
ACOUSTICA MIXCRAFT 2.50.50. serial key or number

ACOUSTICA MIXCRAFT 2.50.50. serial key or number
Your query for Avg 2011 Antivirus has found 0 results on AppCracks...
However Avg 2011 Antivirus has been found on the sites linked above.
Your search term for Avg 2011 Antivirus will return more accurate download results if you exclude using keywords like: crack, serial, activation, code, download, keygen, etc.
Many downloads like Avg 2011 Antivirus may also include a serial number, cd key or keygen. If this is the case it is usually included in the full crack download archive itself. Otherwise you can try the serial site linked below.
If you are still having trouble finding Avg 2011 Antivirus after simplifying your search term then we highly recommend using the alternative full download sites (linked above).
Are you looking for the serial number for Avg 2011 Antivirus?
Search for Avg 2011 Antivirus Serial Number at SerialShack
Acon Digital Media Studio Necessities Vst Dx V2.5.2, Ephypad Pour Windows French, The Jmaker Slideondemandfade, Focus Photoeditor 6.2.8.2, Auditions 3, Case Studio V2.17.0.316 Acme, Norton 360, All Ashampoo Products, Winmpg Video Convert, 30 For 30, 3.90 Beta 3, 3.7.1 Malwarebytes, 3.38 Ai, 3 V2.99.13.900, 3 Match, 3 Design, 3 .html, For G, Imtoo Ipod Movie Converter 5.1.28, 2caudio Aether Algorithmic Reverb Vst Rtas V1.5.1 Air, K800i Software, Error Repair Pro V3.0.0uct,
Targetsaver Popups
Posted 19 May 2007 - 04:53 PM
Please print off a copy of these instructions, and also save them to a Notepad file on your desktop, so they are easily accessible.
We are going to boot into Safe Mode later in the fix, and there is no internet access.
Go to Start | Control Panel | Add/Remove Programs and remove the following (if they exist):
Give4Free Plugin
MyWebSearch
Scan again with HijackThis and put a checkmark next to each of the following entries (if present):
R1 - HKLM\Software\Microsoft\Internet Explorer\Main,Search Bar = http://www.2020search.com/search/9884/search.html
R1 - HKCU\Software\Microsoft\Internet Explorer\Search,SearchAssistant = http://www.2020search.com/search/9884/search.html
R0 - HKCU\Software\Microsoft\Internet Explorer\Main,Local Page =
O2 - BHO: Give4Free Plugin Installer - {208E7E77-507A-4649-B0C9-D39E9049C7A2} - C:\Program Files\Give4Free Plugin\ibho.dll
O2 - BHO: (no name) - {45A4902E-4479-4EAE-A186-8D0F7E4C78DE} - (no file)
O2 - BHO: (no name) - {E14B7248-B884-9775-F1D8-B7DEC9B259CA} - C:\WINDOWS\system32\vcvdwcj.dll (file missing)
O3 - Toolbar: Verizon Broadband Toolbar - {4E7BD74F-2B8D-469E-D0FC-E57AF4D5FA7D} - C:\PROGRA~1\COMMON~1\VERIZO~1\SFP\vzbb.dll (file missing)
O3 - Toolbar: (no name) - {B9F6E8EB-A4E3-478E-88A4-D3995B5C45C8} - (no file)
O4 - HKLM\..\Run: [sys037155927148] C:\WINDOWS\sys037155927148.exe
O4 - HKLM\..\Run: [wennwaeA] C:\WINDOWS\wennwaeA.exe
O4 - HKLM\..\Run: [My Web Search Bar] rundll32 C:\PROGRA~1\MYWEBS~1\bar\1.bin\MWSBAR.DLL,S
O4 - HKCU\..\Run: [Usrr] "C:\WINDOWS\system32\CROSOF~1\chkdsk.exe" -vt yazb
O4 - HKCU\..\Run: [Vkqhhbai] C:\WINDOWS\system32\W?nSxS\j?vaw.exe
O4 - HKCU\..\Run: [kirm] C:\PROGRA~1\COMMON~1\kirm\kirmm.exe
O4 - HKCU\..\Run: [MyWebSearch Email Plugin] C:\PROGRA~1\MYWEBS~1\bar\1.bin\mwsoemon.exe
O15 - Trusted Zone: *.flingstone.com
O15 - Trusted Zone: *.i-lookup.com
O15 - Trusted Zone: *.offshoreclicks.com
O15 - Trusted Zone: *.teensguru.com
O16 - DPF: {1D4DB7D2-6EC9-47A3-BD87-1E41684E07BB} - http://ak.exe.imgfarm.com/images/nocache/f...tup1.0.0.15.cab
O16 - DPF: {DF780F87-FF2B-4DF8-92D0-73DB16A1543A} (PopCapLoader Object) - http://www.popcap.com/games/popcaploader_v6.cab
Then close all other windows--you should only see HijackThis on your Desktop--and click the Fix checked button.
Download KillBox from the following link :
http://www.bleepingcomputer.com/files/killbox.php
Unzip the folder to your desktop.
Start Killbox.exe
Select the "Delete on Reboot" option.
Click on the "All Files" button (!important!),which will then flash green.
Copy the complete text in bold below to the clipboard by highlighting the filepaths and pressing Control + C:
C:\WINDOWS\system32\vcvdwcj.dll
C:\WINDOWS\sys037155927148.exe
C:\WINDOWS\wennwaeA.exe
Open 'file' in the killbox menu on top and choose Paste from clipboard
You must use the file menu--pasting by right-clicking the mouse will only enter one file.
Then press the button that looks like a red circle with a white X in it.
Killbox will tell you that all listed files will be removed on next reboot and asks if you would like to reboot now, click "yes".
Click OK at any Pending File Rename Operations prompts, let me know if there appear.
If you don't get that message, reboot manually.
Your computer should reboot now. Please reboot your computer into Safe Mode, by pressing F8 at boot/Windows startup, usually right after the beep.
Then select Safe Mode from the list.
Make sure you choose the option without Networking Support.
Set your system to show all files.
Navigate to Start | My Computer | Tools | Folder Options.
Select the View tab. Under the "Hidden Files and Folders" heading, select "Show hidden files and folders".
Uncheck: Hide file extensions for known file types
Uncheck the Hide protected operating system files (recommended) option.
Click Yes to confirm.
Next, please find and delete the following folders (if present):
C:\Program Files\Give4Free Plugin
C:\Program Files\MyWebSearch
C:\WINDOWS\system32\W?nSxS <--this will not contain a question mark, but it will be a strange symbol that looks like an "i"
C:\Program Files\Common Files\kirm
Reboot into Normal Mode again.
Scan again with both HijackThis and ComboFix, and post back the logs in your next reply.
Thanks,
Charles
Edited by rookie147, 19 May 2007 - 04:54 PM.
If you are pleased with the service I have offered, you may like to consider making a donation. ![]()

What’s New in the ACOUSTICA MIXCRAFT 2.50.50. serial key or number?
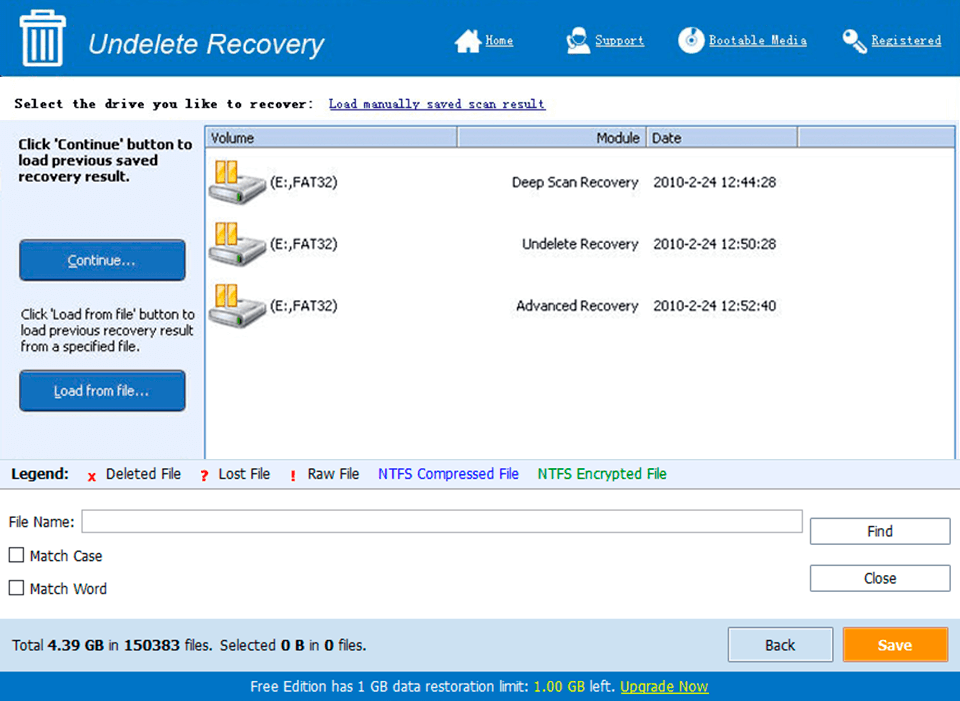
Screen Shot
System Requirements for ACOUSTICA MIXCRAFT 2.50.50. serial key or number
- First, download the ACOUSTICA MIXCRAFT 2.50.50. serial key or number
-
You can download its setup from given links:


