person has just been employed by the company, and the normal way to log in is to use a smart card and PIN. This resembles a bank card with a chip where you insert it into your laptop or keyboard and then insert a PIN to log in. Maybe it takes 3-5 days to get a new smart card, so during the waiting period, they may log in using a username and password:
[ 12 ]
Understanding Security Fundamentals
Chapter 1
Access controls The three main parts of access controls are identifying an individual, authenticating them when they insert a password or PIN, and then authorization, where an individual has different forms of access to different data. For example, someone working in finance will need a higher level of security clearance and have to access different data than a person who dispatched an order in finished goods: Identification: This is similar to everyone who has their own bank account; the account is identified by the account details on the bank card. Identification in a security environment may involve having a user account, a smart card, or maybe a fingerprint reader—this is unique to that individual. Authentication: Once the individual inserts their method of identification, they next to be authenticated, for example, by inserting a password or a PIN. Authorization: This is the level of access you have to selective data. You are normally a member of certain groups, for example, a sales manager could access data from the sales group and then access data from the managers group. You will only be given the minimum amount of access required to perform your job; this is known as least privilege.
Discretionary access control Discretionary access control involves New Technology File System (NTFS) file permissions, which are used in Microsoft operating systems. The user is only given the access that he/she needs to perform their job. The permissions are as follows: Full control: Full access Modify: Change data, read, and read and execute Read and execute: Read the file and run a program if one is inside it List folder contents: Expand a folder to see the subfolders inside it Read: Read the contents Write: Allows you to write to the file Special permissions: Allows granular access; for example, it breaks each of the previous permissions down to a more granular level
[ 13 ]
Understanding Security Fundamentals
Chapter 1
Data creator/owner: The person that creates the unclassified data is called the owner and they are responsible for checking who has access to that data:
Least privilege Least privilege is where you give someone only the most limited access required so that they can perform their job role; this is known as need to know basis. The company will write a least privilege policy so that the administrators know how to manage it.
[ 14 ]
Understanding Security Fundamentals
Chapter 1
Mandatory access control Mandatory Access Control (MAC) is based on the classification level of the data. MAC looks at how much damage they could cause to the interest of the nation. These are as follows: Top secret: Highest level, exceptionally grave damage Secret: Causes serious damage Confidential: Causes damage Restricted: Undesirable effects Examples of Mandatory Access Control (MAC) are as follows: Data types Nuclear energy project Research and development Ongoing legal issues Government payroll
Classification Top secret Secret Confidential Restricted
These are the roles: Custodian: The custodian is the person who stores and manages classified data. Security administrator: The security administrator is the person who gives access to classified data once clearance has been approved. Security enhanced Linux: SELinux is a project that was created with the intention of providing stricter security measures for access control and user permits, processes, files, and devices in Linux systems. The National Security Agency (NSA) in the United States published this as open code under the GNU PNL license. This project was integrated into Linux's (LSM) security modules from the 2.6.0 version of the Linux kernel that was published in 2003.
Linux permissions (not SELinux) File permissions: Linux permissions come in a numerical format; the first number represents the owner, the second number represents the group, and the third number represents all other users: Permissions:
Owner: First number Group: Second number All other users: Third number
[ 15 ]
Understanding Security Fundamentals
Chapter 1
Numerical values: 4: Read (r) 2: Write (w) 1: Execute (x) Unlike a Windows permission that will execute an application, the execute function in Linux allows you to view or search. A permission of 6 would be read and write. A value of 2 would be write, and a value of 7 would be read, write, and execute. Some examples are as follows: Example 1: If I have 764 access to File A, this could be broken down as: Owner: Read, write, and execute Group: Read All other users: Read Example 2: Determine which of the following permissions to File B is the highest and which is the lowest: 776 File B, also shown as _rwx _rwx _rw 677 File B 777 File B 577 File B 576 File B When selecting the highest, you look at the value on the left, therefore the highest is the value of 777, which is full control. When selecting the lowest, you look at the lowest value on the left. There are two options here: d and e start with the lowest number, and then you look at the others. From here, you can see that answer e is the lowest. The higher the number, the higher the permissions; the lowest number is the one with the least permissions.
You can also change permissions in Linux: If permissions to File C is 654 and we wish to change these permissions, we will run the Chmod 777 File A command, which changes the permissions to File C.
[ 16 ]
Understanding Security Fundamentals
Chapter 1
Role-based access control This is a subset of duties within a department. An example would be two people with the finance department who only handle the petty cash. In IT terms, it could be that only two of the IT team administer the email server.
Rule-Based Access Control In Rule-Based Access Control (RBAC), a rule is applied to all of the people within, for example, contractors will only have access between 8 a.m. and 5 p.m., and the help desk people will only be able to access Building 1, where their place of work is. It can be timebased or have some sort of restriction, but it applies to the whole department.
Attribute-based access control In Attribute-Based Access Control (ABAC), access is restricted based on an attribute in the account. John could be an executive and some data could be restricted to only those with the executive attribute.
Group-based access To control access to data, people may be put into groups to simplify access. An example would be if there were two people who worked in Information Technology (IT) who needed access to older IT data. These people are called Bill and Ben:
Everyone in the sales team may have full control of the sales data by using group-based access, but you may need two new starters to have only read access. In this case, you would create a group called new starters and give those people inside that group only read permission to the data.
[ 17 ]
Understanding Security Fundamentals
Chapter 1
If access to data is done via group-based access, then any solution in the exam will be a group-based answer.
Hashing and data integrity Hashing: It is where the data inside a document is hashed using an algorithm such as Secure Hash Algorithm version 1 (SHA1) and Message Digest version 5 (MD5). This turns the data inside the file into a long text string known as a hash value; this is also known as a message digest. Hashing the same data: If you copy a file and therefore have two files containing the same data, and if you hash them with the same hashing algorithm, it will always produce the same hash value. Verifying integrity: During forensic analysis, the scientist takes a copy of the data prior to investigation. To ensure that he/she has not tampered with it during investigation, he/she will hash the data before starting and then compare the hash to the data when he/she has finished. If the hash matches, then we know that the integrity of the data is intact. One-way function: For the purpose of the exam, hashing is a one-way function and cannot be reversed. HMAC authentication: In cryptography, an HMAC (sometimes known as either keyed-hash message authentication code or hash-based message authentication code) is a specific type of Message Authentication Code (MAC) involving a cryptographic hash function and a secret cryptographic key. We can have HMAC-MD5 or HMAC-SHA1; the exam provides both data integrity and data authentication. Digital signature: This is used to verify the integrity of an email so that you know it has not been tampered with in transit. The private certificate used to sign the email that creates a one-way hash function and when it arrives at its destination the recipient has already been given a public key to verify that it has not been tampered with in transit. This will be covered in more depth later in this book. Can you read data that has been hashed? Hashing does not hide the data as a digitally signed email could still be read—it only verifies integrity. If you wish to stop someone reading the email in transit, you need to encrypt it.
[ 18 ]
Understanding Security Fundamentals
Chapter 1
RACE Integrity Primitives Evaluation Message Digest (RIPEMD): This is a 128-bit hashing function. RIPEMD (https://en.wikipedia.org/wiki/RACE_ (Europe) has been replaced by RIPEMD-160, RIPEMD-256, and RIPEMD-320. For the purpose of the exam, you need to know that it can be used to hash data.
Hash practical The reason that we hash a file is to verify its integrity so that we know if someone has tampered with it.
Hash exercise In this exercise, we have a file called data.txt. First of all, I use a free MD5 hashing tool and browse to the data.txt file, which generates a hash value. I have also created a folder called Move data to here: 1. Get the original hash:
[ 19 ]
Understanding Security Fundamentals
Chapter 1
2. Copy the hash from the current hash value to the original hash value. 3. Copy the data.txt file to the Move data to here folder, then go to the MD5 hash software and browse to the data.txt file in the new location, and press verify. The values should be the same as shown here:
The values are the same, therefore we know the integrity of the data is intact and it has not been tampered with when moving the readme.txt file. 4. Next, we go into the data.txt file and change a single character, add an extra dot at the end of a sentence, or even enter a space that cannot be seen. We then take another hash of the data and we will then see that the hash value is different and does not match; this means that the data has been tampered with:
[ 20 ]
Understanding Security Fundamentals
Chapter 1
Defense in depth model Defense in depth is the concept of protecting a company's data with a series of defensive layers so that if one layer fails, another layer will already be in place to thwart an attack. We start with our data, then we encrypt it to protect it: The data is stored on a server The data has file permissions The data is encrypted The data is in a secure area of the building There is a security guard at the building entrance checking identification There is CCTV on the perimeter There is a high fence on the perimeter
[ 21 ]
Understanding Security Fundamentals
Chapter 1
Therefore, before someone can steal the data, they have seven layers of security that they must pass through. The concept of defense in depth is that if one layer fails, then the next layer protects:
Review questions 1. 2. 3. 4. 5. 6. 7. 8.
What are the three components of the CIA triad? Why might a CCTV camera be sited outside a building without any film inside? What does confidentiality mean? How can we protect a data center from people entering it? What is the purpose of an airgap? Name three administrative controls. Name three physical controls. Following an incident, what type of control will be used when researching how the incident happened? 9. How do I know if the integrity of my data is intact?
[ 22 ]
Understanding Security Fundamentals
Chapter 1
10. What is a corrective control? 11. What is the purpose of hashing? 12. If I hash the same data with different SHA1 applications, what will the output be? 13. What two things does HMAC provide? 14. What type of control is it when I change the firewall rules? 15. What is used to log in to a system that works in conjunction with a PIN? 16. What is the name of the person who looks after classified data and who is the person that gives people access to the classified data? 17. When you use a DAC model for access, who determines who gains access to the data? 18. What is least privilege? 19. What access control method does SELinux utilize? 20. What is the Linux permission of 777? What access does it give you? 21. What does the Linux permission execute allow me to do? 22. The sales team are allowed to log in to the company between 9 a.m. and 10 p.m. What type of access control is being used? 23. Two people from the finance team are only allowed to authorize the payment of checks; what type of access control are they using? 24. What is the purpose of the defense in depth model? 25. When someone leaves the company what is the first thing we should do with their user account?
[ 23 ]
Understanding Security Fundamentals
Chapter 1
Answers and explanations 1. Confidentiality means only allowing those authorized to access data. Integrity means that data has not been tampered with. Availability means that data is available when you need it, for example when purchasing an airline ticket. 2. We could place a CCTV camera in a prominent location as a deterrent; people walking past cannot tell if it has film or not, so we are using it as a deterrent. 3. Confidentiality means that we are limiting access to data to only those who should have access. 4. To stop people entering a data center, we would install a mantrap, a turnstile device, so that we can control who accesses the data center, one at a time. 5. An airgap is what it says on the tin, it is a gap between your network and a machine. A user would use an airgap maybe between Research and Development Machine and the corporate network. 6. Administrative controls could be writing a new policy to make the company run smoothly; we may have just implemented change management. You could implement a new form to ensure that all of the data required for an application is supplied. We could run an annual security awareness training day, complete a risk assessment, or perform penetration testing. 7. Physical control is huge. Remember that these can be physically touched. You can choose three from: cable locks, laptop safe, biometric locks, fences, gates, burglar alarms, fire alarms, lights, security guards, bollards, barricades, a Faraday cage, key management, proximity cards, tokens, HVAC, an airgap, motion sensors, and cameras and biometric devices such as an iris scanner. 8. If we investigate an incident, we need to collect all of the facts about the incident; this is a detective control. Think of a detective such as Sherlock Holmes who is always investigating mysteries. 9. If we hash the data before and after, and the hash value remains the same, then the integrity of the data is intact. If the second hash is different, the data has been tampered with. 10. Corrective control is a one-way function where an incident has happened and we want to redeem the situation. For example, if the hard drive on my laptop fails, then I will purchase a new hard drive, put it into my laptop, install the operating system and application, then obtain a copy of my data from a backup.
[ 24 ]
Understanding Security Fundamentals
Chapter 1
11. Hashing is a technique that lets you know if data has been tampered with, but it does not hide the data. 12. If the same data is hashed with two different applications that can hash data with SHA1, then the hash value will be the same. 13. HMAC provides data integrity and data authentication. You can use HMACSHA1 or HMAC-MD5. 14. If I change firewall rules, I am doing this to reduce risk; it is carried out by administrators, therefore it is a technical control. 15. A smart card is a credit card-type device that has a chip built in; once inserted into the keyboard or USB card reader, you will then be asked to enter a PIN. 16. The person who stores and manages classified data is called the custodian. The person who gives access to the classified data is the security administrator. Prior to getting access to the data, the person may well be vetted. 17. In the DAC model, the data is unclassified and the data creator, who is also called the owner, will decide who gains access to the data. 18. Least privilege is a technique that says that people should only get the most limited access to data that they need to perform their job. 19. SELinux uses the MAC model to access data. This is the secure version of Linux. 20. In Linux 777, give the owner who is the first digit, the group that is the sent digit and all users who are the third group read, write, and execute. It could also be a rwx. 21. The Linux permission for execute (x) allows you to search for or view data. 22. An access control method that applies either a time restriction or location restriction is called rule-based access. 23. A subset of a department with access to a subset of duties is called role-based access. 24. The defense in depth model has many different layers; the idea behind this is if one layer is broken through, the next layer will provide protection. 25. When someone leaves the company, we should disable their account so that the keys associated with it are still available. The next stage is to change the password so nobody can access it, especially the person who has just left.
[ 25 ]
2 Conducting Risk Analysis As a security professional, you will need to understand that identifying and managing risks can help to keep your company's environment safe from various types of attacks. In this chapter, we will look at types of threats and vulnerabilities and the roles that different threat actors play. We will cover the following exam objectives in this chapter: Explain threat actor types and attributes: Types of actors: script kiddies—hacktivists—organized crime—nation states/APT—insiders—competitors. Attributes of actors: internal/external—level of sophistication—resources/funding—intent/motivation. Use of open source intelligence Explain the importance of policies, plans, and procedures related to organizational security: Standard operating procedure—agreement types—BPA—SLA—ISA—MOU/MOA. Personnel management: mandatory vacations—job rotation—separation of duties—clean desk—background checks—exit interviews—role-based awareness training—continuing education—acceptable use policy/rules of behavior—adverse actions. General security policies: social media networks/applications—personal email. Summarize business impact analysis concepts: RTO/RPO—MTBF—MTTR—mission-essential functions—identification of critical systems—impact—life—property—safety—finance—reputation. Privacy impact assessment—privacy threshold assessment.
Conducting Risk Analysis
Chapter 2
Explain risk management processes and concepts: Threat assessment: environmental—manmade—internal versus external. Risk assessment: SLE—ALE—ARO—asset value—risk register—likelihood of occurrence—supply chain assessment—impact—quantitative—qualitative. Testing: penetration testing authorization—vulnerability testing —authorization. Risk response techniques: accept—transfer—avoid—mitigate.
Risk management Risk management is the process of identifying risks within a company and making decisions about how to reduce the risks so that an incident does not cause harm to the company and its assets. You may not be able to eliminate the risk completely, but you may be able to put procedures in place to reduce it or keep it an acceptable level. The first step in risk management is to identify the asset. Is it a top-secret document? If that was the case you'd limit access to the document. The top-secret document would be stored in a secure area at all times; nobody would be able to take copies or photographs of it. For example, if you had 1 kg of trash and you placed it outside your front door at night, you would be certain that in the morning it would still be there; however, if the asset was 1 kg of 24-carat gold and you left it outside your house at night, it would probably not be there in the morning. The first step in risk management is identifying the asset, because how we classify the asset will determine how the asset is handled, stored, protected, and who has access to it.
Importance of policy, plans, and procedures Creating policies, plans, and procedures is a part of risk management and helps to reduce the attack surface and prevent incidents from happening. Let's look at the different type of policies that can be used.
[ 27 ]
Conducting Risk Analysis
Chapter 2
Standard operating procedures Standard operating procedures (SOP) give us step-by-step instructions about how an activity is to be carried out. An example would be how to back up data. The SOP will state which data needs to be backed up daily, weekly, or monthly. Critical data would be backed up every two hours, whereas archive data may be backed up monthly. The SOP would also state the medium to be used for the backup; it may be backed up to a NetApp or network share rather than to tape so that quicker recovery can be carried out. Stage one in risk assessment is the classification of the asset; this then determines how it is accessed, stored, and handled.
Agreement types Contracts between companies that want to purchase or sell services are very common as they protect both partners participating in the contract. We will now look at different agreement types that may be used in those contracts: Business Partnership Agreement (BPA): A BPA is used between two companies who want to participate in a business venture to make a profit. It sets out how much each partner should contribute, their rights and responsibilities, the rules for the day-to-day running of the business, who makes the decisions, and how the profits are agreed and shared. It also has rules for the partnership ending either over time or if one of the partners dies. Service-Level Agreement (SLA): A SLA is a contract between a service provider and a company receiving the service that defines the level of service expected from the service provider; it is based on metrics within a specific time frame. The agreement can be either a fix or a response over a certain period of time. SLA is measure in metrics, as to what percentage has been achieved.
[ 28 ]
Conducting Risk Analysis
Chapter 2
For example, your company has an SLA with a service provider that will fix your printer within 4 hours. If the printer breaks down then the service provider needs to repair the printer within four hours or face a penalty. An SLA only relates to one product or service at one time. A company may have several SLAs in place that cover all of their equipment: Interconnection Security Agreement (ISA): An ISA states how connections should be made between two business partners. If one of the business partners is a government agency and the connection agreement is not enforced, it could pose a security risk to their network. The connection agreement could specify which type of VPN and tunnel should be used or it could state that a dedicated T3 line is used to make the connection between them. Memorandum of Understanding (MOU): An MOU is a formal agreement between two or more parties. MOUs are stronger than a gentlemen's agreement and both parties must be willing to make a serious commitment to each other, but they are not legally binding. Memorandum of Agreement (MOA): An MOA is similar to an MOU but serves as a legal document and describes the terms and details of the agreement. Non—Disclosure Agreement (NDA): An NDA is a legally binding contract made between an employee or a business partner where they promise not to disclose trade secrets to others without proper authorization. The reason for this is to stop trade secrets or proprietary information being sold on to competitors.
Personnel management—policies and procedures Employing personnel is a key function in a successful business; however, employing people is high risk as we need to employ the right type of person, who must be bright enough to identify cyber-crime attacks. To help reduce the risk that employees face or to prevent human resources from employing the wrong person and prevent fraud on an ongoing basis, the following policies can be adopted: Job rotation: Job rotation is used for two main reasons—the first is so that all staff can be trained in all aspects of the jobs in the company. Employees may change departments every six months; this way, they get fully trained. The second reason is that by rotating jobs, any theft or fraudulent activities can be discovered by the new person coming in.
[ 29 ]
Conducting Risk Analysis
Chapter 2
Mandatory vacations: Mandatory vacation helps detect whether an employee has been involved in fraudulent activities by forcing them to take holidays of a week or more. When people are involved in fraudulent activities they tend not to take many holidays so that the fraud cannot be discovered. This is especially rife in jobs in which people have fiscal trust, such as someone working in finance or someone who can authorize credit card payments. Separation of duties: Separation of duties is having more than one person participate in completing a task; this is internal control to prevent fraud or error. An example would be where a person who worked in the finance department collected all money being paid in and then authorized all payment being payed out. A charity in the United Kingdom was defrauded out of £1.3 million over a period of six years. If they had two distinct finance jobs, where one person received the money and another authorized payments, the fraud would have been prevented. This is the aim of separation of duties: no one person does the whole task. Let's look at an example. All members of the IT team can make any changes to the network firewall; this creates a huge risk to the network. An auditor could recommend that each time a firewall rule is changed it is authorized by the Change Advisory Board and two people should be responsible for checking the changes to the firewall. With two people being responsible for making the changes, any errors should be eliminated. This is an example of separation of duties. Let's look at a second example. When I first got married, we opened a joint back account that only my wages were paid into. My wife spent money from this account even though she had her own account. I paid in, my wife withdrew—a true separation of duties. Nowadays I have my own account! Separation of duties is where one person does not complete all configuration or transactions by themselves.
[ 30 ]
Conducting Risk Analysis
Chapter 2
Other policies adopted by the company to help reduce risk are as follows: Clean desk policy: A clean desk policy (sometimes known as clear desk policy) is a company policy that specifies that employees should clear their desks of all papers at the end of the day. This prevents the cleaning staff or anyone else from breaking into the building and reading those papers. Background checks: Completing background checks on new employees may involve looking into criminal records, employment and education history, and driving license and credit checks. This is to ensure that what the person has stated on their CV (resume) is correct. More stringent background checks are needed for those working with children and handling finance. Exit interview: The purpose of an exit interview is to find out the reason behind why the employee has decided to leave; this can be used to improve employment retention. Acceptable User Policy (AUP): The purpose of the AUP is to let the employee or contractor know what they can do with company computers and Bring Your Own Device (BYOD) devices. It lays out the practices relating to how you can access the company network and the internet. It will also state practices that are forbidden, such as using in blogs and social media sites such as Facebook or Twitter while at work. Rules of behavior: Rules of behavior lay down the rules of how employees should conduct themselves when at work. There should be no bullying, discrimination, or sexual harassment. Employees should work together for good and for the benefit of the company, even if they are not from the same background. People should respect and tolerate other employee's religious beliefs even though they may not be their own beliefs and they may not agree with them. Adverse action: Adverse action is action that is unlawful if it is taken for particular reasons. The fair work act defines a number of actions as adverse actions, such as a person threatening an employee, injuring them in their employment, or discriminating against them. Policy violations: When employees or contractors do not follow the policies or procedures that they have agreed to, this may result in either disciplinary procedures or, if serious, instant dismissal. This is normally behavioral based.
[ 31 ]
Conducting Risk Analysis
Chapter 2
Role-based awareness training Role-based awareness training is mandatory training that an employee carries out on an annual basis; an example of this would be security awareness training that is used by companies to reduce their security risks. During the training, employees will learn about social engineering attacks where the employee is targeted, for example, a phishing email. There will be more information about attacks in Chapter 8, Protecting Against Attacks and Vulnerabilities. Policy violation is where SOP and policies have been ignored. Transferring data from outside the company should be done via VPN.
General security policies General security policies affecting an employee using the internet are as follows: Social media networks/applications: Many people have social media accounts, such as Twitter, Facebook, Reddit, or Instagram. These sites store personal details about everyone who has an account, and employees need to be careful with the information that they post on these sites. For example, you could put your date of birth, where you live, your personal preferences, and your email address. This information is a security risk and it could lead to a phishing attack or identify theft. Cognitive hacking is where a computer or information system attack relies on changing human users' perceptions and corresponding behaviors in order to be successful. This is a social engineering attack and the information required could be found on your various social media websites or applications. You may also put comments on social media websites that could discredit your employer or one of their customers, and this could lead to dismissal. These comments may also prevent you from gaining future employment as employers normally complete a background check and also look at your social media accounts. If you have different social media sites, don't use the same password for each of them, especially if it is the same as your online banking account. One account hacked means that all accounts are hacked. Personal email: Your company mailbox must not be used for personal email. For example, if you decide to sell your car and then email all of the staff in the company, you will violate the Acceptable Use Policy.
[ 32 ]
Conducting Risk Analysis
Chapter 2
Business impact analysis concepts Business impact analysis (BIA) looks at the financial loss relating to an incident and does not look at how the threat or how an event occurred. It measures the additional cost due to various factors. Financial loss factors include the following: Loss and delay of sales Regulatory fines and contract penalties Purchase of new equipment to return to an operational state Additional labor required until returning to an operational state Do we need to seek a new property to operate in? Impact factors include the following: Loss of company brand or reputation Loss of life Were safety procedures in place? BIA looks at the financial loss but does not look at the threat.
Privacy threshold assessment/privacy impact assessment Personal data use, storage, and access are regulated, and a company will be fined if they do not handle data properly. There are two policies that we need to look at, and these are the privacy threshold assessment and the privacy impact assessment. Let's now look at these: Privacy threshold assessment: This assessment is to help identify personal information, described as either Personally Identifiable Information (PII), Sensitive Personal Information (SPI), or Public Health Information (PHI), as used in information security and privacy laws.
[ 33 ]
Conducting Risk Analysis
Chapter 2
Privacy Impact Assessment (PIA): A PIA is an analysis of how personally identifiable information is collected, used, shared, and maintained. Should you have a project that requires access to the PII, SPI, or PHI information, you may need to fill in a PIA screening form justifying the need for its use.
Mission-essential functions/identification of critical systems When we look at BIA as a whole we have to see what the company's mission-essential functions are; for example, an airline depends heavily on its website to sell airline tickets. If this was to fail it would result in loss of revenue. Critical systems for the airline would be the server that the website was placed on, as well as its ability to contact a backend database server, such as SQL, that holds ticketing information, processes the credit card transactions, and contains the order history for each of their customers.
Example What would be the mission-essential functions of a newspaper, and what would be its critical systems? Newspapers generate revenue not only via sales but more importantly by selling advertisement space in the paper. The mission-essential function would be the program that creates the advertisements, and the critical systems would be the server that the program resides upon, the database for processing payments, and the systems used to print the newspapers.
Supply chain risk assessment Your supply chain is the companies that you totally rely upon to provide the materials for you to carry out a business function or make a product for sale. Let's say that you are a laptop manufacturer and Company A provides the batteries and Company B provides the power supplies. If either of these runs short of either batteries or power supplies it stops you from manufacturing and selling your laptops.
[ 34 ]
Conducting Risk Analysis
Chapter 2
Example Company C provides your broadband internet access and you are totally reliant upon them for the internet—you may mitigate the risk of the internet failing by adopting vendor diversity, where you purchase broadband from Company D so that if either of your suppliers fails you still have internet access, which is now crucial to any modern business.
Business impact analysis concepts The following concepts are used to carry out the business impact analysis: Recovery Point Object (RPO): RPO is how much time a company can last without its data before it affects operations. This is also known as acceptable downtime; if a company agrees that it can be without data for three hours, then the RPO is three hours. If the IT systems in a company suffer a loss of service at 13:00 hours, then the RPO would be 16:00 hours. Any repair beyond that time would have an adverse impact on the business. Recovery Time Object (RTO): RTO is the time that the company has been returned to an operational state. In the RPO scenario, we would like the RTO to be before 16:00 hours. If the RTO is beyond 16:00 hours, then once again it has an adverse impact on the business. Mean Time to Repair (MTTR): MTTR is the average amount of time it takes to repair a system. If my car broke down at 14:00 hours and it was repaired at 16:00 hours the MTTR would be two hours. Mean Time Between Failures (MTBF): MTBF shows the reliability of a system. If I purchase a new car for $50,000 on January 1 then it breaks down on January 2, 4, 6, and 8, I would take it back to the garage as the MTBF would be pretty high and for $50,000, I want a car that is more reliable. Mean Time to Failure (MTTF): MTTF is the predicted lifespan of a system. Normally, an IT system is expected to last about five years, therefore its MTTF is five years. If I bought a car in 1960 and I had to scrap it in 1992, the MTTF of the car would be 32 years. RPO is the acceptable downtime, whereas RTO is the return to an operational state.
[ 35 ]
Conducting Risk Analysis
Chapter 2
Calculating loss The following concepts can be used to calculate the actual loss of equipment throughout the year and may be used to determine whether we need to take out additional insurance against the loss of the equipment: Single Loss Expectancy (SLE): The SLE is the loss of one item. For example, if my laptop is worth $1,000 and I lose it while travelling, then my SLE would be $1,000. Annual Rate of Occurrence (ARO): The ARO is the number of times that an item has been lost in a year. If an IT team loses six laptops in a year, the ARO would be six. Annual Loss Expectancy (ALE): The ALE is calculated by multiplying the SLE by the ARO—in the previous examples we have $1,000 x 6 =$6,000. The ALE is the total loss in a year.
Example A multinational corporation loses 300 laptops annually and these laptops are valued at $850; would they take out an insurance policy to cover the costs of replacement if the insurance premiums were $21,250 monthly? The answer is no, because the cost of replacing them is the same as the cost of the insurance. They would take a risk on not losing 300 laptops next year. The calculations are as follows: ALE: SLE x ARO ALE: $850 x 300 = $225,000 Monthly cost: $225,000/12 = $21,250 Annual loss expectancy = Single loss expectancy X Annual rate of occurrence.
[ 36 ]
Conducting Risk Analysis
Chapter 2
Risk procedures and concepts Risk is the probability that an event will happen—it could bring profit to you. For example, if you place a bet in roulette at a casino then you could win money. It is, however, more likely that a risk will result in financial loss or loss of service. Companies will adopt a risk management strategy to reduce the risk they are exposed to, but may not be able to eliminate the loss completely. In IT, new technology comes out every day and poses new risks to businesses, and therefore risk management is ever evolving. The main components are assets, risks, threats, and vulnerabilities: Asset: The first stage in risk management is the identification and classification of the asset. If the asset is a top-secret document, you will handle and store it differently than an asset that is unclassified and available for free on the internet. Risk: Risk is the probability that an event could occur, resulting in financial loss or loss of service. Threat: A threat is someone or something that wants to inflict loss on a company by exploiting vulnerabilities. It could be a hacker that wants to steal a company's data. Vulnerability: This is the weakness that help an attacker exploit a system. It could be a weakness in a software package or a misconfiguration of a firewall. A threat is something that will pose a danger by exploiting vulnerability. Vulnerability is a weakness that may be exploited, and risk is the probability that an event will happen.
Threat assessment A threat assessment helps a company classify its assets and then looks at the vulnerabilities of that asset. It will look at all of the threats the company may face, the probably of the threat happening, and the potential loss should the threat be successful: Environmental threat: This threat is based on environmental factors, for example, the likelihood of a flood, hurricane, or tornado. If you live in Florida there is a peak season for hurricanes from mid-August to October, whereas if you live in Scotland, the last time they had a minor hurricane was in 1968. Florida has a high risk of having a hurricane, whereas Scotland would be an extremely low risk. Man-made threat: This is a human threat—it could be a malicious insider attack where an employee deliberately deletes data, or could just be an accidental deletion by an incompetent member of staff.
[ 37 ]
Conducting Risk Analysis
Chapter 2
sdOffice - Synergetic Data Systems
 sdOffice ® Version 2.0 Copyright ©2007 by Synergetic Data Systems Inc. All rights reserved. sdOffice is a registered trademark of Synergetic Data Systems Inc. Other product names used in this document may be trademarks or registered trademarks of their respective owners. sdOffice 2.0 1 TABLE OF CONTENTS TABLE OF CONTENTS................................................................................................................ 2 INTRODUCTION .......................................................................................................................... 4 ARCHITECTURE .......................................................................................................................... 5 NETWORK SERVER INSTALLATION ...................................................................................... 6 Unix/Linux Server From Download ........................................................................................... 6 Unix/Linux Server from CD ....................................................................................................... 6 Windows Server.......................................................................................................................... 8 OFFICE CLIENT INSTALLATION ............................................................................................. 9 CONFIGURATION...................................................................................................................... 10 Unix Configuration ................................................................................................................... 10 Windows Configuration............................................................................................................ 12 LICENSING ................................................................................................................................. 13 Unix Licensing.......................................................................................................................... 14 Windows Licensing .................................................................................................................. 15 Activation Errors....................................................................................................................... 16 WINDOWS OFFICE CLIENT OVERVIEW .............................................................................. 17 Overview................................................................................................................................... 17 APPLICATION CLIENT INTERFACES.................................................................................... 18 Pre-defined Interfaces ............................................................................................................... 18 Default Rules for Client and Server Addresses ........................................................................ 18 Command Files - sdRun Interfaces........................................................................................... 20 Standard I/O - sdpipe.pl Interface............................................................................................. 22 BBx and ProvideX Interfaces ................................................................................................... 23 Print Preview – sdpreview.sh.................................................................................................... 27 Direct Interface Guidelines ....................................................................................................... 28 OBJECT REFERENCE ................................................................................................................ 30 Job Management ....................................................................................................................... 31 Command Usage and Parameters ......................................................................................... 31 Universal Commands................................................................................................................ 32 Command Usage and Parameters ......................................................................................... 32 Excel Object.............................................................................................................................. 40 Overview............................................................................................................................... 40 Command Usage and Parameters ......................................................................................... 41 Word Object.............................................................................................................................. 57 Overview............................................................................................................................... 57 Command Usage and Parameters ......................................................................................... 58 Outlook Object.......................................................................................................................... 69 Overview............................................................................................................................... 69 Command Usage and Parameters ......................................................................................... 69 MAPI Object............................................................................................................................. 77 sdOffice 2.0 2 Overview............................................................................................................................... 77 Commands and parameters ................................................................................................... 78 ADO Object .............................................................................................................................. 80 Overview............................................................................................................................... 80 Command Usage and Parameters ......................................................................................... 81 System Object ........................................................................................................................... 90 Mail Object ............................................................................................................................... 91 Overview............................................................................................................................... 91 Command Usage and Parameters ......................................................................................... 91 SAMPLES..................................................................................................................................... 95 Sample: ADO Database Manipulation...................................................................................... 96 Sample: Excel Calculation Engine............................................................................................ 97 Sample: Excel Formatting......................................................................................................... 98 Sample: Excel Report ............................................................................................................... 99 Sample: Excel Charting .......................................................................................................... 101 Sample: MAPI email submission............................................................................................ 102 Sample: Outlook Add Appointment ....................................................................................... 103 Sample: Outlook Add Contact ................................................................................................ 104 Sample: Outlook Email........................................................................................................... 105 Sample: Outlook Read Appointments .................................................................................... 106 Sample: Outlook Read Contacts ............................................................................................. 107 Sample: Word Document Formatting..................................................................................... 108 Sample: Word Mail Merge ..................................................................................................... 110 ADMIN CONNECTIONS.......................................................................................................... 112 OBJECT EXTENSIONS WITH VBSCRIPT............................................................................. 113 AUTOMATED FILE DISTRIBUTION..................................................................................... 116 APPENDIX................................................................................................................................. 118 Colors in Word and Excel....................................................................................................... 118 Paper Bins ............................................................................................................................... 119 Paper Sizes .............................................................................................................................. 120 sdOffice 2.0 3 INTRODUCTION sdOffice is a unique software tool that enables access to Microsoft Office® and other Windowsbased technologies from non-Windows systems and applications. Any application or computer that can interact with a TCP/IP socket or Unix/Linux pipe can now work with Microsoft Office and other products, using sdOffice as the bridge to the Component Object Model (COM) interfaces found in many Windows applications. COM is a method used in the Windows application world to treat programs, such as Microsoft Excel® and Microsoft Word®, as programmable objects from within other programs. This powerful facility is an important part of the Microsoft Windows® platform, but many legacy programming environments are not able to take advantage of it. In addition, many applications today run in Unix and Linux environments and have no direct way to access COM objects on Windows systems. sdOffice is the bridge that allows applications of any sort to work with the COM object model for Microsoft Office. sdOffice accepts commands from an application and translates them to the appropriate COM methods, allowing applications written in virtually any programming language, and running on virtually any operating system, to control programs like Excel and Word in real time with a comprehensive, extensible set of commands. As an example of the sort of capability that sdOffice provides, imagine the example of a traditional export to Excel procedure used by many legacy software users. In the original effort, the user runs a report that creates a tab-delimited or comma-separated-value text file. The user then copies the file to their PC, opens Excel, and imports the file. The columns in that file show up in the cells in Excel, and then the work begins. The user begins formatting the columns to match the data types and formats, adds column headings, inserts a formula column, adds column totals or maybe some grouped subtotals. After all this work, the Excel worksheet finally looks like a finished document. With sdOffice, that same report that started the whole process can export directly to Excel and perform every one of those formatting, formula, and totaling steps without any user intervention. With that sort of automated functionality, the application, rather than the user, performs all the work to produce the finished document, saving a tremendous amount of time. sdOffice is composed of several elements, which are described in the next chapter. sdOffice 2.0 4 ARCHITECTURE sdOffice is composed of three elements: An sdOffice Network Server Windows-based Office clients Application clients The heart of sdOffice is the Network Server. This software runs full time in background, optionally as a service under Windows, and as a daemon on Unix or Linux. The Network Server is the interface point for both Office clients and Application clients. The Office clients connect to the network server when they start up, and maintain a persistent connection while waiting for application clients to connect and initiate jobs. The Office client is the piece that translates commands into COM object methods. The Office client is similar to, but more powerful than, the old sdOffice 1.0 Windows client. The Application clients connect to the network server whenever a job needs to be executed on an Office client. The Application connects to the Network Server, specifies which client and which job object, and then begins sending commands. The Network Server routes the commands to the appropriate client, and returns responses back. Application clients include: The application software itself, if it can work with a TCP/IP socket A Perl-based pipe for applications that can use bi-directional pipes but not sockets sdRun executables (Perl-based on Unix/Linux, native on Windows) which process the commands from a text file BBx and ProvideX wrappers around the above features, providing a familiar CALL interface to programmers in those languages It is also possible to emulate an Application Client using Telnet, or by using the Application Connection window in the Office Client’s visual interface. sdOffice 2.0 5 NETWORK SERVER INSTALLATION Unix/Linux Server From Download 1. Login as root. 2. Create a directory to hold the sdOffice Server files, and change to that directory. Example: 3. umask 0 mkdir /usr/sdofc20 cd /usr/sdofc20 Uncompress and extract sdOffice from the download file. uncompress sdo20_xxx_tar.Z tar xvf sdo20_xxx_tar 4. Execute the set up script. ./sdsetup.sh The sdsetup.sh script will create a launch script called /usr/bin/sdo20d, used to start and stop the sdOffice Network Server. 5. Activate demo mode, or activate permanently, using ./license.sh. 6. Start the server: sdo20d start 7. Check the log file to verify operation: more sdo20d.log or tail sdo20d.log. See the Licensing section for activation information. Note that you will probably want to place the sdo20d start command in your system boot scripts, often found in the /etc/init.d directory or a similar location, depending on your version of UNIX. Unix/Linux Server from CD 1. Login as root. sdOffice 2.0 6 2. Mount the CD as a file system that supports lowercase file names. If you are unsure how to do this, check your man pages: man mount. The following table illustrates sample mount commands for various operating systems, assuming standard CD device names and that the mount directory /mnt is available. You may need to adjust these commands according to your configuration. SCO UNIX OS5 SCO UNIX Unixware AIX Sun Solaris HP/UX mount –o lower /dev/cd0 /mnt mount –r –f HS,lower /dev/cd0 /mnt mount –F cdfs –r /dev/cdrom/cdrom1 /mnt mount –vcdrfs –r /dev/cd0 /mnt mount –rt hsfs /dev/sr0 /mnt mount –r –F cdfs –o cdcase /dev/dsk/c1d0s2 /mnt 3. Change to the sdOffice 2.0 UNIX directory in the mount directory: cd /mnt/sdo20/unix 4. Run the install script: ./install.sh, or if you do not have execute permission to the file, sh install.sh. You must agree to the license agreement, then you will be presented a list of operating system versions. Choose the correct version for your system. 5. The sdOffice server will then be installed to the selected directory, and the set up script ./sdsetup.sh will be automatically executed in that directory. The sdsetup.sh script will create a launch script called /usr/bin/sdo20d, used to start and stop the sdOffice Network Server. 6. Activate demo mode, or activate permanently, using ./license.sh. 7. Start the server: sdo20d start 8. Check the log file to verify operation: more sdo20d.log or tail sdo20d.log. See the Licensing section for additional activation information. Note that you will probably want to place the sdo20d start command in your system boot scripts, often found in the /etc/init.d directory or a similar location, depending on your version of UNIX. sdOffice 2.0 7 Windows Server 1. From the CD, use Explorer to locate the D:\sdo20\win directory, and double-click the setup.exe program (use Control Panel Add/Remove Programs if the system supports Terminal Services). If you downloaded sdOffice from the Internet, simply execute the downloaded executable (use Control Panel Add/Remove programs if the system supports Terminal Services). Follow the on-screen prompts from the installer to install sdOffice to your system. This will install the sdo20d.exe server program, along with supporting files and the run-time engine, and create Start menu options under the title “sdOffice 2.0 Server”. 2. Click the Server Configuration option from the Start menu. This will conditionally rename certain files and prompt for several configuration values. The values entered are stored in the sdo20d.ini file. You can also use the Configure button from within the sdOffice Server Manager. 3. Click the Server Manager option from the Windows Start, Programs, sdOffice 2.0 Server menu. 4. Activate the demo mode, then if desired, activate permanently, by pressing the Licensing button and using the form that displays. On line help is available if needed. 5. Click the Start button from the Server Manager to start the server manually. 6. Check the log in the Server Manager to monitor operation. 7. If desired, and you are running the server on Windows NT, 2000, XP or any of the Windows variants that support NT Services, you can install the server as a service by running the Install as a Service option. When the sdOffice Server is run as a service, it is automatically started when Windows boots up. You must start and stop the service using the Windows Services applet, found in the Control Panel Administrative Tools option. The Server Manager options for starting and stopping the server are disabled. See the Licensing section for activation information. sdOffice 2.0 8 OFFICE CLIENT INSTALLATION The office client is a separate installation from the server. This Windows program should be installed on any workstation that will perform sdOffice jobs. Simply run the sdOffice2_setup.exe program. If you install it on a Windows system that supports Terminal Services, such as Windows 2003 Server, it must be installed using Control Panel, Add/Remove Programs while logged in as an administrator. This technique can be used in lieu of directly running the setup program on any system, but it is required in a server environment. Once installed and started, choose the Options tab to configure the Office Client. See the Office Client Overview chapter for more details. Automatic Configuration At the end of the setup execution, the setup program will look for the file “sdOffice2.ini” in the same path as sdOffice2_setup.exe. If found, that file will be used as the default configuration file. This procedure allows an administrator to configure one Office client installation normally, then copy the sdOffice2.ini file from his/her Office Client install path to the location where the sdOffice2_setup.exe program is normally installed from (or distribute the file with the setup.exe). Users will then get a default configuration, including server and port settings, automatically. sdOffice 2.0 9 CONFIGURATION Unix Configuration The network server is configured by editing the sdo20d.ini file. Here is an example file: [defaults] logfile=sdo20d.log logdetail=1 # client security is controlled as follows: # secure=0 unauthenticated, open (suggested for LAN only) # secure=1 authenticated connections but data sent in clear (VPN # or low-value data traffic) # secure=2 authenticated, SSL encrypted secure=0 refresh_manifiest=0 [clients] port=6115 allow=192.*.*.*;99.99.99.99 [apps] port=6114 allow=192.168.1.10;192.168.1.11 [admin] #uses apps port allow=127.0.0.1 The options for this file are defined below. logfile logdetail secure [defaults] section Connections, and optionally detail transaction data, are logged to this file. If set to 0, only connections are logged. If set to 1, transaction details are logged. If turned on, be sure to watch the size of the log file, and restart the Network Server periodically to reset the log. This value sets the security level for client connections, which often can come from remote systems across the Internet. There are three levels: 0 - Neither encryption nor authentication is performed on the socket. Note that all connection types are filtered by IP address to ensure only specific addresses can connect to the server. This option is sdOffice 2.0 10 typically all that is required on a local network, as long as the data that will be sent to clients is not highly sensitive. 1-Authentication only. No encryption is performed, but clients must authenticate themselves as valid sdOffice Office clients. 2-Authentication and encryption. Office Clients must authenticate themselves, plus all client traffic is encrypted using SSL. If the host system does not support SSL (i.e. the openssl libraries are not available), then this option will produce a startup error and the sdOffice Network Server will not start. jobhist This value controls the creation and purging of job history files. Job history files are placed in the jobhist directory under the server install directory. Each job’s commands are stored in a job history file, allowing for easy retrieval of jobs for analysis or debugging. Error messages returned by the client are entered into the job history file as a comment. The value is the number of days that job history files are retained. Anywhere from 0, meaning no job history files are created, to a fraction of a day or any number of days. refresh_manifest port allow port allow sdOffice 2.0 Jobhist=1 would keep job history files for 24 hours. Jobhost=.04167 would keep them for 1 hour. The job history files are named Sets the number of minutes between client re-processing of the manifest.txt file in the server “files” directory. Set to 0 to not refresh (the file will only be read as clients start up and connect to the server). This value should be an integer, and fractional minutes are rounded to the nearest integer. See the Automated File Distribution chapter for details. [clients] section The port on which the Network Server listens for Office client connections. This defaults to port 6115. If changed, Office clients must be configured to use the new port. A semi-colon delimited list of valid IP addresses or address wildcards for Office clients. Clients whose IP address is not in this list are denied access. Common address wildcards for local networks include 192.*.*.* and 10.*.*.*. [apps] section The port on which the Network Server listens for Application client connections. This defaults to port 6114. If changed, Application clients must use the new port. A semi-colon delimited list of valid IP addresses or address 11 wildcards for Application clients. Clients whose IP address is not in this list are denied access. allow Common address wildcards for local networks include 192.*.*.* and 10.*.*.*. [admin] section A semi-colon delimited list of valid IP addresses or address wildcards for admin connections. Connections from IP addresses not in this list are denied access. This is often set to the localhost address, 127.0.0.1, allowing admin access only from the network server host machine. Admin connections are initiated via the Application client port, typically via telnet, and the first command line sent is always “admin”. Admin connections provide several commands to manage the Network server. Windows Configuration On Windows, you can edit the sd20d.ini file just as on Unix, or you can use the sdOffice Server Manager and select the Configure button. The Configuration screen provides editing capabilities to many of sdo20d.ini settings. See the previous section for details about setting the various fields on this form, or view the online help. sdOffice 2.0 12 LICENSING Licensing for sdOffice is based upon the number of concurrent Application clients that will connect to the sdOffice Network Server. Application clients typically connect only long enough to run a job, from a few seconds to a few minutes, so the number of connection licenses required typically will be less than the number of active users on a network. The connection counts available are 1, 3, 5, 10, 15, 20, 25, 30, 40, 50, 75, 100, and unlimited. Each sdOffice Network Server is issued a unique serial number and two activation keys. One key enables the server itself, and is tied to the server’s system ID and machine class, both generated at the time of install. The other key enables the licensed number of Application connections. Licensing is controlled entirely by the sdOffice Network Server process, sdo20d. You can install the Application interfaces and Office clients freely anywhere on your network. Each sdOffice Network Server installation has a serial number. There is one special serial number, SD0099999, reserved for demo mode use on any machine. All permanent licenses are assigned a unique serial number and must be licensed to a single machine installation. Serial numbers and their associated PIN codes are assigned by SDSI when sdOffice is purchased. In order to obtain permanent or emergency temporary activation keys, the serial number and PIN code are required. There are two activation keys that must be entered for full operation of sdOffice: a system key and a connections key. The system key enables the sdOffice Network Server to operate on a specific computer. The connections key determines the number of concurrent Application connections that may run. For demo mode operation, just a temporary system key is required; demo mode operation automatically enables 3 Application connections. There are three types of system activation keys: 30-Day Demo This license has a fixed serial number (SD0099999) and can run on any machine for 30 days. While running under this serial number, sdOffice will print “*Demo*” phrases randomly in data sent to sdOffice clients. This is the first mode activated after an installation, as it enables the retrieval of a System ID and Machine Class needed for permanent licensing later, as well as allowing sdOffice to operate in demo mode. Permanent This license has an assigned serial number, and requires a System ID and Machine Class to activate. A permanent license does not expire, enabling the sdOffice Network Server to run perpetually on the machine where installed and licensed. The System ID is derived from a given installation machine and attributes of a file in the sdOffice rt\lib\keys directory (Windows) or the rt\lib directory (UNIX), so it will change if the installation is moved to a new machine, or even to a new location on the same machine. Once the System ID changes, the permanent activation key sdOffice 2.0 13 will no longer work, and sdOffice must be re-activated. If the original permanent installation of sdOffice is no longer used, then you can request a reset of the permanent license to enable a new System ID and Machine Class to be associated with the permanent activation key. Contact [email protected] to request resets. Emergency Temporary This license is assigned a serial number, like a permanent license, but it does not require a System ID or Machine Class to activate. This allows you to re-install the sdOffice Network Server on a different machine than originally licensed, and operate it for 30 days. Once a temporary license has been issued for a given serial number, another temporary license cannot be issued for 45 days. Unix Licensing To activate the sdOffice Network Server on UNIX, perform the following steps: Login as root. cd to the sdOffice directory (i.e. cd /usr/lib/sdsi/sdofc20). Execute ./license.sh. The license.sh script prompts for the following options: SDOFFICE LICENSING OPTIONS Use the following options if this machine is connected to the Internet: ----------------------------------------------------------------------1 - Permanent Activation (requires serial number and PIN code) 2 - Emergency Temporary Activation (also requires SN and PIN) 3 - 30-Day Demo Mode Activation Use the following options for manual activation. Activation keys can be obtained from http://synergetic-data.com/sd2lic.cgi. ----------------------------------------------------------------4 - Display System ID and machine class (needed for option 5) 5 - Enter Permanent Activation 6 - Enter Emergency Temporary Activation 7 - Enter 30-Day Demo Mode Activation q - quit Enter selection: To obtain either a permanent or emergency temporary activation, you will need to know your serial number and PIN code previously assigned by SDSI. These values are not necessary to obtain a 30-day demo mode activation. If your machine has Internet access, you can perform activation easily by choosing options 1 through 3. Options 1 and 2 will prompt you for your serial number and PIN. Each of the three options will use the Internet to retrieve the desired activation key. sdOffice 2.0 14 If the Internet is not available from the install machine, then you can perform activation manually by using another machine to visit http://synergetic-data.com/sd2lic.cgi. Use option 4 to display the System ID and Machine Class, which will be required to obtain a permanent activation key from this web site. Options 5 and 6 will prompt for a serial number, system key, and connections key, in sequence. Option 7 will only prompt for a system key. Windows Licensing The first step after an installation is to activate demo mode. This initializes the system ID file, enabling a permanent license to be obtained. If you get an error message after pressing the Show System ID button, then this installation has never been initialized, and you must activate demo mode first. To activate demo mode: If you are connected to the Internet, press the Automatic Demo Activation button. This will obtain a current demo mode activation key from SDSI's website and activate the run-time engine. If you are not connected to the Internet, go to a computer that is, and go to http://synergeticdata.com/sd2lic.cgi, then click the link to get a 30-day trial. Note the activation key returned, and enter it exactly the same way in the Demo Activation Key field, then click the Manual Demo Activation button. To verify the activation, click the Show System ID button. If the System ID and Class fields get filled in, then it worked. sdOffice 2.0 15 To activate permanent mode: To activate automatically over the Internet, you need to click the Show System ID button to get the System ID and Machine Class fields. Then fill in your serial number and PIN code, and click the Automatic Activation button. This will use your information to obtain a permanent activation key for the system, as well as your job and designer activation keys, and activate everything. To activate sdOffice manually, note your System ID and Machine Class, then go to http://synergetic-data.com/sd2lic.cgi. Enter your serial number and PIN code, then click the button to get a permanent license. When prompted, enter the System ID and Machine Class exactly as noted on this screen. Note the two activation keys returned, and enter them exactly as provided in the two entry fields, then click the Manual Activation button. To activate in emergency temporary mode: To obtain a temporary activation over the Internet or manually, follow the steps for a permanent license, but check the Emergency Temp Activation option. The System ID and Machine Class are not used for temporary activations. Activation Errors Permanent activation keys are dependent on the system ID and machine class information generated by an installation. Therefore, a permanent activation key will only work on the original installation for which it was generated. If the sdOffice Network Server needs to be moved or re-installed, a new permanent activation key must be generated. This is only possible if SDSI resets the permanent key for your serial number, so you must contact SDSI, certify that the original installation is no longer in use, and request a reset. In the meantime, you can obtain an emergency temporary activation to allow your serial number to be used on a new installation for 30 days. If you attempt to get a new permanent activation key and are notified that one has already been assigned, then contact SDSI to request a reset. If this cannot be done in a timely fashion, get an emergency temporary key instead, and then contact SDSI at a later time. Note that temporary keys are issued at most once every 45 days. If you get an error message indicating the temporary key availability has not expired, then you must contact SDSI to get a reset. sdOffice 2.0 16 WINDOWS OFFICE CLIENT OVERVIEW Overview The Office Client runs on Windows-based computers and executes the jobs routed to it from the sdOffice Network Server. This program provides the interface to Microsoft Office and other objects, by translating job command streams into COM object methods and properties. This program provides a user interface to view and edit job activity and configuration parameters. There is also a simple interface to test jobs on the client, without connecting to a Network Server and consuming application connection licenses. For details about this interface, consult the Help menu in the Office Client. sdOffice 2.0 17 APPLICATION CLIENT INTERFACES The basic principle behind any application client is to connect to the sdOffice Network Server, send an initialization command, and then begin sending commands for the job. The server parses the initialization command and attempts to link the Application client with an appropriate Office client. Pre-defined Interfaces Applications which use the pre-defined interfaces do not need to worry about the internal send and response formats used by the server. The pre-defined interfaces are: sdRun interfaces (sdrun.exe on Windows and sdrun.pl (Perl-based) on Unix/Linux). These interfaces submit a job command file, which is simply a text file containing the object and the commands to send to that object. sdpipe.pl, a Perl-based script designed to provide a standard I/O method of interfacing with the server, for application environments that can’t communicate directly with sockets. sdofc*.bb/sdofc*.pv, BBx and ProvideX callable programs designed for operation in those programming environments. sdpreview.sh, a Unix/Linux shell script designed to display a report print-preview on a user’s PC workstation, simply by printing to it. The script uses the sdrun.pl Perl script, so Perl is a prerequisite. In addition to these interfaces, any application that can communicate with the server via a TCP/IP socket (or the sdpipe.pl script) can connect and execute jobs by following the guidelines for connecting to the server and submitting jobs. These guidelines are described in the section titled Direct Interface Guidelines. Default Rules for Client and Server Addresses When an application wishes to start a job, it must connect to an sdOffice Network Server, and tell it what target sdOffice Client to send the job to. The application interfaces can be told explicitly what these values are, but there are other ways to specify the information. For the Network Server, the default address is ‘localhost’, and the default port is 6114. In order to specify a different default, you can establish an environment variable SDSERVER with the format server or server:port. The server value can be a hostname or an IP address. The port portion can optionally be specified in another environment variable, SDPORT. In BBx or ProvideX environments, when using the sdrun.bb/pv or sdofc*.bb/pv programs, you can instead specify a global string “$sdserver”, using the stbl (gbl on ProvideX) function. The port value can optionally be specified in the global string “$sdport”. sdOffice 2.0 18 For the target sdOffice Client, the default on Unix or Linux is to evaluate the “who” command to determine the hostname of the client PC. This value will generally be accurate if the user is logged in over a telnet or ssh connection (typically via a terminal emulator). If this value isn’t valid, then an environment variable SDHOST can be defined. On Windows, there is no default value, so the target must be explicitly provided or the SDHOST environment variable must be defined. Note that in BBx or ProvideX, the stbl or gbl value “$sdhost” can be used in lieu of setting the SDHOST environment variable. The target can be specified in several ways: an IP address, a computer name (as the Windows PC identifies itself) in the format @name, or a user name (as the Windows user logged in) in the format ~name. sdOffice 2.0 19 Command Files - sdRun Interfaces sdOffice comes with a series of programs designed to process command files, simplifying the communication with sdOffice by allowing a developer to create a text file containing commands and then process the commands automatically. While there are no programming type features like looping constructs, variables, or conditionals, in many cases these interfaces will satisfy the needs of a project and will save the programmer the time of developing the communication layer. And for Perl or Business Basic programmers, the source code can be useful for seeing how to manage the communications. The programs are: sdrun.pl sdrun.exe sdrun.bb sdrun.pv Perl script program Windows 32-bit executable PRO/5 CALLable program ProvideX CALLable program Examples of command files can be found in the sdOffice directory, names s_*.txt. A command file always starts with an application name, such as "word", "excel", or "mail". Following this line are any number of commands and associated parameters. Comments can be interspersed as lines starting with #. To execute the Perl program: perl sdrun.pl CommandFile {Target {ServerPort {ServerIP}}} {>ResponseFile} {2>ErrorFile} CommandFile, the first argument, is required, and is the path to the command file. Target is an optional argument that specifies the sdOffice Client target for the job. If not specified, the environment variable SDHOST is used, or the who command is used to attempt to identify the target PC. Note that the who command technique will not work if sdrun.pl is run in background. ServerIP and ServerPort are optional arguments to specify the server IP address or hostname, and listening port. If they are not supplied, then defaults are used from the environment variable SDSERVER (or localhost) and the environment variable SDPORT (or port 6114). If any get-type commands are issued, the responses are sent to STDOUT. You can redirect the responses to a file rather than the terminal using ">" redirection. If there are multiple get-type commands, a line "<< multiple response break >>" will appear between each result set. If any errors are encountered, the error message is sent to STDERR and the job exits immediately. You can redirect this output with "2>". Normally, STDERR is routed to the terminal. sdOffice 2.0 20 To execute sdRun.exe: \path\to\sdrun.exe CommandFile {Target {ServerPort {ServerIP {ResponseFile {ErrorFile }}}}} CommandFile, the first argument, is required, and is the path to the command file. Target is an optional argument that specifies the sdOffice Client target for the job. If not specified, the environment variable SDHOST is used. ServerIP and ServerPort are optional arguments to specify the server IP address or hostname, and listening port. If they are not supplied, then the defaults are localhost and 6114, respectively. If any get-type commands are issued, the responses are normally displayed in a message box. You can direct the responses to a file using the ResponseFile argument as a file path. If there are multiple get-type commands, a line "<< multiple response break >>" will appear between each result set. If any errors are encountered, normally an error message window is displayed. You can direct this output to a file with the ErrorFile argument as a file path. In either case, the job exits immediately Note that the arguments are positional. To name a ResponseFile, for example, you must also name the ServerIP and ServerPort. To execute the PRO/5 or Providex programs: call "sdrun.bb|pv", CommandFile$, Target$, Server$, Response$, Errmsg$ CommandFile$ is the command file path name to process. Target$ identifies the target sdOffice Client, by IP address, Computer Name (syntax “@name”), or User Name (syntax “~username”). If this value is null, then the default rules for determining the client are used. These rules are defined in the Application Interfaces chapter. Server$ identifies the server IP or hostname and optionally the port (format server or server:port) of the sdOffice Network Server. If this value is null, the default rules for determining the server are used. These rules are defined in the Application Interfaces chapter. Response$ will contain all the reponses returned by Get style commands in the command file. Multiple responses will be delimited with ASCII 0 characters. Errmsg$ will return any error message encountered. If a command encounters an error, the remainder of the command file isn't processed, and the error message is returned immediately. sdOffice 2.0 21 Standard I/O - sdpipe.pl Interface The sdpipe.pl interface is a simple Perl script that communicates standard input and output over a socket, enabling application programs without TCP/IP socket support to open a connection to the sdOffice Network Server and execute jobs through it. The syntax of sdpipe.pl is: perl /path/sdpipe.pl { server { port }} The optional arguments are server and port, which default to ‘localhost’ and ‘6114’, or the values in environment variables SDHOST and SDPORT, if supplied. Once a pipe is opened to this command line, writes to the pipe are sent to the server, and reads from the pipe return server responses. Any program that uses sdpipe.pl must adhere to the direct interface guidelines, including terminating all commands with a CR-LF sequence (chr(13) + chr(10)), and reading “get” responses until a terminating line with a single period (“.”+chr(13)+chr(10)). sdOffice 2.0 22 BBx and ProvideX Interfaces sdOffice includes several BBx and ProvideX programs that can simplify the management of a sdOffice session. These programs are CALLed modules that initiate and manage the communication with sdOffice automatically. Target machines can be automatically determined by sdofc.bb/pv in a Unix environment where users connect via telnet or ssh, based on the ‘who –m’ or ‘who –mx’ command. However, if you are running outside of this environment, or you want to target an Office Client on a different system than the one running the terminal emulator, you need to specify the target using the string table global “$sdhost”. For example: x$=stbl("$sdhost","192.168.1.20") x$=stbl("$sdhost", "@mycomputer") x$=stbl("$sdhost","~JohnSmith") Under ProvideX, use gbl() rather than stbl(). Under BBx, you can also define values with “set” commands in the config.bbx file: set $sdhost=192.168.1.20 Also note that if the sdOffice server is on a different machine than the BBx or ProvideX application, you need to define stbl/gbl “$sdserver” to specify the server machine and port: x$=stbl("$sdserver","192.168.1.99:6114") Generic Interface Program – sdofc.bb or sdofc.pv There is program sdofc.bb (and sdofc.pv for ProvideX) that manages the socket communication with the sdOffice server. The CALL arguments for sdofc.bb/pv are object$, cmd$, response$, errmsg$. This program can be used to manage a session with any sdOffice object, simply by passing the object in the first argument. For example: obj$=”excel” call “sdofc.bb”,obj$,”newbook”,response$,errmsg$ call “sdofc.bb”,obj$,”writecell col=1,row=1,value=123.45”,response$,errmsg$ call “sdofc.bb”,obj$,”leaveopen”,””,”” call “sdofc.bb”,obj$,”close”,””,”” Object-Specific Interface Programs For most objects, there is also a specific program that can be called that matches the object. For example, the program sdofc_e.bb is the BBx version of the Excel program. These objectspecific programs are provided for compatibility with sdOffice 1. Each of these object-specific programs simply calls “sdofc.bb” or “sdofc.pv” with a static first argument. sdOffice 2.0 23 These object-specific sdOffice program uses a simple, three-value argument list, call "sdofc_e.bb", cmd$, response$, errmsg$ for example. In each case, cmd$ is a command value and optional parameters, response$ returns any results from "get" style commands, and errmsg$ returns a null or an error message, if an error is encountered. Unlike direct socket interfaces, there is no need to initially specify which application to automate (Word, Outlook, Excel, etc.), as the program CALLed selects and initializes the correct application automatically. In many cases, the parameter portion can contain a number of name=value pairs. Each pair is delimited with a comma, and each value may be quoted if it contains commas. For example, to set a cell font in Excel, you would use a command like this: call "sdofc_e.bb","format col=1,row=1,font=Arial,size=14.5,bold",response$,errmsg$ The first CALL to one of the sdOffice programs will open a channel to the sdOffice server and issue the correct initialization command (word, excel, mapi, etc.). A connection with the sdOffice Network Server is established via a socket or a pipe to sdpipe.pl, depending on the socket capabilities of the language. Revisions of PRO/5 or Visual PRO/5 after 2.2 support sockets with the addition of ‘alias N0 tcp’ to the config.bbx file. ProvideX also supports sockets. Older versions of PRO/5 on Unix will use the sdpipe.pl interface, but for Visual PRO/5 on Windows, there is no support for the sdofc*.bb programs and you must use the sdrun.exe program to submit jobs as command files. In either language, if stbl("$sdserver") or gbl("$sdserver") or the environment variable SDSERVER is defined, then a socket channel is opened to the specified Network Server. The format of the stbl/gbl or environment variable is: server or server:port. If the port can alternately be specified in the stbl/gbl “$sdport” or the environment variable SDPORT. The Network Server and port values default to ‘localhost’ and ‘6114’, respectively. sdOffice will attempt to connect the job to a workstation running the Office Client. This client is the target, and it can be specified as an IP address, a Windows computer name in the format @name, or a Windows user login in the format ~login. This value can be specified in the stbl/gbl “$sdhost” or environment variable SDHOST. If it isn’t specified, on Unix sdOffice will use the ‘who’ command to attempt to determine the hostname of the system from which a user is logged into Unix. In the case of a ProvideX user running WindX, the default value will be set to the WindX terminal’s address rather than using a ‘who’ command. The channel must remain open, or the session terminates, along with the ActiveX Automation session. When you are ready for the session to end, you can call the program with cmd$="close", and the session will terminate. As an alternative, a Business Basic BEGIN or END will also close channels and terminate the session. The sdofc.bb/pv programs use timeout error handling when communicating with the server, both under socket and DDE modes. The default timeout value for any operation is 30 seconds. You can adjust this value by setting the STBL (GBL under pvx) value for $sdtim to the number of sdOffice 2.0 24 seconds desired. For example, trash$=stbl("$sdtim","60") would establish 60 seconds as the timeout value before an error is returned. Here is a summary of each of the programs: call "sdofc.bb|pv",object$,cmd$,response$,errmsg$ This program automates any valid sdOffice object name, as specified in the object$ argument. This argument must be maintained in all subsequent CALL’s for the same job, as the socket channel is tracked in part by its value. call "sdofc_d.bb|pv",cmd$,response$,errmsg$ This program automates ADO (database) tasks through SQL commands. With this object, you can read and write data in external databases. call "sdofc_e.bb|pv",cmd$,response$,errmsg$ This program automates Excel, providing read, write, and formatting capabilities. You can open existing workbooks, create new workbooks, add embedded charts, manage worksheets and their contents, and print or save the results. call "sdofc_m.bb|pv",cmd$,response$,errmsg$ This program automates MAPI (email messaging) tasks. You can send email to any number of recipients. The mail can include attachments. call "sdofc_o.bb|pv",cmd$,response$,errmsg$ This program automates Outlook, managing appointments, contacts, email, and tasks. Dateoriented information can be used to automate appointment and task records. Master file data can be synchronized with Outlook contacts, and email can be sent using the Outlook address book. Note that email can also be sent using MAPI automation. call "sdofc_w.bb|pv",cmd$,response$,errmsg$ This program automates Word, providing read, write, and formatting capabilities. Use it to open or create Word documents, such as writing letters or performing mail merge functions from within your application. sdOffice 2.0 25 sdOffice 2.0 26 Print Preview – sdpreview.sh This Unix shell script is designed to simplify the creation of simple text report “print previews”, where the text report will appear on the user’s Windows desktop in a scaled, zoom-able window. The script converts standard input to a preview job on the specified Office Client. The syntax of the command is: /path/sdpreview.sh { target { server { port }}} Once running, all standard input to the script is routed to a work file, along with the proper commands required to implement a print preview object on the Office Client. Once the printing is complete, the job is submitted to the sdOffice Network Server using the sdrun.pl Perl script. If the values for target, server, and port are not supplied, then the defaults as described in the sdrun.pl section will be used. However, since sdpreview.sh is typically run within a pipe, the attempt to automatically determine the client via the ‘who’ command will not work. Therefore, it is often important to establish the SDHOST environment variable as the user logs in to the Unix system. sdOffice 2.0 27 Direct Interface Guidelines The basics of this connection lifecycle can be demonstrated with this simple telnet-based example, with application commands indicated with >, and responses with <, for clarity: > < > < > < > < > < > < > < > < > telnet localhost 6114 sdOffice (app connection) 2.0.nn excel;192.168.1.10 ok newbook ok setdelim | ok writerow Column 1|Column 2 ok writerow John|Sally ok show ok leaveopen ok quit In the above example, the application connects to port 6114 on the localhost machine. The sdOffice Network Server is listening for application connections on this machine and port. This is confirmed by the response “sdoffice (app connection) 2.0.nn” (nn is the revision number). The first thing that the application needs to do is request an application object on a particular computer running the Office client. The request consists of a line of object;target. The object is one of the internal objects supported by sdOffice, such as Excel, Word, Outlook, or others, and the target is the Office client to which the job should be sent. The target value can take several forms. First, it can be an IP address. Second, it can be a Window Computer Name prefixed with “@”, such as @sales or @billsdell610. Third, it can be a Windows user name prefixed with “~”, such as ~BillMiller or ~Sally Smith. When clients connect to the server, they identify themselves with their computer name (as defined under Control Panel, System, Computer Name), and the user logged in when the client connects. Note that if the client is installed to run as a service, it will by default login under the user name of “SYSTEM”. In the above example, the initial line is “excel;192.168.1.10”, so it is asking for an Excel object on the client PC whose IP address is 192.168.1.10. When the application sends this initial request line, the server compares connected clients with the request and matches up the application connection with a client connection that can support the object requested and matches the target name. If a client can be assigned to the application, the server sends an “ok” response. If not, the application would get an error message and be disconnected. All error messages start with the prefix “Error: “. sdOffice 2.0 28 For example, if no client could be found, the following response would have been seen: Error: No available clients support excel on 192.168.1.10 Once a connection is established, a job of the requested object is started on the client and is ready to start accepting commands from the application. All commands, except those that begin with the letters “get”, are responded to with either an “ok” or an “Error: message” line. Any command that starts with “get” receives a stream response or an “Error: message” response. All commands must end with a LF or CR+LF ( chr(10) or chr(13) + chr(10) ), and all responses will end with a CR+LF sequence. A stream response is simply a series of lines terminated by a line containing a single period (plus the CR+LF). The terminating line is not to be considered part of the response, but rather just an indicator that the response is complete. Any lines within the data stream that begin with a period are converted to begin with two periods before they are returned to the application, so any application should watch for such lines and treat them as single-period lines. sdOffice 2.0 29 OBJECT REFERENCE The Office client supports a number of objects, most of which are related to Microsoft Office applications, though some simply provide some additional useful functionality. Each object supports a defined set of commands and options, and each object can support additional commands via an extension script, written in VBScript, that can be custom written and distributed to the Office client workstations. Some commands are implemented universally. Once any object is initialized, these universal commands may be sent to the client and the client will act upon them regardless of which object is active. This allows some commands to be executed even if Microsoft Office is not present on the Office Client, by using the always available System object. The standard objects provided by sdOffice are: Microsoft Excel Microsoft Word Microsoft Outlook MAPI (electronic mail via Microsoft MAPI) ADO (database access via ADODB/ODBC) Email (email send/receive via SMTP and POP) System (access to system folders and the Windows shell for launching tasks) Popup (pop up messages) Preview (text report print preview) sdOffice 2.0 30 Job Management Each connection established by an application names an object, such as “excel” or “word”, to work with. In addition, a connection can establish other objects if desired, and switch the current object to any that have been started. Commands that are sent always apply the current job. The job commands are as follows: Command Usage and Parameters JobCloseAll v2.0 jobcloseall Closes all open jobs. JobEnd v2.0 jobend jobname Closes the job specified by jobname. JobGet v2.0 jobget Returns the active job name. JobList v2.0 joblist Returns a list of all open job names. JobLogOff v2.0 joblogoff Ends logging of the job, formerly started with the JobLogOn command. JobLogOn v2.0 joblogon logname sdOffice 2.0 31 Begins logging job commands and time information to the file lognameYYYYMMDD_HHMMSS.sdoj, stored in the JobLogs folder on the Office Client. Stored logs can be run from the Application Connection option in the Office Client, or with an sdRun interface. The JobLogOn and JobLogOff commands should bracket an entire job stream to be effective. JobNew v2.0 jobnew jobname,applicationobject Creates a new job, naming it jobname, and starting the application object object. For example, ‘jobnew job 1,excel’. JobSet v2.0 jobset jobname Sets the active job to jobname. A default job name is created when an application connection is established, based on the initial object requested. The name is “objectjobn”, such as “exceljob1” or “wordjob1”. Universal Commands The following commands are implemented at the connection level and therefore operate no matter what object is active. Command Usage and Parameters GetPath v2.0 getpath foldername Returns the client-side physical path of the named folder. All paths are returned with a terminating backslash. (i.e. c:\program files\) Windows specific folder names Folder Name/Parameter appdata commondesktop commonprograms commonstartmenu sdOffice 2.0 Windows Path user application data folder all users desktop folder all users programs folder all users start menu folder 32 commonstartup cookies desktop favorites history internet mydocuments or personal programs recent sendto startmenu startup templates temp sdOffice specific folder names sdoffice samples joblogs plugins sdOffice 2.0 all users startup folder user cookies folder user desktop folder user favorites folder user history folder user temporary internet folder user my documents folder user program files folder user recent files folder user send to folder user start menu folder user startup folder user templates folder user temporary files folder sdOffice client install path sdOffice samples folder sdOffice joblogs folder sdOffice plugins folder 33 GetFile v2.0 getfile parameters Used to return the contents of a text file on the client workstation. GetFile options The options can include: file=local full path-filename This option uses a full path and filename for the desired file. If you are using the folder option below, only enter the filename (with extension) and not the path. file option only example: getfile file=c:\program files\sample.txt Results = c:\program files\sample.txt file option with folder option example: getfile file=sample.txt,folder=programs Results = C:\Program Files\sample.txt file option with full path-filename and folder option example: Invalid command syntax getfile file=c:\program files\sample.txt,folder=programs Results = C:\Program Files\C:\Program Files\sample.txt folder=foldername Read the file from a local folder. Valid folder names are documented in the GetPath command. The folder option will concatenate the folder value returned with the file option value. So if you give a full path-filename for the file option and use the folder option, the resulting file name will cause an ‘Invalid filename’ error. Popup v2.0 popup parameters The popup displays a popup message on the Office Client desktop, similar to the message popups in instant messaging applications or Microsoft Office 2003. The object accepts a number of parameters to indicate text, links, buttons, and colors. sdOffice 2.0 34 The popup object provides two text regions, a standard text region, normally in the center of the popup, and a link text region, normally the top of the object. The link text can hyperlink to a file or URL, so if the user clicks it, the file is opened or the URL is opened in the browser. Popup options The options can include: File=filename or url This is a file or URL to open when the link text is clicked by the user. If the style is “office”, then it is opened when the user clicks anywhere in the popup. Text=display text LinkText=link text The link text associated with the File value Style = messenger | office This setting controls the style of the popup window. The default style is “messenger”. DisplayStyle = fade | scroll This setting controls how the popup closes, either by fading to clear or scrolling to nothing. TextAlign=alignment bc|bottomcenter bl|bottomleft br|bottomright mc|middlecenter ml|middleleft mr|middleright tc|topcenter tl|topleft tr|topright t|title LinkTextAlign=alignment bc|bottomcenter bl|bottomleft br|bottomright mc|middlecenter ml|middleleft mr|middleright tc|topcenter sdOffice 2.0 35 tl|topleft tr|topright t|title ShowLink = true|false The default value is true, but if set to false, then hyperlinks are not displayed as underlined links. ShowClose = true|false Forces the display of a close box on the popup. The default is off if the style is “messenger”, and true if the style is “office”. Timeout = milliseconds After milliseconds (1000=1 second), close the popup. Set milliseconds to 0 to force the popup to stay open until the user closes it. The default value is 0. BackColor|bc = colorname Sets the background color of the popup to the specified colorname. Valid colors include: black, blue, red, green, cyan, magenta, yellow, white darkblue, darkred, darkyellow, turquoise, teal, pink violet, brightgreen, gray25, gray50 ForeColor|tc = colorname Sets the color for text on the popup. Valid color names are the same as indicated in the BackColor option. BackgroundColorGradient|bcg = colorname Sets the gradient color, used along with the standard background color to generate a color gradient. Valid color names are the same as indicated in the BackColor option. BackgroundStyle|bgs = style Sets the background color gradient style. Can be one of: Angled, Horizontal, Solid, Vertical Preview_On, Preview_Off v2.0 preview_on preview_off These commands turn on and off preview mode, respectively. When preview mode is on, all lines sent to the Office Client are captured in a buffer, and when preview mode is turned off, a print preview window is presented on the workstation. The contents of the print preview are sdOffice 2.0 36 scaled based on the columns and rows received, with form feed characters (chr(12)) delimiting pages. In addition, the user can zoom, scroll, and scale the preview. PreviewLoad v2.0 previewload fullpath-filename The PreviewLoad command loads a text file from a given path and displays its contents in the print preview window. Preview v2.0 preview stringdata The preview command can be used to initiate a report preview window with a single string. This differs from the preview_on and preview_off commands, which capture data sent to the client and then initiate a preview window with the captured data. GetSvrFile v2.0 getsvrfile parameters GetSvrFile is used to transfer a file from the server to the client. GetSvrFile options The options can include: serverfile|sfile=server file All server files are stored in the “files” subdirectory under the sdOffice server install path. There is no need to include path information, as just the base file name is used. clientfile|cfile=client file (full path-filename) This is the file name the server file is copied to. It can be a full path, or you can supply a base name and a folder name. The client file can contain references to special folders in brackets, such as “[mydocuments]specials.doc”. See GetPath for a list of special folder names. folder=foldername Save the client file to a folder. Valid folder names are documented in the GetPath command. sdOffice 2.0 37 SendEmail v2.0 sendemail parameters Sends an email using SMTP. This command accepts many options. Sendemail options to|rec|recipient|sendto=email [,email ,...] Any “to” addresses, separated by commas or entered as multiple to= options. from|sendfrom|sender=email “From” email address. cc= email [,email ,...] Any “cc” addresses, separated by commas or entered as multiple cc= options. bcc= email [,email ,...] Any “bcc” addresses, separated by commas or entered as multiple bcc= options. subject|sub=subject text body|text|bodytext=message body text bodyhtml=HTML message body attach=file [,file ,…] Any file to attach to the email. Files must reside on the client workstation, not the sdOffice server. To attach multiple files, separate them with commas, or use multiple attach options. SetFile v2.0 setfile parameters Used to write a string to a text file on the client workstation. SetFile options Valid options include: text | data=string sdOffice 2.0 38 The text to be written to the file. Note this overwrites the current contents. file | filename | path=file name (full path-filename) The full path and file name of the client-side file to write. SetSvrFile v2.0 setsvrfile parameters SetSvrFile is used to transfer a file from the client to the server. All files sent to the server are written to the “files” subdirectory under the sdOffice server install path. SetSvrFile options The options can include: Clientfile|cfile=client file (fill path-filename) The client-side file name, which can be a full path or a base name located in the folder specified by the folder= option. Serverfile|sfile=server file The server-side file name. Paths are ignored, and the base name is used as a file written to the servers’s “files” directory. Folder=foldername Read the client file from a folder. Valid folder names are documented in the GetPath command. sdOffice 2.0 39 Excel Object Overview Excel uses a two-level document hierarchy. The first level is a workbook (or book), which is equivalent to a .xls file. An Excel session can have any number of workbooks open at one time (OpenBook). When you create a new workbook (NewBook), Excel names it Bookn. You can then perform a SaveAs to give it a file name. Within each workbook are worksheets (or sheets). The worksheets contain the rows and columns of data. Worksheets are named, like workbooks, but the names are not related to the file name of the .xls file. When you create a new sheet (NewSheet), you may provide a name at that time as a parameter. sdOffice works with an active worksheet. When you open or create a workbook, the first worksheet in that workbook is automatically activated. When you create a new sheet in the workbook, it is automatically activated. You can also manually activate a workbook (ActivateBook), and a sheet within the workbook (ActivateSheet), using their names. Sheets can also be cleared of their contents, or deleted entirely (ClearSheet, DelSheet). The name of the current workbook or sheet can also be obtained using GetBook or GetSheet. You can retrieve the data from a worksheet with GetData. You can write data to the sheet with WriteCell or WriteRow. WriteCell provides full control over which cell gets updated, while WriteRow is an efficient way of writing any amount of data. WriteRow always writes from column 1, at a current row pointer. You can set the row pointer with SetRow. You can format cells, columns, or rows with the Format command, and merge cells with the MergeCells command. Formatting includes options to lock cells or hide cell formulas when used in conjunction with workbook or worksheet protect commands. You can delete and insert columns and rows, using DelCol, DelRow, InsertCol, and InsertRow. You could use this capability to add a title row after sorting and subtotaling a list. Print or manage the printer with Print, Printer, and PrintPreview. To change the page format, use PageSetup. Once a sheet has been populated with data, you can sort the data on up to three columns. If you also have column headings in the first row, you can generate subtotals and grand totals based on breaks in a column. Note that boolean parameters are true if present, false if not, in any command. New commands for Excel in Version 2 include: footer, getfooter, getheader, header, and sendto. sdOffice 2.0 40 Command Usage and Parameters Activate v1.0 activate workbook activatebook workbook Activates an open workbook named as the parameter. The name is case-insensitive. ActivateSheet v1.0 activatesheet worksheet Activates the sheet named as the parameter. The name is case-insensitive. AddChart v1.0 addchart parameters Adds a new chart to the current worksheet. The new chart becomes the current chart. Use the setchart command to change the current chart. See the editchart command for a parameter description. Borders v2.0 borders parameters Adds borders to the cell range specified, or the last cell range specified in a writecell command. col=columns, identifies a column (or in combination with row, a cell) to apply borders to. grid (boolean) – applies a grid layout to the cell range, so that there is an outer border and internal grid lines, using the attributes specified (linestyle, weight, and color) or Excel defaults. left, right, top, bottom (booleans) - select one border side and applies the attributes specified (linestyle, weight, and color) to it, or uses Excel defaults. linestyle=style, which can be one of: continuous, dash, dashdot, dashdotdot, dot, double, slantdashdot, or none range=range, identifies a cell range, such as A2:D16, to apply borders to. row=rows, identifies a row (or in combination with col, a cell) to apply borders to. sdOffice 2.0 41 weight=thickness, which can be one of: hairline, thin, medium, thick color=colorname, which can be one of: black, blue, red, green, cyan, magenta, yellow, white, darkblue, darkred, darkyellow, turquoise, teal, pink, violet, brightgreen, gray25, gray50 colorindex=automatic or none ClearSheet v1.0 clearsheet Removes data and formatting from the current sheet. CloseBook v1.0 closebook Closes the active workbook without saving (use Save or SaveAs to save workbooks). After the command, you must use OpenBook, Newbook, or Activate to make a new workbook active. DelCol v1.0 delcol columnnumber Deletes the column number in specified as the parameter. DeleteDoc v2.0 deletedoc filename Deletes a file from the workstation’s file system. The file must have a .xls extension. DelRow v1.0 delrow rownumber Deletes the row number specified in the parameter, and sets the current row to this value. DelSheet v1.0 delsheet sdOffice 2.0 42 Deletes the active sheet from the active workbook. If the workbook has other sheets, the first sheet is activated. EditChart v1.0 editchart parameters Edits the current chart (see addchart or setchart) based on the parameter values specified. Unspecified parameters remain unchanged in the chart. x=measure y=measure w=measure h=measure Range=cell range Type=chart type Title=chart title CategoryTitle=category axis title ValueTitle=value axis title ExtraTitle=extra title ByColumn (boolean) ByRow (boolean) CatLabels=cols or rows SeriesLabels=cols or rows Legend=yes|true|no|false ApplyLabels=none|value|label|percent|labelpercent Measures are used to define the size and location of the chart when displayed in the worksheet. The default location is 0,0 (upper left of worksheet), and the default width and height are 4 inches and 3 inches, respectively. Measures default to inches, but the units can be changed with the units command. Cellranges are used to supply the data to chart. Charts use data in the worksheet on which they are added. The default range is the contigous data area starting with cell A1. To specify a different range, use an absolute range, such as "$B$1:$D$10", or a relative range from the current row. Excel will attempt to determine the descriptions and values from the range. This interpretation can be controlled by the CatLabels and SeriesLabels parameters, and the ByRow and ByColumn parameters. The chart type can be one of the following names: area bar stackedbar 100bar column sdOffice 2.0 43 line stackedline pie radar xyscatter 3darea 3dbar 3dstackedbar 3d100bar 3dcolumn 3dline 3dpie 3dsurface doughnut The various titles apply to the chart or axes. The extra title is used for some chart types. Byrow and Bycolumn determine how Excel inteprets the worksheet range for data. Byrow is the default, where each row represents a new data series. Bycolumn interprets columns for the data series. When determining the series and category titles, Excel will analyze the worksheet range. You can specify the number of columns or rows to interpret using Catlabels and Serieslabels parameters. ApplyLabels controls the use of labels on series data. Footer v2.0 footer parameters Sets the print footer based on the following parameters: lh | leftfooter=left footer text ch | centerfooter=center footer text rh | rightfooter=right footer text Format v1.0 format parameters Use this command to format a cell, a column, a row, or the whole sheet. Formatting can include font information, alignment, width, height, and masking. The following fields can be set with any number of name=value pairs in the parameter. autofit (boolean, no value needed) backcolor=colorname center (boolean) sdOffice 2.0 44 col=column color=colorname font=name fontbold or bold (boolean) fontitalic or italic (boolean) fontsize or size=size height=measure hide (boolean) left (boolean) lock (boolean) mergecells (boolean) numberformat=format range=range right (boolean) row=row width=measure wraptext (boolean) If col and row are specified, then just the intersecting cell is affected. If col or row is specified, then the specified column or row is affected. If range is specified (such as A1:F1), then all cells in the specified range are affected. If neither column nor row nor range is specified, then all cells are affected. Measure values are given in inches by default, but the the unit if measure can be changed to points, millimeters, or centimeters with the Units command. NumberFormat matches the number format values available in the Excel Format Cells dialog. To force text, use "@". This is useful for fields that appear numeric, such as zip codes or numeric ID codes, but which should be left justified. Date formats are also specified this way, though Excel recognizes most human-readable dates, such as "12/31/01", correctly. See Excel help for complete formatting instructions. Some example values: #,##0.00 (2 decimals with commas) m/d (short month/year) @ (text) 0.000 (3 decimals) General (general format) 00000 (zip code) mm/dd/yy (date) (* #,##0.00_);_(* (#,##0.00);_(* ""- ""??_);_(@_) (custom format) Usage notes: Autofit should be performed after the data has been added to the cells. If text fields contain numeric data with leading 0s, like zip codes or ID codes, format the column as text ([email protected]
sdOffice ® Version 2.0 Copyright ©2007 by Synergetic Data Systems Inc. All rights reserved. sdOffice is a registered trademark of Synergetic Data Systems Inc. Other product names used in this document may be trademarks or registered trademarks of their respective owners. sdOffice 2.0 1 TABLE OF CONTENTS TABLE OF CONTENTS................................................................................................................ 2 INTRODUCTION .......................................................................................................................... 4 ARCHITECTURE .......................................................................................................................... 5 NETWORK SERVER INSTALLATION ...................................................................................... 6 Unix/Linux Server From Download ........................................................................................... 6 Unix/Linux Server from CD ....................................................................................................... 6 Windows Server.......................................................................................................................... 8 OFFICE CLIENT INSTALLATION ............................................................................................. 9 CONFIGURATION...................................................................................................................... 10 Unix Configuration ................................................................................................................... 10 Windows Configuration............................................................................................................ 12 LICENSING ................................................................................................................................. 13 Unix Licensing.......................................................................................................................... 14 Windows Licensing .................................................................................................................. 15 Activation Errors....................................................................................................................... 16 WINDOWS OFFICE CLIENT OVERVIEW .............................................................................. 17 Overview................................................................................................................................... 17 APPLICATION CLIENT INTERFACES.................................................................................... 18 Pre-defined Interfaces ............................................................................................................... 18 Default Rules for Client and Server Addresses ........................................................................ 18 Command Files - sdRun Interfaces........................................................................................... 20 Standard I/O - sdpipe.pl Interface............................................................................................. 22 BBx and ProvideX Interfaces ................................................................................................... 23 Print Preview – sdpreview.sh.................................................................................................... 27 Direct Interface Guidelines ....................................................................................................... 28 OBJECT REFERENCE ................................................................................................................ 30 Job Management ....................................................................................................................... 31 Command Usage and Parameters ......................................................................................... 31 Universal Commands................................................................................................................ 32 Command Usage and Parameters ......................................................................................... 32 Excel Object.............................................................................................................................. 40 Overview............................................................................................................................... 40 Command Usage and Parameters ......................................................................................... 41 Word Object.............................................................................................................................. 57 Overview............................................................................................................................... 57 Command Usage and Parameters ......................................................................................... 58 Outlook Object.......................................................................................................................... 69 Overview............................................................................................................................... 69 Command Usage and Parameters ......................................................................................... 69 MAPI Object............................................................................................................................. 77 sdOffice 2.0 2 Overview............................................................................................................................... 77 Commands and parameters ................................................................................................... 78 ADO Object .............................................................................................................................. 80 Overview............................................................................................................................... 80 Command Usage and Parameters ......................................................................................... 81 System Object ........................................................................................................................... 90 Mail Object ............................................................................................................................... 91 Overview............................................................................................................................... 91 Command Usage and Parameters ......................................................................................... 91 SAMPLES..................................................................................................................................... 95 Sample: ADO Database Manipulation...................................................................................... 96 Sample: Excel Calculation Engine............................................................................................ 97 Sample: Excel Formatting......................................................................................................... 98 Sample: Excel Report ............................................................................................................... 99 Sample: Excel Charting .......................................................................................................... 101 Sample: MAPI email submission............................................................................................ 102 Sample: Outlook Add Appointment ....................................................................................... 103 Sample: Outlook Add Contact ................................................................................................ 104 Sample: Outlook Email........................................................................................................... 105 Sample: Outlook Read Appointments .................................................................................... 106 Sample: Outlook Read Contacts ............................................................................................. 107 Sample: Word Document Formatting..................................................................................... 108 Sample: Word Mail Merge ..................................................................................................... 110 ADMIN CONNECTIONS.......................................................................................................... 112 OBJECT EXTENSIONS WITH VBSCRIPT............................................................................. 113 AUTOMATED FILE DISTRIBUTION..................................................................................... 116 APPENDIX................................................................................................................................. 118 Colors in Word and Excel....................................................................................................... 118 Paper Bins ............................................................................................................................... 119 Paper Sizes .............................................................................................................................. 120 sdOffice 2.0 3 INTRODUCTION sdOffice is a unique software tool that enables access to Microsoft Office® and other Windowsbased technologies from non-Windows systems and applications. Any application or computer that can interact with a TCP/IP socket or Unix/Linux pipe can now work with Microsoft Office and other products, using sdOffice as the bridge to the Component Object Model (COM) interfaces found in many Windows applications. COM is a method used in the Windows application world to treat programs, such as Microsoft Excel® and Microsoft Word®, as programmable objects from within other programs. This powerful facility is an important part of the Microsoft Windows® platform, but many legacy programming environments are not able to take advantage of it. In addition, many applications today run in Unix and Linux environments and have no direct way to access COM objects on Windows systems. sdOffice is the bridge that allows applications of any sort to work with the COM object model for Microsoft Office. sdOffice accepts commands from an application and translates them to the appropriate COM methods, allowing applications written in virtually any programming language, and running on virtually any operating system, to control programs like Excel and Word in real time with a comprehensive, extensible set of commands. As an example of the sort of capability that sdOffice provides, imagine the example of a traditional export to Excel procedure used by many legacy software users. In the original effort, the user runs a report that creates a tab-delimited or comma-separated-value text file. The user then copies the file to their PC, opens Excel, and imports the file. The columns in that file show up in the cells in Excel, and then the work begins. The user begins formatting the columns to match the data types and formats, adds column headings, inserts a formula column, adds column totals or maybe some grouped subtotals. After all this work, the Excel worksheet finally looks like a finished document. With sdOffice, that same report that started the whole process can export directly to Excel and perform every one of those formatting, formula, and totaling steps without any user intervention. With that sort of automated functionality, the application, rather than the user, performs all the work to produce the finished document, saving a tremendous amount of time. sdOffice is composed of several elements, which are described in the next chapter. sdOffice 2.0 4 ARCHITECTURE sdOffice is composed of three elements: An sdOffice Network Server Windows-based Office clients Application clients The heart of sdOffice is the Network Server. This software runs full time in background, optionally as a service under Windows, and as a daemon on Unix or Linux. The Network Server is the interface point for both Office clients and Application clients. The Office clients connect to the network server when they start up, and maintain a persistent connection while waiting for application clients to connect and initiate jobs. The Office client is the piece that translates commands into COM object methods. The Office client is similar to, but more powerful than, the old sdOffice 1.0 Windows client. The Application clients connect to the network server whenever a job needs to be executed on an Office client. The Application connects to the Network Server, specifies which client and which job object, and then begins sending commands. The Network Server routes the commands to the appropriate client, and returns responses back. Application clients include: The application software itself, if it can work with a TCP/IP socket A Perl-based pipe for applications that can use bi-directional pipes but not sockets sdRun executables (Perl-based on Unix/Linux, native on Windows) which process the commands from a text file BBx and ProvideX wrappers around the above features, providing a familiar CALL interface to programmers in those languages It is also possible to emulate an Application Client using Telnet, or by using the Application Connection window in the Office Client’s visual interface. sdOffice 2.0 5 NETWORK SERVER INSTALLATION Unix/Linux Server From Download 1. Login as root. 2. Create a directory to hold the sdOffice Server files, and change to that directory. Example: 3. umask 0 mkdir /usr/sdofc20 cd /usr/sdofc20 Uncompress and extract sdOffice from the download file. uncompress sdo20_xxx_tar.Z tar xvf sdo20_xxx_tar 4. Execute the set up script. ./sdsetup.sh The sdsetup.sh script will create a launch script called /usr/bin/sdo20d, used to start and stop the sdOffice Network Server. 5. Activate demo mode, or activate permanently, using ./license.sh. 6. Start the server: sdo20d start 7. Check the log file to verify operation: more sdo20d.log or tail sdo20d.log. See the Licensing section for activation information. Note that you will probably want to place the sdo20d start command in your system boot scripts, often found in the /etc/init.d directory or a similar location, depending on your version of UNIX. Unix/Linux Server from CD 1. Login as root. sdOffice 2.0 6 2. Mount the CD as a file system that supports lowercase file names. If you are unsure how to do this, check your man pages: man mount. The following table illustrates sample mount commands for various operating systems, assuming standard CD device names and that the mount directory /mnt is available. You may need to adjust these commands according to your configuration. SCO UNIX OS5 SCO UNIX Unixware AIX Sun Solaris HP/UX mount –o lower /dev/cd0 /mnt mount –r –f HS,lower /dev/cd0 /mnt mount –F cdfs –r /dev/cdrom/cdrom1 /mnt mount –vcdrfs –r /dev/cd0 /mnt mount –rt hsfs /dev/sr0 /mnt mount –r –F cdfs –o cdcase /dev/dsk/c1d0s2 /mnt 3. Change to the sdOffice 2.0 UNIX directory in the mount directory: cd /mnt/sdo20/unix 4. Run the install script: ./install.sh, or if you do not have execute permission to the file, sh install.sh. You must agree to the license agreement, then you will be presented a list of operating system versions. Choose the correct version for your system. 5. The sdOffice server will then be installed to the selected directory, and the set up script ./sdsetup.sh will be automatically executed in that directory. The sdsetup.sh script will create a launch script called /usr/bin/sdo20d, used to start and stop the sdOffice Network Server. 6. Activate demo mode, or activate permanently, using ./license.sh. 7. Start the server: sdo20d start 8. Check the log file to verify operation: more sdo20d.log or tail sdo20d.log. See the Licensing section for additional activation information. Note that you will probably want to place the sdo20d start command in your system boot scripts, often found in the /etc/init.d directory or a similar location, depending on your version of UNIX. sdOffice 2.0 7 Windows Server 1. From the CD, use Explorer to locate the D:\sdo20\win directory, and double-click the setup.exe program (use Control Panel Add/Remove Programs if the system supports Terminal Services). If you downloaded sdOffice from the Internet, simply execute the downloaded executable (use Control Panel Add/Remove programs if the system supports Terminal Services). Follow the on-screen prompts from the installer to install sdOffice to your system. This will install the sdo20d.exe server program, along with supporting files and the run-time engine, and create Start menu options under the title “sdOffice 2.0 Server”. 2. Click the Server Configuration option from the Start menu. This will conditionally rename certain files and prompt for several configuration values. The values entered are stored in the sdo20d.ini file. You can also use the Configure button from within the sdOffice Server Manager. 3. Click the Server Manager option from the Windows Start, Programs, sdOffice 2.0 Server menu. 4. Activate the demo mode, then if desired, activate permanently, by pressing the Licensing button and using the form that displays. On line help is available if needed. 5. Click the Start button from the Server Manager to start the server manually. 6. Check the log in the Server Manager to monitor operation. 7. If desired, and you are running the server on Windows NT, 2000, XP or any of the Windows variants that support NT Services, you can install the server as a service by running the Install as a Service option. When the sdOffice Server is run as a service, it is automatically started when Windows boots up. You must start and stop the service using the Windows Services applet, found in the Control Panel Administrative Tools option. The Server Manager options for starting and stopping the server are disabled. See the Licensing section for activation information. sdOffice 2.0 8 OFFICE CLIENT INSTALLATION The office client is a separate installation from the server. This Windows program should be installed on any workstation that will perform sdOffice jobs. Simply run the sdOffice2_setup.exe program. If you install it on a Windows system that supports Terminal Services, such as Windows 2003 Server, it must be installed using Control Panel, Add/Remove Programs while logged in as an administrator. This technique can be used in lieu of directly running the setup program on any system, but it is required in a server environment. Once installed and started, choose the Options tab to configure the Office Client. See the Office Client Overview chapter for more details. Automatic Configuration At the end of the setup execution, the setup program will look for the file “sdOffice2.ini” in the same path as sdOffice2_setup.exe. If found, that file will be used as the default configuration file. This procedure allows an administrator to configure one Office client installation normally, then copy the sdOffice2.ini file from his/her Office Client install path to the location where the sdOffice2_setup.exe program is normally installed from (or distribute the file with the setup.exe). Users will then get a default configuration, including server and port settings, automatically. sdOffice 2.0 9 CONFIGURATION Unix Configuration The network server is configured by editing the sdo20d.ini file. Here is an example file: [defaults] logfile=sdo20d.log logdetail=1 # client security is controlled as follows: # secure=0 unauthenticated, open (suggested for LAN only) # secure=1 authenticated connections but data sent in clear (VPN # or low-value data traffic) # secure=2 authenticated, SSL encrypted secure=0 refresh_manifiest=0 [clients] port=6115 allow=192.*.*.*;99.99.99.99 [apps] port=6114 allow=192.168.1.10;192.168.1.11 [admin] #uses apps port allow=127.0.0.1 The options for this file are defined below. logfile logdetail secure [defaults] section Connections, and optionally detail transaction data, are logged to this file. If set to 0, only connections are logged. If set to 1, transaction details are logged. If turned on, be sure to watch the size of the log file, and restart the Network Server periodically to reset the log. This value sets the security level for client connections, which often can come from remote systems across the Internet. There are three levels: 0 - Neither encryption nor authentication is performed on the socket. Note that all connection types are filtered by IP address to ensure only specific addresses can connect to the server. This option is sdOffice 2.0 10 typically all that is required on a local network, as long as the data that will be sent to clients is not highly sensitive. 1-Authentication only. No encryption is performed, but clients must authenticate themselves as valid sdOffice Office clients. 2-Authentication and encryption. Office Clients must authenticate themselves, plus all client traffic is encrypted using SSL. If the host system does not support SSL (i.e. the openssl libraries are not available), then this option will produce a startup error and the sdOffice Network Server will not start. jobhist This value controls the creation and purging of job history files. Job history files are placed in the jobhist directory under the server install directory. Each job’s commands are stored in a job history file, allowing for easy retrieval of jobs for analysis or debugging. Error messages returned by the client are entered into the job history file as a comment. The value is the number of days that job history files are retained. Anywhere from 0, meaning no job history files are created, to a fraction of a day or any number of days. refresh_manifest port allow port allow sdOffice 2.0 Jobhist=1 would keep job history files for 24 hours. Jobhost=.04167 would keep them for 1 hour. The job history files are named Sets the number of minutes between client re-processing of the manifest.txt file in the server “files” directory. Set to 0 to not refresh (the file will only be read as clients start up and connect to the server). This value should be an integer, and fractional minutes are rounded to the nearest integer. See the Automated File Distribution chapter for details. [clients] section The port on which the Network Server listens for Office client connections. This defaults to port 6115. If changed, Office clients must be configured to use the new port. A semi-colon delimited list of valid IP addresses or address wildcards for Office clients. Clients whose IP address is not in this list are denied access. Common address wildcards for local networks include 192.*.*.* and 10.*.*.*. [apps] section The port on which the Network Server listens for Application client connections. This defaults to port 6114. If changed, Application clients must use the new port. A semi-colon delimited list of valid IP addresses or address 11 wildcards for Application clients. Clients whose IP address is not in this list are denied access. allow Common address wildcards for local networks include 192.*.*.* and 10.*.*.*. [admin] section A semi-colon delimited list of valid IP addresses or address wildcards for admin connections. Connections from IP addresses not in this list are denied access. This is often set to the localhost address, 127.0.0.1, allowing admin access only from the network server host machine. Admin connections are initiated via the Application client port, typically via telnet, and the first command line sent is always “admin”. Admin connections provide several commands to manage the Network server. Windows Configuration On Windows, you can edit the sd20d.ini file just as on Unix, or you can use the sdOffice Server Manager and select the Configure button. The Configuration screen provides editing capabilities to many of sdo20d.ini settings. See the previous section for details about setting the various fields on this form, or view the online help. sdOffice 2.0 12 LICENSING Licensing for sdOffice is based upon the number of concurrent Application clients that will connect to the sdOffice Network Server. Application clients typically connect only long enough to run a job, from a few seconds to a few minutes, so the number of connection licenses required typically will be less than the number of active users on a network. The connection counts available are 1, 3, 5, 10, 15, 20, 25, 30, 40, 50, 75, 100, and unlimited. Each sdOffice Network Server is issued a unique serial number and two activation keys. One key enables the server itself, and is tied to the server’s system ID and machine class, both generated at the time of install. The other key enables the licensed number of Application connections. Licensing is controlled entirely by the sdOffice Network Server process, sdo20d. You can install the Application interfaces and Office clients freely anywhere on your network. Each sdOffice Network Server installation has a serial number. There is one special serial number, SD0099999, reserved for demo mode use on any machine. All permanent licenses are assigned a unique serial number and must be licensed to a single machine installation. Serial numbers and their associated PIN codes are assigned by SDSI when sdOffice is purchased. In order to obtain permanent or emergency temporary activation keys, the serial number and PIN code are required. There are two activation keys that must be entered for full operation of sdOffice: a system key and a connections key. The system key enables the sdOffice Network Server to operate on a specific computer. The connections key determines the number of concurrent Application connections that may run. For demo mode operation, just a temporary system key is required; demo mode operation automatically enables 3 Application connections. There are three types of system activation keys: 30-Day Demo This license has a fixed serial number (SD0099999) and can run on any machine for 30 days. While running under this serial number, sdOffice will print “*Demo*” phrases randomly in data sent to sdOffice clients. This is the first mode activated after an installation, as it enables the retrieval of a System ID and Machine Class needed for permanent licensing later, as well as allowing sdOffice to operate in demo mode. Permanent This license has an assigned serial number, and requires a System ID and Machine Class to activate. A permanent license does not expire, enabling the sdOffice Network Server to run perpetually on the machine where installed and licensed. The System ID is derived from a given installation machine and attributes of a file in the sdOffice rt\lib\keys directory (Windows) or the rt\lib directory (UNIX), so it will change if the installation is moved to a new machine, or even to a new location on the same machine. Once the System ID changes, the permanent activation key sdOffice 2.0 13 will no longer work, and sdOffice must be re-activated. If the original permanent installation of sdOffice is no longer used, then you can request a reset of the permanent license to enable a new System ID and Machine Class to be associated with the permanent activation key. Contact [email protected] to request resets. Emergency Temporary This license is assigned a serial number, like a permanent license, but it does not require a System ID or Machine Class to activate. This allows you to re-install the sdOffice Network Server on a different machine than originally licensed, and operate it for 30 days. Once a temporary license has been issued for a given serial number, another temporary license cannot be issued for 45 days. Unix Licensing To activate the sdOffice Network Server on UNIX, perform the following steps: Login as root. cd to the sdOffice directory (i.e. cd /usr/lib/sdsi/sdofc20). Execute ./license.sh. The license.sh script prompts for the following options: SDOFFICE LICENSING OPTIONS Use the following options if this machine is connected to the Internet: ----------------------------------------------------------------------1 - Permanent Activation (requires serial number and PIN code) 2 - Emergency Temporary Activation (also requires SN and PIN) 3 - 30-Day Demo Mode Activation Use the following options for manual activation. Activation keys can be obtained from http://synergetic-data.com/sd2lic.cgi. ----------------------------------------------------------------4 - Display System ID and machine class (needed for option 5) 5 - Enter Permanent Activation 6 - Enter Emergency Temporary Activation 7 - Enter 30-Day Demo Mode Activation q - quit Enter selection: To obtain either a permanent or emergency temporary activation, you will need to know your serial number and PIN code previously assigned by SDSI. These values are not necessary to obtain a 30-day demo mode activation. If your machine has Internet access, you can perform activation easily by choosing options 1 through 3. Options 1 and 2 will prompt you for your serial number and PIN. Each of the three options will use the Internet to retrieve the desired activation key. sdOffice 2.0 14 If the Internet is not available from the install machine, then you can perform activation manually by using another machine to visit http://synergetic-data.com/sd2lic.cgi. Use option 4 to display the System ID and Machine Class, which will be required to obtain a permanent activation key from this web site. Options 5 and 6 will prompt for a serial number, system key, and connections key, in sequence. Option 7 will only prompt for a system key. Windows Licensing The first step after an installation is to activate demo mode. This initializes the system ID file, enabling a permanent license to be obtained. If you get an error message after pressing the Show System ID button, then this installation has never been initialized, and you must activate demo mode first. To activate demo mode: If you are connected to the Internet, press the Automatic Demo Activation button. This will obtain a current demo mode activation key from SDSI's website and activate the run-time engine. If you are not connected to the Internet, go to a computer that is, and go to http://synergeticdata.com/sd2lic.cgi, then click the link to get a 30-day trial. Note the activation key returned, and enter it exactly the same way in the Demo Activation Key field, then click the Manual Demo Activation button. To verify the activation, click the Show System ID button. If the System ID and Class fields get filled in, then it worked. sdOffice 2.0 15 To activate permanent mode: To activate automatically over the Internet, you need to click the Show System ID button to get the System ID and Machine Class fields. Then fill in your serial number and PIN code, and click the Automatic Activation button. This will use your information to obtain a permanent activation key for the system, as well as your job and designer activation keys, and activate everything. To activate sdOffice manually, note your System ID and Machine Class, then go to http://synergetic-data.com/sd2lic.cgi. Enter your serial number and PIN code, then click the button to get a permanent license. When prompted, enter the System ID and Machine Class exactly as noted on this screen. Note the two activation keys returned, and enter them exactly as provided in the two entry fields, then click the Manual Activation button. To activate in emergency temporary mode: To obtain a temporary activation over the Internet or manually, follow the steps for a permanent license, but check the Emergency Temp Activation option. The System ID and Machine Class are not used for temporary activations. Activation Errors Permanent activation keys are dependent on the system ID and machine class information generated by an installation. Therefore, a permanent activation key will only work on the original installation for which it was generated. If the sdOffice Network Server needs to be moved or re-installed, a new permanent activation key must be generated. This is only possible if SDSI resets the permanent key for your serial number, so you must contact SDSI, certify that the original installation is no longer in use, and request a reset. In the meantime, you can obtain an emergency temporary activation to allow your serial number to be used on a new installation for 30 days. If you attempt to get a new permanent activation key and are notified that one has already been assigned, then contact SDSI to request a reset. If this cannot be done in a timely fashion, get an emergency temporary key instead, and then contact SDSI at a later time. Note that temporary keys are issued at most once every 45 days. If you get an error message indicating the temporary key availability has not expired, then you must contact SDSI to get a reset. sdOffice 2.0 16 WINDOWS OFFICE CLIENT OVERVIEW Overview The Office Client runs on Windows-based computers and executes the jobs routed to it from the sdOffice Network Server. This program provides the interface to Microsoft Office and other objects, by translating job command streams into COM object methods and properties. This program provides a user interface to view and edit job activity and configuration parameters. There is also a simple interface to test jobs on the client, without connecting to a Network Server and consuming application connection licenses. For details about this interface, consult the Help menu in the Office Client. sdOffice 2.0 17 APPLICATION CLIENT INTERFACES The basic principle behind any application client is to connect to the sdOffice Network Server, send an initialization command, and then begin sending commands for the job. The server parses the initialization command and attempts to link the Application client with an appropriate Office client. Pre-defined Interfaces Applications which use the pre-defined interfaces do not need to worry about the internal send and response formats used by the server. The pre-defined interfaces are: sdRun interfaces (sdrun.exe on Windows and sdrun.pl (Perl-based) on Unix/Linux). These interfaces submit a job command file, which is simply a text file containing the object and the commands to send to that object. sdpipe.pl, a Perl-based script designed to provide a standard I/O method of interfacing with the server, for application environments that can’t communicate directly with sockets. sdofc*.bb/sdofc*.pv, BBx and ProvideX callable programs designed for operation in those programming environments. sdpreview.sh, a Unix/Linux shell script designed to display a report print-preview on a user’s PC workstation, simply by printing to it. The script uses the sdrun.pl Perl script, so Perl is a prerequisite. In addition to these interfaces, any application that can communicate with the server via a TCP/IP socket (or the sdpipe.pl script) can connect and execute jobs by following the guidelines for connecting to the server and submitting jobs. These guidelines are described in the section titled Direct Interface Guidelines. Default Rules for Client and Server Addresses When an application wishes to start a job, it must connect to an sdOffice Network Server, and tell it what target sdOffice Client to send the job to. The application interfaces can be told explicitly what these values are, but there are other ways to specify the information. For the Network Server, the default address is ‘localhost’, and the default port is 6114. In order to specify a different default, you can establish an environment variable SDSERVER with the format server or server:port. The server value can be a hostname or an IP address. The port portion can optionally be specified in another environment variable, SDPORT. In BBx or ProvideX environments, when using the sdrun.bb/pv or sdofc*.bb/pv programs, you can instead specify a global string “$sdserver”, using the stbl (gbl on ProvideX) function. The port value can optionally be specified in the global string “$sdport”. sdOffice 2.0 18 For the target sdOffice Client, the default on Unix or Linux is to evaluate the “who” command to determine the hostname of the client PC. This value will generally be accurate if the user is logged in over a telnet or ssh connection (typically via a terminal emulator). If this value isn’t valid, then an environment variable SDHOST can be defined. On Windows, there is no default value, so the target must be explicitly provided or the SDHOST environment variable must be defined. Note that in BBx or ProvideX, the stbl or gbl value “$sdhost” can be used in lieu of setting the SDHOST environment variable. The target can be specified in several ways: an IP address, a computer name (as the Windows PC identifies itself) in the format @name, or a user name (as the Windows user logged in) in the format ~name. sdOffice 2.0 19 Command Files - sdRun Interfaces sdOffice comes with a series of programs designed to process command files, simplifying the communication with sdOffice by allowing a developer to create a text file containing commands and then process the commands automatically. While there are no programming type features like looping constructs, variables, or conditionals, in many cases these interfaces will satisfy the needs of a project and will save the programmer the time of developing the communication layer. And for Perl or Business Basic programmers, the source code can be useful for seeing how to manage the communications. The programs are: sdrun.pl sdrun.exe sdrun.bb sdrun.pv Perl script program Windows 32-bit executable PRO/5 CALLable program ProvideX CALLable program Examples of command files can be found in the sdOffice directory, names s_*.txt. A command file always starts with an application name, such as "word", "excel", or "mail". Following this line are any number of commands and associated parameters. Comments can be interspersed as lines starting with #. To execute the Perl program: perl sdrun.pl CommandFile {Target {ServerPort {ServerIP}}} {>ResponseFile} {2>ErrorFile} CommandFile, the first argument, is required, and is the path to the command file. Target is an optional argument that specifies the sdOffice Client target for the job. If not specified, the environment variable SDHOST is used, or the who command is used to attempt to identify the target PC. Note that the who command technique will not work if sdrun.pl is run in background. ServerIP and ServerPort are optional arguments to specify the server IP address or hostname, and listening port. If they are not supplied, then defaults are used from the environment variable SDSERVER (or localhost) and the environment variable SDPORT (or port 6114). If any get-type commands are issued, the responses are sent to STDOUT. You can redirect the responses to a file rather than the terminal using ">" redirection. If there are multiple get-type commands, a line "<< multiple response break >>" will appear between each result set. If any errors are encountered, the error message is sent to STDERR and the job exits immediately. You can redirect this output with "2>". Normally, STDERR is routed to the terminal. sdOffice 2.0 20 To execute sdRun.exe: \path\to\sdrun.exe CommandFile {Target {ServerPort {ServerIP {ResponseFile {ErrorFile }}}}} CommandFile, the first argument, is required, and is the path to the command file. Target is an optional argument that specifies the sdOffice Client target for the job. If not specified, the environment variable SDHOST is used. ServerIP and ServerPort are optional arguments to specify the server IP address or hostname, and listening port. If they are not supplied, then the defaults are localhost and 6114, respectively. If any get-type commands are issued, the responses are normally displayed in a message box. You can direct the responses to a file using the ResponseFile argument as a file path. If there are multiple get-type commands, a line "<< multiple response break >>" will appear between each result set. If any errors are encountered, normally an error message window is displayed. You can direct this output to a file with the ErrorFile argument as a file path. In either case, the job exits immediately Note that the arguments are positional. To name a ResponseFile, for example, you must also name the ServerIP and ServerPort. To execute the PRO/5 or Providex programs: call "sdrun.bb|pv", CommandFile$, Target$, Server$, Response$, Errmsg$ CommandFile$ is the command file path name to process. Target$ identifies the target sdOffice Client, by IP address, Computer Name (syntax “@name”), or User Name (syntax “~username”). If this value is null, then the default rules for determining the client are used. These rules are defined in the Application Interfaces chapter. Server$ identifies the server IP or hostname and optionally the port (format server or server:port) of the sdOffice Network Server. If this value is null, the default rules for determining the server are used. These rules are defined in the Application Interfaces chapter. Response$ will contain all the reponses returned by Get style commands in the command file. Multiple responses will be delimited with ASCII 0 characters. Errmsg$ will return any error message encountered. If a command encounters an error, the remainder of the command file isn't processed, and the error message is returned immediately. sdOffice 2.0 21 Standard I/O - sdpipe.pl Interface The sdpipe.pl interface is a simple Perl script that communicates standard input and output over a socket, enabling application programs without TCP/IP socket support to open a connection to the sdOffice Network Server and execute jobs through it. The syntax of sdpipe.pl is: perl /path/sdpipe.pl { server { port }} The optional arguments are server and port, which default to ‘localhost’ and ‘6114’, or the values in environment variables SDHOST and SDPORT, if supplied. Once a pipe is opened to this command line, writes to the pipe are sent to the server, and reads from the pipe return server responses. Any program that uses sdpipe.pl must adhere to the direct interface guidelines, including terminating all commands with a CR-LF sequence (chr(13) + chr(10)), and reading “get” responses until a terminating line with a single period (“.”+chr(13)+chr(10)). sdOffice 2.0 22 BBx and ProvideX Interfaces sdOffice includes several BBx and ProvideX programs that can simplify the management of a sdOffice session. These programs are CALLed modules that initiate and manage the communication with sdOffice automatically. Target machines can be automatically determined by sdofc.bb/pv in a Unix environment where users connect via telnet or ssh, based on the ‘who –m’ or ‘who –mx’ command. However, if you are running outside of this environment, or you want to target an Office Client on a different system than the one running the terminal emulator, you need to specify the target using the string table global “$sdhost”. For example: x$=stbl("$sdhost","192.168.1.20") x$=stbl("$sdhost", "@mycomputer") x$=stbl("$sdhost","~JohnSmith") Under ProvideX, use gbl() rather than stbl(). Under BBx, you can also define values with “set” commands in the config.bbx file: set $sdhost=192.168.1.20 Also note that if the sdOffice server is on a different machine than the BBx or ProvideX application, you need to define stbl/gbl “$sdserver” to specify the server machine and port: x$=stbl("$sdserver","192.168.1.99:6114") Generic Interface Program – sdofc.bb or sdofc.pv There is program sdofc.bb (and sdofc.pv for ProvideX) that manages the socket communication with the sdOffice server. The CALL arguments for sdofc.bb/pv are object$, cmd$, response$, errmsg$. This program can be used to manage a session with any sdOffice object, simply by passing the object in the first argument. For example: obj$=”excel” call “sdofc.bb”,obj$,”newbook”,response$,errmsg$ call “sdofc.bb”,obj$,”writecell col=1,row=1,value=123.45”,response$,errmsg$ call “sdofc.bb”,obj$,”leaveopen”,””,”” call “sdofc.bb”,obj$,”close”,””,”” Object-Specific Interface Programs For most objects, there is also a specific program that can be called that matches the object. For example, the program sdofc_e.bb is the BBx version of the Excel program. These objectspecific programs are provided for compatibility with sdOffice 1. Each of these object-specific programs simply calls “sdofc.bb” or “sdofc.pv” with a static first argument. sdOffice 2.0 23 These object-specific sdOffice program uses a simple, three-value argument list, call "sdofc_e.bb", cmd$, response$, errmsg$ for example. In each case, cmd$ is a command value and optional parameters, response$ returns any results from "get" style commands, and errmsg$ returns a null or an error message, if an error is encountered. Unlike direct socket interfaces, there is no need to initially specify which application to automate (Word, Outlook, Excel, etc.), as the program CALLed selects and initializes the correct application automatically. In many cases, the parameter portion can contain a number of name=value pairs. Each pair is delimited with a comma, and each value may be quoted if it contains commas. For example, to set a cell font in Excel, you would use a command like this: call "sdofc_e.bb","format col=1,row=1,font=Arial,size=14.5,bold",response$,errmsg$ The first CALL to one of the sdOffice programs will open a channel to the sdOffice server and issue the correct initialization command (word, excel, mapi, etc.). A connection with the sdOffice Network Server is established via a socket or a pipe to sdpipe.pl, depending on the socket capabilities of the language. Revisions of PRO/5 or Visual PRO/5 after 2.2 support sockets with the addition of ‘alias N0 tcp’ to the config.bbx file. ProvideX also supports sockets. Older versions of PRO/5 on Unix will use the sdpipe.pl interface, but for Visual PRO/5 on Windows, there is no support for the sdofc*.bb programs and you must use the sdrun.exe program to submit jobs as command files. In either language, if stbl("$sdserver") or gbl("$sdserver") or the environment variable SDSERVER is defined, then a socket channel is opened to the specified Network Server. The format of the stbl/gbl or environment variable is: server or server:port. If the port can alternately be specified in the stbl/gbl “$sdport” or the environment variable SDPORT. The Network Server and port values default to ‘localhost’ and ‘6114’, respectively. sdOffice will attempt to connect the job to a workstation running the Office Client. This client is the target, and it can be specified as an IP address, a Windows computer name in the format @name, or a Windows user login in the format ~login. This value can be specified in the stbl/gbl “$sdhost” or environment variable SDHOST. If it isn’t specified, on Unix sdOffice will use the ‘who’ command to attempt to determine the hostname of the system from which a user is logged into Unix. In the case of a ProvideX user running WindX, the default value will be set to the WindX terminal’s address rather than using a ‘who’ command. The channel must remain open, or the session terminates, along with the ActiveX Automation session. When you are ready for the session to end, you can call the program with cmd$="close", and the session will terminate. As an alternative, a Business Basic BEGIN or END will also close channels and terminate the session. The sdofc.bb/pv programs use timeout error handling when communicating with the server, both under socket and DDE modes. The default timeout value for any operation is 30 seconds. You can adjust this value by setting the STBL (GBL under pvx) value for $sdtim to the number of sdOffice 2.0 24 seconds desired. For example, trash$=stbl("$sdtim","60") would establish 60 seconds as the timeout value before an error is returned. Here is a summary of each of the programs: call "sdofc.bb|pv",object$,cmd$,response$,errmsg$ This program automates any valid sdOffice object name, as specified in the object$ argument. This argument must be maintained in all subsequent CALL’s for the same job, as the socket channel is tracked in part by its value. call "sdofc_d.bb|pv",cmd$,response$,errmsg$ This program automates ADO (database) tasks through SQL commands. With this object, you can read and write data in external databases. call "sdofc_e.bb|pv",cmd$,response$,errmsg$ This program automates Excel, providing read, write, and formatting capabilities. You can open existing workbooks, create new workbooks, add embedded charts, manage worksheets and their contents, and print or save the results. call "sdofc_m.bb|pv",cmd$,response$,errmsg$ This program automates MAPI (email messaging) tasks. You can send email to any number of recipients. The mail can include attachments. call "sdofc_o.bb|pv",cmd$,response$,errmsg$ This program automates Outlook, managing appointments, contacts, email, and tasks. Dateoriented information can be used to automate appointment and task records. Master file data can be synchronized with Outlook contacts, and email can be sent using the Outlook address book. Note that email can also be sent using MAPI automation. call "sdofc_w.bb|pv",cmd$,response$,errmsg$ This program automates Word, providing read, write, and formatting capabilities. Use it to open or create Word documents, such as writing letters or performing mail merge functions from within your application. sdOffice 2.0 25 sdOffice 2.0 26 Print Preview – sdpreview.sh This Unix shell script is designed to simplify the creation of simple text report “print previews”, where the text report will appear on the user’s Windows desktop in a scaled, zoom-able window. The script converts standard input to a preview job on the specified Office Client. The syntax of the command is: /path/sdpreview.sh { target { server { port }}} Once running, all standard input to the script is routed to a work file, along with the proper commands required to implement a print preview object on the Office Client. Once the printing is complete, the job is submitted to the sdOffice Network Server using the sdrun.pl Perl script. If the values for target, server, and port are not supplied, then the defaults as described in the sdrun.pl section will be used. However, since sdpreview.sh is typically run within a pipe, the attempt to automatically determine the client via the ‘who’ command will not work. Therefore, it is often important to establish the SDHOST environment variable as the user logs in to the Unix system. sdOffice 2.0 27 Direct Interface Guidelines The basics of this connection lifecycle can be demonstrated with this simple telnet-based example, with application commands indicated with >, and responses with <, for clarity: > < > < > < > < > < > < > < > < > telnet localhost 6114 sdOffice (app connection) 2.0.nn excel;192.168.1.10 ok newbook ok setdelim | ok writerow Column 1|Column 2 ok writerow John|Sally ok show ok leaveopen ok quit In the above example, the application connects to port 6114 on the localhost machine. The sdOffice Network Server is listening for application connections on this machine and port. This is confirmed by the response “sdoffice (app connection) 2.0.nn” (nn is the revision number). The first thing that the application needs to do is request an application object on a particular computer running the Office client. The request consists of a line of object;target. The object is one of the internal objects supported by sdOffice, such as Excel, Word, Outlook, or others, and the target is the Office client to which the job should be sent. The target value can take several forms. First, it can be an IP address. Second, it can be a Window Computer Name prefixed with “@”, such as @sales or @billsdell610. Third, it can be a Windows user name prefixed with “~”, such as ~BillMiller or ~Sally Smith. When clients connect to the server, they identify themselves with their computer name (as defined under Control Panel, System, Computer Name), and the user logged in when the client connects. Note that if the client is installed to run as a service, it will by default login under the user name of “SYSTEM”. In the above example, the initial line is “excel;192.168.1.10”, so it is asking for an Excel object on the client PC whose IP address is 192.168.1.10. When the application sends this initial request line, the server compares connected clients with the request and matches up the application connection with a client connection that can support the object requested and matches the target name. If a client can be assigned to the application, the server sends an “ok” response. If not, the application would get an error message and be disconnected. All error messages start with the prefix “Error: “. sdOffice 2.0 28 For example, if no client could be found, the following response would have been seen: Error: No available clients support excel on 192.168.1.10 Once a connection is established, a job of the requested object is started on the client and is ready to start accepting commands from the application. All commands, except those that begin with the letters “get”, are responded to with either an “ok” or an “Error: message” line. Any command that starts with “get” receives a stream response or an “Error: message” response. All commands must end with a LF or CR+LF ( chr(10) or chr(13) + chr(10) ), and all responses will end with a CR+LF sequence. A stream response is simply a series of lines terminated by a line containing a single period (plus the CR+LF). The terminating line is not to be considered part of the response, but rather just an indicator that the response is complete. Any lines within the data stream that begin with a period are converted to begin with two periods before they are returned to the application, so any application should watch for such lines and treat them as single-period lines. sdOffice 2.0 29 OBJECT REFERENCE The Office client supports a number of objects, most of which are related to Microsoft Office applications, though some simply provide some additional useful functionality. Each object supports a defined set of commands and options, and each object can support additional commands via an extension script, written in VBScript, that can be custom written and distributed to the Office client workstations. Some commands are implemented universally. Once any object is initialized, these universal commands may be sent to the client and the client will act upon them regardless of which object is active. This allows some commands to be executed even if Microsoft Office is not present on the Office Client, by using the always available System object. The standard objects provided by sdOffice are: Microsoft Excel Microsoft Word Microsoft Outlook MAPI (electronic mail via Microsoft MAPI) ADO (database access via ADODB/ODBC) Email (email send/receive via SMTP and POP) System (access to system folders and the Windows shell for launching tasks) Popup (pop up messages) Preview (text report print preview) sdOffice 2.0 30 Job Management Each connection established by an application names an object, such as “excel” or “word”, to work with. In addition, a connection can establish other objects if desired, and switch the current object to any that have been started. Commands that are sent always apply the current job. The job commands are as follows: Command Usage and Parameters JobCloseAll v2.0 jobcloseall Closes all open jobs. JobEnd v2.0 jobend jobname Closes the job specified by jobname. JobGet v2.0 jobget Returns the active job name. JobList v2.0 joblist Returns a list of all open job names. JobLogOff v2.0 joblogoff Ends logging of the job, formerly started with the JobLogOn command. JobLogOn v2.0 joblogon logname sdOffice 2.0 31 Begins logging job commands and time information to the file lognameYYYYMMDD_HHMMSS.sdoj, stored in the JobLogs folder on the Office Client. Stored logs can be run from the Application Connection option in the Office Client, or with an sdRun interface. The JobLogOn and JobLogOff commands should bracket an entire job stream to be effective. JobNew v2.0 jobnew jobname,applicationobject Creates a new job, naming it jobname, and starting the application object object. For example, ‘jobnew job 1,excel’. JobSet v2.0 jobset jobname Sets the active job to jobname. A default job name is created when an application connection is established, based on the initial object requested. The name is “objectjobn”, such as “exceljob1” or “wordjob1”. Universal Commands The following commands are implemented at the connection level and therefore operate no matter what object is active. Command Usage and Parameters GetPath v2.0 getpath foldername Returns the client-side physical path of the named folder. All paths are returned with a terminating backslash. (i.e. c:\program files\) Windows specific folder names Folder Name/Parameter appdata commondesktop commonprograms commonstartmenu sdOffice 2.0 Windows Path user application data folder all users desktop folder all users programs folder all users start menu folder 32 commonstartup cookies desktop favorites history internet mydocuments or personal programs recent sendto startmenu startup templates temp sdOffice specific folder names sdoffice samples joblogs plugins sdOffice 2.0 all users startup folder user cookies folder user desktop folder user favorites folder user history folder user temporary internet folder user my documents folder user program files folder user recent files folder user send to folder user start menu folder user startup folder user templates folder user temporary files folder sdOffice client install path sdOffice samples folder sdOffice joblogs folder sdOffice plugins folder 33 GetFile v2.0 getfile parameters Used to return the contents of a text file on the client workstation. GetFile options The options can include: file=local full path-filename This option uses a full path and filename for the desired file. If you are using the folder option below, only enter the filename (with extension) and not the path. file option only example: getfile file=c:\program files\sample.txt Results = c:\program files\sample.txt file option with folder option example: getfile file=sample.txt,folder=programs Results = C:\Program Files\sample.txt file option with full path-filename and folder option example: Invalid command syntax getfile file=c:\program files\sample.txt,folder=programs Results = C:\Program Files\C:\Program Files\sample.txt folder=foldername Read the file from a local folder. Valid folder names are documented in the GetPath command. The folder option will concatenate the folder value returned with the file option value. So if you give a full path-filename for the file option and use the folder option, the resulting file name will cause an ‘Invalid filename’ error. Popup v2.0 popup parameters The popup displays a popup message on the Office Client desktop, similar to the message popups in instant messaging applications or Microsoft Office 2003. The object accepts a number of parameters to indicate text, links, buttons, and colors. sdOffice 2.0 34 The popup object provides two text regions, a standard text region, normally in the center of the popup, and a link text region, normally the top of the object. The link text can hyperlink to a file or URL, so if the user clicks it, the file is opened or the URL is opened in the browser. Popup options The options can include: File=filename or url This is a file or URL to open when the link text is clicked by the user. If the style is “office”, then it is opened when the user clicks anywhere in the popup. Text=display text LinkText=link text The link text associated with the File value Style = messenger | office This setting controls the style of the popup window. The default style is “messenger”. DisplayStyle = fade | scroll This setting controls how the popup closes, either by fading to clear or scrolling to nothing. TextAlign=alignment bc|bottomcenter bl|bottomleft br|bottomright mc|middlecenter ml|middleleft mr|middleright tc|topcenter tl|topleft tr|topright t|title LinkTextAlign=alignment bc|bottomcenter bl|bottomleft br|bottomright mc|middlecenter ml|middleleft mr|middleright tc|topcenter sdOffice 2.0 35 tl|topleft tr|topright t|title ShowLink = true|false The default value is true, but if set to false, then hyperlinks are not displayed as underlined links. ShowClose = true|false Forces the display of a close box on the popup. The default is off if the style is “messenger”, and true if the style is “office”. Timeout = milliseconds After milliseconds (1000=1 second), close the popup. Set milliseconds to 0 to force the popup to stay open until the user closes it. The default value is 0. BackColor|bc = colorname Sets the background color of the popup to the specified colorname. Valid colors include: black, blue, red, green, cyan, magenta, yellow, white darkblue, darkred, darkyellow, turquoise, teal, pink violet, brightgreen, gray25, gray50 ForeColor|tc = colorname Sets the color for text on the popup. Valid color names are the same as indicated in the BackColor option. BackgroundColorGradient|bcg = colorname Sets the gradient color, used along with the standard background color to generate a color gradient. Valid color names are the same as indicated in the BackColor option. BackgroundStyle|bgs = style Sets the background color gradient style. Can be one of: Angled, Horizontal, Solid, Vertical Preview_On, Preview_Off v2.0 preview_on preview_off These commands turn on and off preview mode, respectively. When preview mode is on, all lines sent to the Office Client are captured in a buffer, and when preview mode is turned off, a print preview window is presented on the workstation. The contents of the print preview are sdOffice 2.0 36 scaled based on the columns and rows received, with form feed characters (chr(12)) delimiting pages. In addition, the user can zoom, scroll, and scale the preview. PreviewLoad v2.0 previewload fullpath-filename The PreviewLoad command loads a text file from a given path and displays its contents in the print preview window. Preview v2.0 preview stringdata The preview command can be used to initiate a report preview window with a single string. This differs from the preview_on and preview_off commands, which capture data sent to the client and then initiate a preview window with the captured data. GetSvrFile v2.0 getsvrfile parameters GetSvrFile is used to transfer a file from the server to the client. GetSvrFile options The options can include: serverfile|sfile=server file All server files are stored in the “files” subdirectory under the sdOffice server install path. There is no need to include path information, as just the base file name is used. clientfile|cfile=client file (full path-filename) This is the file name the server file is copied to. It can be a full path, or you can supply a base name and a folder name. The client file can contain references to special folders in brackets, such as “[mydocuments]specials.doc”. See GetPath for a list of special folder names. folder=foldername Save the client file to a folder. Valid folder names are documented in the GetPath command. sdOffice 2.0 37 SendEmail v2.0 sendemail parameters Sends an email using SMTP. This command accepts many options. Sendemail options to|rec|recipient|sendto=email [,email ,...] Any “to” addresses, separated by commas or entered as multiple to= options. from|sendfrom|sender=email “From” email address. cc= email [,email ,...] Any “cc” addresses, separated by commas or entered as multiple cc= options. bcc= email [,email ,...] Any “bcc” addresses, separated by commas or entered as multiple bcc= options. subject|sub=subject text body|text|bodytext=message body text bodyhtml=HTML message body attach=file [,file ,…] Any file to attach to the email. Files must reside on the client workstation, not the sdOffice server. To attach multiple files, separate them with commas, or use multiple attach options. SetFile v2.0 setfile parameters Used to write a string to a text file on the client workstation. SetFile options Valid options include: text | data=string sdOffice 2.0 38 The text to be written to the file. Note this overwrites the current contents. file | filename | path=file name (full path-filename) The full path and file name of the client-side file to write. SetSvrFile v2.0 setsvrfile parameters SetSvrFile is used to transfer a file from the client to the server. All files sent to the server are written to the “files” subdirectory under the sdOffice server install path. SetSvrFile options The options can include: Clientfile|cfile=client file (fill path-filename) The client-side file name, which can be a full path or a base name located in the folder specified by the folder= option. Serverfile|sfile=server file The server-side file name. Paths are ignored, and the base name is used as a file written to the servers’s “files” directory. Folder=foldername Read the client file from a folder. Valid folder names are documented in the GetPath command. sdOffice 2.0 39 Excel Object Overview Excel uses a two-level document hierarchy. The first level is a workbook (or book), which is equivalent to a .xls file. An Excel session can have any number of workbooks open at one time (OpenBook). When you create a new workbook (NewBook), Excel names it Bookn. You can then perform a SaveAs to give it a file name. Within each workbook are worksheets (or sheets). The worksheets contain the rows and columns of data. Worksheets are named, like workbooks, but the names are not related to the file name of the .xls file. When you create a new sheet (NewSheet), you may provide a name at that time as a parameter. sdOffice works with an active worksheet. When you open or create a workbook, the first worksheet in that workbook is automatically activated. When you create a new sheet in the workbook, it is automatically activated. You can also manually activate a workbook (ActivateBook), and a sheet within the workbook (ActivateSheet), using their names. Sheets can also be cleared of their contents, or deleted entirely (ClearSheet, DelSheet). The name of the current workbook or sheet can also be obtained using GetBook or GetSheet. You can retrieve the data from a worksheet with GetData. You can write data to the sheet with WriteCell or WriteRow. WriteCell provides full control over which cell gets updated, while WriteRow is an efficient way of writing any amount of data. WriteRow always writes from column 1, at a current row pointer. You can set the row pointer with SetRow. You can format cells, columns, or rows with the Format command, and merge cells with the MergeCells command. Formatting includes options to lock cells or hide cell formulas when used in conjunction with workbook or worksheet protect commands. You can delete and insert columns and rows, using DelCol, DelRow, InsertCol, and InsertRow. You could use this capability to add a title row after sorting and subtotaling a list. Print or manage the printer with Print, Printer, and PrintPreview. To change the page format, use PageSetup. Once a sheet has been populated with data, you can sort the data on up to three columns. If you also have column headings in the first row, you can generate subtotals and grand totals based on breaks in a column. Note that boolean parameters are true if present, false if not, in any command. New commands for Excel in Version 2 include: footer, getfooter, getheader, header, and sendto. sdOffice 2.0 40 Command Usage and Parameters Activate v1.0 activate workbook activatebook workbook Activates an open workbook named as the parameter. The name is case-insensitive. ActivateSheet v1.0 activatesheet worksheet Activates the sheet named as the parameter. The name is case-insensitive. AddChart v1.0 addchart parameters Adds a new chart to the current worksheet. The new chart becomes the current chart. Use the setchart command to change the current chart. See the editchart command for a parameter description. Borders v2.0 borders parameters Adds borders to the cell range specified, or the last cell range specified in a writecell command. col=columns, identifies a column (or in combination with row, a cell) to apply borders to. grid (boolean) – applies a grid layout to the cell range, so that there is an outer border and internal grid lines, using the attributes specified (linestyle, weight, and color) or Excel defaults. left, right, top, bottom (booleans) - select one border side and applies the attributes specified (linestyle, weight, and color) to it, or uses Excel defaults. linestyle=style, which can be one of: continuous, dash, dashdot, dashdotdot, dot, double, slantdashdot, or none range=range, identifies a cell range, such as A2:D16, to apply borders to. row=rows, identifies a row (or in combination with col, a cell) to apply borders to. sdOffice 2.0 41 weight=thickness, which can be one of: hairline, thin, medium, thick color=colorname, which can be one of: black, blue, red, green, cyan, magenta, yellow, white, darkblue, darkred, darkyellow, turquoise, teal, pink, violet, brightgreen, gray25, gray50 colorindex=automatic or none ClearSheet v1.0 clearsheet Removes data and formatting from the current sheet. CloseBook v1.0 closebook Closes the active workbook without saving (use Save or SaveAs to save workbooks). After the command, you must use OpenBook, Newbook, or Activate to make a new workbook active. DelCol v1.0 delcol columnnumber Deletes the column number in specified as the parameter. DeleteDoc v2.0 deletedoc filename Deletes a file from the workstation’s file system. The file must have a .xls extension. DelRow v1.0 delrow rownumber Deletes the row number specified in the parameter, and sets the current row to this value. DelSheet v1.0 delsheet sdOffice 2.0 42 Deletes the active sheet from the active workbook. If the workbook has other sheets, the first sheet is activated. EditChart v1.0 editchart parameters Edits the current chart (see addchart or setchart) based on the parameter values specified. Unspecified parameters remain unchanged in the chart. x=measure y=measure w=measure h=measure Range=cell range Type=chart type Title=chart title CategoryTitle=category axis title ValueTitle=value axis title ExtraTitle=extra title ByColumn (boolean) ByRow (boolean) CatLabels=cols or rows SeriesLabels=cols or rows Legend=yes|true|no|false ApplyLabels=none|value|label|percent|labelpercent Measures are used to define the size and location of the chart when displayed in the worksheet. The default location is 0,0 (upper left of worksheet), and the default width and height are 4 inches and 3 inches, respectively. Measures default to inches, but the units can be changed with the units command. Cellranges are used to supply the data to chart. Charts use data in the worksheet on which they are added. The default range is the contigous data area starting with cell A1. To specify a different range, use an absolute range, such as "$B$1:$D$10", or a relative range from the current row. Excel will attempt to determine the descriptions and values from the range. This interpretation can be controlled by the CatLabels and SeriesLabels parameters, and the ByRow and ByColumn parameters. The chart type can be one of the following names: area bar stackedbar 100bar column sdOffice 2.0 43 line stackedline pie radar xyscatter 3darea 3dbar 3dstackedbar 3d100bar 3dcolumn 3dline 3dpie 3dsurface doughnut The various titles apply to the chart or axes. The extra title is used for some chart types. Byrow and Bycolumn determine how Excel inteprets the worksheet range for data. Byrow is the default, where each row represents a new data series. Bycolumn interprets columns for the data series. When determining the series and category titles, Excel will analyze the worksheet range. You can specify the number of columns or rows to interpret using Catlabels and Serieslabels parameters. ApplyLabels controls the use of labels on series data. Footer v2.0 footer parameters Sets the print footer based on the following parameters: lh | leftfooter=left footer text ch | centerfooter=center footer text rh | rightfooter=right footer text Format v1.0 format parameters Use this command to format a cell, a column, a row, or the whole sheet. Formatting can include font information, alignment, width, height, and masking. The following fields can be set with any number of name=value pairs in the parameter. autofit (boolean, no value needed) backcolor=colorname center (boolean) sdOffice 2.0 44 col=column color=colorname font=name fontbold or bold (boolean) fontitalic or italic (boolean) fontsize or size=size height=measure hide (boolean) left (boolean) lock (boolean) mergecells (boolean) numberformat=format range=range right (boolean) row=row width=measure wraptext (boolean) If col and row are specified, then just the intersecting cell is affected. If col or row is specified, then the specified column or row is affected. If range is specified (such as A1:F1), then all cells in the specified range are affected. If neither column nor row nor range is specified, then all cells are affected. Measure values are given in inches by default, but the the unit if measure can be changed to points, millimeters, or centimeters with the Units command. NumberFormat matches the number format values available in the Excel Format Cells dialog. To force text, use "@". This is useful for fields that appear numeric, such as zip codes or numeric ID codes, but which should be left justified. Date formats are also specified this way, though Excel recognizes most human-readable dates, such as "12/31/01", correctly. See Excel help for complete formatting instructions. Some example values: #,##0.00 (2 decimals with commas) m/d (short month/year) @ (text) 0.000 (3 decimals) General (general format) 00000 (zip code) mm/dd/yy (date) (* #,##0.00_);_(* (#,##0.00);_(* ""- ""??_);_(@_) (custom format) Usage notes: Autofit should be performed after the data has been added to the cells. If text fields contain numeric data with leading 0s, like zip codes or ID codes, format the column as text ([email protected]DC02_Fin
Chapter Two
The Internet
and World Wide Web
1439079420_Ch02OP_REV.indd 72 10/27/09 10:32:18 AM
Objectives
After completing this chapter, you will be able to:
1 Discuss the evolution of the Internet
2 Identify and briefly describe various broadband Internet connections and
state differences between broadband Internet Internet connections and dial-up
connections
3 Describe the types of Internet access providers: Internet service providers,
online service providers, wireless Internet service providers
4 Describe the purpose of an IP address and its relationship to a domain
name
5 Explain the purpose of a Web browser and identify the components of a
Web address
6 Describe how to use a search engine to search for information on the Web
and differentiate between a search engine and a subject directory
7 Describe the types of Web sites: portal, news, informational, business/
marketing, blog, wiki, online social network, educational, entertainment,
advocacy, Web application, content aggregator, and personal
8 Explain how Web pages use graphics, animation, audio, video, virtual
reality, and plug-ins
9 Identify and briefly describe the steps required for Web publishing
10 Describe the types of e-commerce: business-to-consumer, consumerto-consumer,
and business-to-business
11 Explain how e-mail, mailing lists, instant messaging, chat rooms, VoIP,
newsgroups and message boards, and FTP work
12 Identify the rules of netiquette
1439079420_Ch02OP_REV.indd 73 10/27/09 10:32:36 AM
74 Chapter 2 The Internet and World Wide Web
The Internet
One of the major reasons business, home, and
other users purchase computers is for Internet
access. The Internet is a widely used research
tool, providing society with access to global
information and instant communications.
Further, access to the Internet can occur anytime
from a computer anywhere: at home, at
work, at school, in a restaurant, on an airplane,
and at a park.
The Internet, also called the Net, is a worldwide
collection of networks that links millions
of businesses, government agencies, educational
institutions, and individuals. Each of the networks
Web — conduct research
Web — share videos
on the Internet provides resources that add to the
abundance of goods, services, and information
accessible via the Internet.
Today, more than one billion home and business
users around the world access a variety of
services on the Internet, some of which are shown
in Figure 2-1. The World Wide Web, or simply
the Web, and e-mail are two of the more widely
used Internet services. Other services include chat
rooms, instant messaging, and VoIP (Voice over
Internet Protocol). To enhance your understanding
of these Internet services, the chapter begins
by discussing the history of the Internet and how
the Internet works and then explains each of
these services.
Web — read blogs
Figure 2-1 People around the world use a variety of Internet services in daily activities. Internet services allow home and business
users to access the Web for activities such as conducting research, reading blogs, or sharing videos; to send e-mail messages; or to
converse with others using chat rooms, instant messaging, or VoIP.
1439079420_Ch02_FINAL.indd 74 11/09/10 6:02:48 PM
Evolution of the Internet
The Internet has its roots in a networking project
started by the Pentagon’s Advanced Research
Projects Agency (ARPA), an agency of the U.S.
Department of Defense. ARPA’s goal was to build a
network that (1) allowed scientists at different physical
locations to share information and work together
on military and scientific projects and (2) could
function even if part of the network were disabled
or destroyed by a disaster such as a nuclear attack.
That network, called ARPANET, became functional
in September 1969, linking scientific and academic
researchers across the United States.
The original ARPANET consisted of four main
computers, one each located at the University
of California at Los Angeles, the University of
California at Santa Barbara, the Stanford Research
Institute, and the University of Utah. Each of these
The Internet and World Wide Web Chapter 2 75
computers served as a host on the network. A host,
more commonly known today as a server, is any
computer that provides services and connections
to other computers on a network. Hosts often use
high-speed communications to transfer data and
messages over a network.
As researchers and others realized the great
benefit of using ARPANET to share data and
information, ARPANET underwent phenomenal
growth. By 1984, ARPANET had more than 1,000
individual computers linked as hosts. Today, more
than 550 million hosts connect to the Internet.
Some organizations connected entire networks
to ARPANET to take advantage of its high-speed
communications. In 1986, the National Science
Foundation (NSF) connected its huge network
of five super computer centers, called NSFnet, to
ARPANET. This configuration of complex networks
and hosts became known as the Internet.
chat room
e-mail
instant messaging
1439079420_Ch02_FINAL.indd 75 11/09/10 6:02:58 PM
VoIP
76 Chapter 2 The Internet and World Wide Web
W3C
For more information,
visit scsite.com/dc2011/
ch2/weblink and then
click W3C.
Until 1995, NSFnet handled the bulk of the
communications activity, or traffic, on the Internet.
In 1995, NSFnet terminated its network on the
Internet and resumed its status as a research network.
Today, the Internet consists of many local,
regional, national, and international networks.
Numerous corporations, commercial firms, and
other companies such as IBM provide networks
to handle Internet traffic. Both public and private
organizations own networks on the Internet. These
networks, along with telephone companies such as
Verizon and AT&T, cable and satellite companies,
and the government, all contribute toward the internal
structure of the Internet.
Each organization on the Internet is responsible
only for maintaining its own network. No single
person, company, institution, or government agency
controls or owns the Internet. The World Wide
Web Consortium (W3C), however, oversees research
and sets standards and guidelines for many areas of
the Internet. The mission of the W3C is to contribute
to the growth of the Web. More than 350 organizations
from around the world are members of the
W3C, advising, defining standards, and addressing
other issues.
Internet2
Internet2 is a not-for-profit research and
development project that connects more than 200
universities and 115 companies via a high-speed private
network. Founded in 1996, the goal of Internet2
is to develop and test advanced network technologies
that will benefit Internet users in the short-term
future. These technologies require an extremely
high-speed network that exceeds the capabilities of
today’s Internet and networks. Examples of previous
Internet2 projects that are now mainstream
include telemedicine, digital libraries (online books,
magazines, music, movies, speeches, etc.), and faster
Internet services. Current Internet2 projects include
interactive high-definition video and enhanced
detection and resolution of network problems.
Connecting to the Internet
Many home and small business users connect
to the Internet via high-speed broadband Internet
service. With broadband Internet service, your computer
or mobile device usually is connected to the
Internet the entire time it is powered on. Examples
of broadband Internet service include cable, DSL,
fiber, radio signals, and satellite.
• Cable Internet service provides high-speed Internet
access through the cable television network via a
cable modem.
• DSL (digital subscriber line) provides high-speed
Internet connections using regular copper
telephone lines.
• Fiber to the Premises (FTTP) uses fiber-optic cable
to provide high-speed Internet access to home
and business users.
• Fixed wireless provides high-speed Internet
connections using a dish-shaped antenna on your
house or business to communicate with a tower
location via radio signals.
• A cellular radio network offers high-speed Internet
connections to devices with built-in compatible
technology or computers with wireless modems.
• A Wi-Fi (wireless fidelity) network uses
radio signals to provide high-speed Internet
connections to compatible or properly equipped
wireless computers and devices.
• Satellite Internet service provides high-speed
Internet connections via satellite to a satellite dish
that communicates with a satellite modem.
Employees and students typically connect their
computers to the Internet through a business or
school network. The business or school network
connects to a high-speed broadband Internet service.
Many home users set up a Wi-Fi network, which
sends signals to a communications device that is connected
to a high-speed Internet service such as cable
or DSL. Instead of using broadband Internet service,
however, some home users connect to the Internet
via dial-up access, which is a slower-speed technology.
Dial-up access takes place when the modem in your
computer connects to the Internet via a standard telephone
line that transmits data and information using
an analog (continuous wave pattern) signal. Users may
opt for dial-up access because of its lower price or
because broadband access is not available in their area.
Mobile users access the Internet using a variety of
Internet services. Most hotels and airports provide
wired or wireless Internet connections as a service to
travelers. Wireless Internet services, such as Wi-Fi
networks, allow mobile users to connect easily to the
Internet with notebook computers, smart phones,
and other mobile devices while away from a telephone,
cable, or other wired connection. Many public
locations, such as airports, hotels, schools, shopping
malls, and coffee shops, are hot spots that provide
Wi-Fi Internet connections to users with mobile
computers or devices. At public locations, you may
be required to agree to terms of service, obtain a
password (for example, from the hotel’s front desk),
or perform some other action in order to connect to
the Internet. Some cities provide free Wi-Fi Internet
connections to all residents.
1439079420_Ch02_FINAL.indd 76 11/09/10 6:03:01 PM
FAQ 2-1
How popular is broadband?
According to a study performed by Pew Internet &
American Life Project, 63 percent of American adults
have broadband Internet connections at home.
Adoption of broadband connections increases during
good economic times, while some may hesitate to
make the switch during an economic downturn. It is
believed that once the price of a broadband connection
decreases, and broadband is available in more
rural areas, its popularity will increase further.
For more information, visit scsite.com/dc2011/
ch2/faq and then click Broadband.
Access Providers
An access provider is a business that provides
individuals and organizations access to the
Internet free or for a fee. For example, some
local call
toll-free call
Regional
ISP
cable Internet service
The Internet and World Wide Web Chapter 2 77
Wi-Fi networks provide free access while others
charge a per use fee. Other access providers often
charge a fixed amount for an Internet connection,
offering faster speeds or more services for higher
rates. Typical monthly rates range from about
$5 to $24 per month for dial-up, $13 to $70 for
DSL, $20 to $75 for cable, $40 to $150 for FTTP,
$30 to $80 for fixed wireless, $60 to $80 for cellular
networks, and $50 to $120 for satellite. Many
Internet access providers offer services such as
news, weather, financial data, games, travel guides,
e-mail, photo communities, and online storage
to hold digital photos and other files. (A file is a
named unit of storage.)
Access providers are categorized as regional
or national ISPs, online service providers, and
wireless Internet service providers (Figure 2-2).
National
ISP
Online Service
(special members-only
content)
Online
Service
Provider
DSL
local call
Screen
T.K.
wireless connection
Wireless
Internet
Service
Provider
Figure 2-2 Common ways to access the Internet are through a regional or national Internet service provider, an online service
provider, or a wireless Internet service provider.
1439079420_Ch02_FINAL.indd 77 11/09/10 6:03:02 PM
78 Chapter 2 The Internet and World Wide Web
Wireless Modems
For more information, visit
scsite.com/dc2011/ch2/
weblink and then click
Wireless Modems.
An ISP (Internet service provider)
is a regional or national access provider.
A regional ISP usually provides Internet
access to a specific geographic area. A
national ISP is a business that provides
Internet access in cities and towns nationwide.
For dial-up access, some national
ISPs provide both local and toll-free telephone
numbers. Due to their larger size,
national ISPs usually offer more services
and have a larger technical support staff
than regional ISPs. Examples of national
ISPs are AT&T and EarthLink.
In addition to providing Internet
access, an online service provider
(OSP) also has many members-only
features such as instant messaging or
their own customized version of a Web
browser. The two more popular OSPs
are AOL (America Online) and MSN
(Microsoft Network). AOL differs from
many OSPs in that it provides gateway
functionality to the Internet, meaning it
regulates the Internet services to which
members have access. AOL also provides
free access to its services to any user with
a broadband Internet connection.
When selecting an ISP or OSP for dial-up
access, ensure it pro vides at least one local
telephone number. Otherwise, long-distance
telephone charges will apply for the time you
connect to the Internet.
A wireless Internet service provider, sometimes
called a wireless data provider, is a company
that provides wireless Internet access to
desktop and notebook computers and mobile
devices, such as smart phones and portable media
players, with built-in wireless capability (such as
Wi-Fi) or to computers using wireless modems
or wireless access devices. Wireless modems,
which usually are in the form of a USB flash
drive or a card that inserts in a slot in a computer
or mobile device, generally dial a telephone number
to establish a connection with the wireless
Internet service provider. An antenna on or built
into the computer or device, wireless modem,
or wireless access device typically sends signals
through the airwaves to communicate with a
wireless Internet service provider. Some examples
of wireless Internet service pro viders include
AT&T, Boingo Wireless, Sprint Broadband
Direct, T-Mobile, and Verizon Wireless.
What types of Web sites do mobile Internet
users visit?
More than 87 million individuals subscribe to a wireless
Internet service provider. Mobile Internet users most
frequently visit weather, entertainment, and e-mail Web
sites. The chart below illustrates various types of Web
sites and their associated increase in traffic resulting
from mobile Internet users.
Percent Increase
FAQ 2-2
25%
20%
15%
10%
5%
0%
Weather
Entertainment
Increase Due to Mobile Internet Users
E-mail
Sports
Business
Social Networking
Web Site Type
Source: ClickZ
Search
Shopping
For more information, visit scsite.com/dc2011/ch2/faq
and then click Mobile Internet.
How Data and Information Travel
the Internet
Computers connected to the Internet work
together to transfer data and information
around the world using servers and clients and
various wired and wireless transmission media.
On the Internet, your computer is a client that
can access data, information, and services on a
variety of servers.
The inner structure of the Internet works
much like a transportation system. Just as
interstate highways connect major cities and
carry the bulk of the automotive traffic across
the country, several main transmission media
carry the heaviest amount of traffic on the
Internet. These major carriers of network
traffic are known collectively as the Internet
backbone.
In the United States, the transmission media
that make up the Internet backbone exchange
data and information at several different major
cities across the country. That is, they transfer
data and information from one network to
another until reaching the final destination
(Figure 2-3).
1439079420_Ch02_FINAL.indd 78 11/09/10 6:03:05 PM
How a Home User’s Data and Information Might Travel the Internet
Using a Cable Modem Connection
Step 1
You initiate an action
to request data or
information from
the Internet. For
example, you
request to display
a Web page on your
computer screen.
Internet Addresses
The Internet relies on an addressing system
much like the postal service to send data and
information to a computer at a specific destination.
An IP address, short for Internet Protocol
address, is a number that uniquely identifies each
computer or device connected to the Internet.
The IP address usually consists of four groups of
numbers, each separated by a period. The number
in each group is between 0 and 255. For example,
the numbers 72.14.207.99 are an IP address. In
general, the first portion of each IP address identifies
the network and the last portion identifies
the specific computer.
These all-numeric IP addresses are difficult to
remember and use. Thus, the Internet supports
The Internet and World Wide Web Chapter 2 79
Step 2
A cable modem
transfers the
computer’s digital
signals to the cable
television line in
your house.
Step 6
The server retrieves the requested
Web page and sends it back through
the Internet backbone to your computer.
Step 5
The ISP routes your request through the
Internet backbone to the destination server
(in this example, the server that contains
the requested Web site).
Step 3
Your request (digital signals) travels
through cable television lines to a
central cable
system, which
is shared by
up to 500
homes in a
neighborhood.
the use of a text name that represents one or more
IP addresses. A domain name is the text version
of an IP address. Figure 2-4 shows an IP address
and its associated domain name. As with an IP
address, the components of a domain name are
separated by periods.
The text in the domain name up to the first period
identifies the type of Internet server. In Figure 2-4,
for example, the www indicates a Web server.
Step 4
The central cable system sends
your request over high-speed
fiber-optic lines to the cable
operator, who often
also is the ISP.
Figure 2-3 This figure shows how a home user’s data and information might travel the Internet using a cable modem connection.
IP address 72.14.207.99
Domain name www.google.com
top-level domain
Figure 2-4 The IP address and domain name for the Google Web site.
1439079420_Ch02_FINAL.indd 79 11/09/10 6:03:07 PM
80 Chapter 2 The Internet and World Wide Web
Every domain name contains a top-level domain
(TLD), which is the last section of the domain
name. A generic TLD (gTLD), such as the com in
Figure 2-4 on the previous page, identifies the type
of organization associated with the domain. The
Internet server and gTLD portions of a domain
name often are not required.
The organization that assigns and controls
top-level domains is the Internet Corporation for
Assigned Names and Numbers (ICANN pronounced
EYE-can). Figure 2-5 lists some gTLDs. For TLDs
such as biz, com, info, name, net, and org, you register
for a domain name from a registrar, which is an
organization that sells and manages domain names.
For international Web sites outside the United
States, the domain name also includes a country
code TLD (ccTLD), which is a two-letter country
code, such as au for Australia. For example,
www.philips.com.au is the domain name for Philips
Australia. Some smaller countries have granted use
of their ccTLDs for commercial purposes, such as tv
(Tuvalu) for the television/entertainment industry.
The domain name system (DNS) is the method that
the Internet uses to store domain names and their
corresponding IP addresses. When you specify a
Examples of Generic Top-Level Domains
Generic TLD Intended Purpose
aero Aviation community members
biz Businesses of all sizes
cat Catalan cultural community
com Commercial organizations, businesses, and companies
coop Business cooperatives such as credit unions and rural electric co-ops
edu Educational institutions
gov Government agencies
info
Business organizations or individuals providing general
information
jobs Employment or human resource businesses
mil Military organizations
mobi Delivery and management of mobile Internet services
museum Accredited museums
name Individuals or families
net Network providers or commercial companies
org Nonprofit organizations
pro Certified professionals such as doctors, lawyers, and accountants
tel Internet communications
travel Travel industry
Figure 2-5 In addition to the generic TLDs listed above, ICANN continually
evaluates proposals for new TLDs.
domain name, a DNS server translates the domain
name to its associated IP address so that data and
information can be routed to the correct computer.
A DNS server is an Internet server that usually is
associated with an Internet access provider. For a
more technical discussion about DNS servers, read
the High-Tech Talk article on page 382.
The growth of the Internet has led to a shortage
of IP addresses. Thus, a new IP addressing scheme,
called IPv6, may increase the number of available
IP addresses. For a more technical discussion about
Internet addresses and IPv6, read the High-Tech
Talk article on page 110.
QUIZ YOURSELF 2-1
Instructions: Find the true statement below.
Then, rewrite the remaining false statements so
that they are true.
1. An access provider is a business that
provides individuals and organizations
access to the Internet free or for a fee.
2. A wireless Internet service provider is a
number that uniquely identifies each computer
or device connected to the Internet.
3. An IP address, such as www.google.com, is
the text version of a domain name.
4. Satellite Internet service provides highspeed
Internet access through the cable
television network via a cable modem.
5. The World Wide Web Consortium (W3C)
oversees research and owns the Internet.
Quiz Yourself Online: To further check your
knowledge of pages 74 through 80, visit
scsite.com/dc2011/ch2/quiz and then click
Objectives 1 – 4.
The World Wide Web
Although many people use the terms World Wide
Web and Internet interchangeably, the World
Wide Web actually is a service of the Internet.
While the Internet was developed in the late 1960s,
the World Wide Web emerged in the early 1990s.
Since then, it has grown phenomenally to become
one of the more widely used Internet services.
The World Wide Web (WWW ), or Web,
consists of a worldwide collection of electronic
documents. Each electronic document on the
Web is called a Web page, which can contain text,
graphics, animation, audio, and video. Additionally,
Web pages usually have built-in connections to
other documents.
1439079420_Ch02_FINAL.indd 80 11/09/10 6:03:09 PM
Some Web pages are static (fixed); others are
dynamic (changing). Visitors to a static Web page
all see the same content. With a dynamic Web
page, by contrast, visitors can customize some or
all of the viewed content such as desired stock
quotes, weather for a region, or ticket availability
for flights.
A Web site is a collection of related Web
pages and associated items, such as documents
and pictures, stored on a Web server. A Web
server is a computer that delivers requested
Web pages to your computer. The same Web
server can store multiple Web sites. Some
industry experts use the term Web 2.0 to refer
to Web sites that provide a means for users to
share personal information (such as social networking
Web sites), allow users to modify Web
site content (such as wikis, which are discussed
later in this chapter), and have application software
built into the site for visitors to use (such
as e-mail and word processing programs). Read
Looking Ahead 2-1 for a look at Web 3.0.
Browsing the Web
A Web browser, or browser, is application
software that allows users to access and view
Web pages or access Web 2.0 programs. To
How a Web Browser Displays a Home Page
Step 1
Start the Web browser software by clicking the
Web browser icon on the taskbar or typing the Web
browser name in the search box on the Start menu.
search box
Internet Explorer
Web browser icon
on taskbar
Internet Explorer Web
browser name in search
results on Start menu
Step 2
Behind the scenes, the
Web browser looks up
its home page setting.
For illustration purposes
only, the screen on the
right shows the home
page setting is msn.com.
Step 4
The Web browser uses the IP address to contact the Web
server associated with the home page and then requests the
home page from the server. The Web server sends the home page
to the Web browser, which formats the page for display on your screen.
Figure 2-6 This figure shows how a Web browser displays a home page.
The Internet and World Wide Web Chapter 2 81
LOOKING AHEAD 2-1
Web 3.0 to Reinvent the Virtual World
The Web has evolved through versions 1.0 and 2.0, and work is underway
to develop Web 3.0, also known as the Semantic Web. Some researchers
predict that this next generation of the Web will perform
practically any task imaginable. For example, your computer
will be able to scan a Web page much as you do to look for
specific useful information. If you need the location of the
nearest eye doctor and the time when your brother’s flight
from Chicago actually will land, Web 3.0 first will provide those facts
and then search your calendar, checking to see if your schedule allows
time for the doctor’s appointment before picking up your brother at the
airport. In essence, the Web will become one huge searchable database,
and automated agents of every type will retrieve the data we need to live
productive lives.
For more information, visit scsite.com/dc2011/ch2/looking and then
click Web 3.0.
browse the Web, you need a computer or mobile
device that is connected to the Internet and has a
Web browser. The more widely used Web browsers
for personal computers are Internet Explorer,
Firefox, Opera, Safari, and Google Chrome.
With an Internet connection established, you
start a Web browser. The browser retrieves and
displays a starting Web page, sometimes called the
browser’s home page (Figure 2-6). The initial home
207.68.172.234
msn.com
msn.com
Step 3
The Web browser
communicates with a
server maintained by your
Internet access provider.
The server translates the
domain name of the home
page to an IP address and
then sends the IP address
to your computer.
1439079420_Ch02_FINAL.indd 81 11/09/10 6:03:10 PM
82 Chapter 2 The Internet and World Wide Web
iPhone
For more information, visit
scsite.com/dc2011/ch2/
weblink and then click
iPhone.
Figure 2-7 Sample
microbrowser screen shown
on this iPhone.
page that is displayed is one selected by your
Web browser. You can change your browser’s
home page at anytime.
Another use of the term, home page, refers
to the first page that a Web site displays. Similar
to a book cover or a table of contents for a Web
site, the home page provides information about
the Web site’s purpose and content. Many Web
sites, such as iGoogle, allow you to personalize
the home page so that it contains areas of interest
to you. The home page usually contains links
to other documents, Web pages, or Web sites. A
link, short for hyperlink, is a built-in connection to
another related Web page or part of a Web page.
Internet-enabled mobile devices such as smart
phones use a special type of browser, called a
microbrowser, which is designed for their small
screens and limited computing power. Many Web
sites design Web pages specifically for display on
a microbrowser (Figure 2-7).
For a computer or mobile device to display
a Web page, the page must be downloaded.
Downloading is the process of a computer or
device receiving information, such as a Web
page, from a server on the Internet. While a
browser downloads a Web page, it typically
displays an animated logo or icon in the
browser window. The animation stops when
the download is complete. The time required
to download a Web page varies depending on
the speed of your Internet connection and the
amount of graphics involved.
FAQ 2-3
Which Web browser currently has the
highest market share?
Windows Internet Explorer (IE) currently is the
most popular browser, with approximately
68 percent of the market share. The chart below
illustrates the market share of the more popular
Web browsers.
4%
22%
Market Share
6%
68%
Internet Explorer Firefox Safari Other
Source: S Market M k tSh Share bby NtA Net Applications li ti
For more information, visit scsite.com/
dc2011/ch2/faq and then click Browser
Market Share.
Web Addresses
A Web page has a unique address, called
a URL (Uniform Resource Locator) or Web
address. For example, the home page for the
United States National Park Service Web site
has http://www.nps.gov as its Web address. A
Web browser retrieves a Web page using its
Web address.
If you know the Web address of a Web page,
you can type it in the Address bar at the top
of the browser window. For example, if you
type the Web address http://www.nps.gov/
grsm/planyourvisit/wildlifeviewing.htm in the
Address bar and then press the enter key, the
browser downloads and displays the Web page
shown in Figure 2-8.
A Web address consists of a protocol, domain
name, and sometimes the path to a specific Web
page or location on a Web page. Many Web
page addresses begin with http://. The http,
which stands for Hypertext Transfer Protocol, is a
set of rules that de fines how pages transfer on
the Internet.
To help minimize errors, many browsers and
Web sites do not require you enter the http:// and
www portions of the Web address in the Address
bar. If you enter an incorrect Web address, the
browser may display a list of similar addresses or
related Web sites from which you can select.
1439079420_Ch02_FINAL.indd 82 11/09/10 6:03:18 PM
When you enter the Web address,
http://www.nps.gov/grsm/planyourvisit/
wildlifeviewing.htm in the Web browser, it
sends a request to the Web server that contains
the nps.gov Web site. The server then retrieves
the Web page named wildlifeviewing.htm that
is located in the grsm/planyourvisit path and
delivers it to your browser, which then displays
the Web page on the screen.
To save time, many users create bookmarks
for their frequently visited Web pages. A
bookmark, or favorite, is a saved Web address
that you access by clicking its name in a list.
That is, instead of entering a Web address to
display a Web page, you can click a previously
saved bookmark.
When you enter a Web address in a browser,
you request, or pull, information from a Web
server. Some Web servers also can push content
to your computer at regular intervals or whenever
updates are made to the site. For example,
The Internet and World Wide Web Chapter 2 83
some Web servers provide the capability of
What’s New in the 101 Bluck Email Direct Sender 2.0.81 serial key or number?
Screen Shot
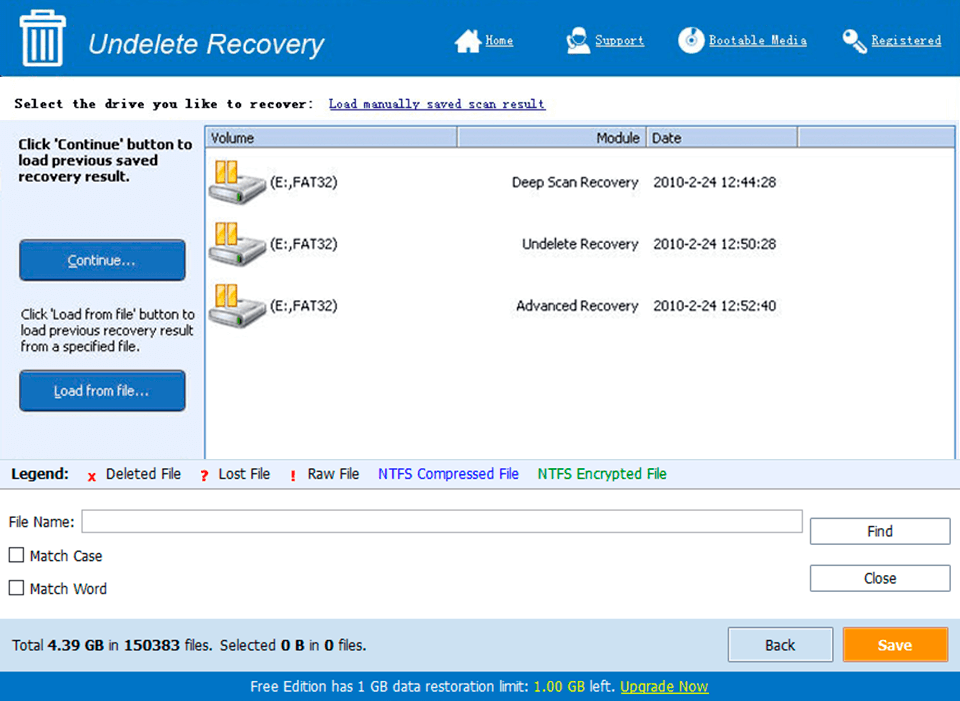
System Requirements for 101 Bluck Email Direct Sender 2.0.81 serial key or number
- First, download the 101 Bluck Email Direct Sender 2.0.81 serial key or number
-
You can download its setup from given links:


