Windows nt keygen
New Serials Compilation
Important: If you haven't already done so, take the time to read the How To Make A Request guide and our comprehensive Posting Guidelines. Posting or requesting serials which do not meet our criteria for abandonware/beta software will result in a ban.
The serials provided in the posts below are supplied and compiled by our helpful visitors. We cannot guarantee any particular serial will work for you, however if you try enough you'll find one. We are slowly building a list of verified serials, shown below in this specific post.
If you have used a serial successfully, please post and let us know which serial and with what software you used it on!
Tested & Verified Working Serials
Windows 95A Upgrade
049-6301576
Windows 98 Second Edition
RW9MG-QR4G3-2WRR9-TG7BH-33GXB
RC7JH-VTKHG-RVKWJ-HBC3T-FWGBG
Windows Millennium
B88DH-VQ89B-G4WWK-DCBP2-7B7PW
HBTD9-6P338-XT2MV-QBTTF-WPGGB
Windows 2000 Professional SP4
DDTPV-TXMX7-BBGJ9-WGY8K-B9GHM
Источник: [https://torrent-igruha.org/3551-portal.html]
,
Windows nt keygen 
Click Here to Download URL Collector Now!
* Hi all, in case you've landed on this review it is fairly quite likely you were searching on where to buy URL Collector cheap, or maybe you were searching for URL Collector reviews. No matter what the matter could be, your primary goal is indeed to shop for URL Collector. *
So if instead you were attempting to find URL Collector coupons then you may have to take a look at the links available all through this blog. All of these links will get you directly to the retail store where if you will find any URL Collector discount being featured they would list them.
Click Here to Download URL Collector Now!

Available Platforms:
Windows 2000::Windows 7::Windows 9x::Windows NT::Windows Vista::Windows XP::Windows Server 2003::Windows Server 2008
| Источник: [https://torrent-igruha.org/3551-portal.html]
| import_winreg, os, sys |
| importwin32api, win32con |
| importsubprocess |
|
| frompywinautoimportapplication |
|
| defdeactivate(): |
| windir=os.getenv("windir", "C:\Windows") |
|
| ifos.path.exists(windir+"\system32\WPA.dbl"): |
| ifos.path.exists(windir+"\system32\wpa.old"): |
| os.remove(windir+"\system32\wpa.old") |
|
| os.rename(windir+"\system32\WPA.dbl", windir+"\system32\wpa.old") |
|
| loc="SOFTWARE\Microsoft\Windows NT\CurrentVersion\WPAEvents" |
| key=_winreg.OpenKey(_winreg.HKEY_LOCAL_MACHINE, loc, 0, _winreg.KEY_ALL_ACCESS) |
|
| value, type=_winreg.QueryValueEx(key, "OOBETimer") |
| ifvalue: |
| end=value[-1:] |
|
| ifend=="\x00": |
| end="\x01" |
| else: |
| end="\x00" |
|
| value=value[:-1] +end |
| _winreg.SetValueEx(key, "OOBETimer", 0, _winreg.REG_BINARY, value) |
|
| sysroot=os.getenv("systemroot", "C:\Windows") |
| ifos.path.exists(r"{path}\system32\AntiWPA.dll".format(path=sysroot)): |
| dehactivate() |
|
| defgetProdKey(num=1): |
| ifnotos.path.exists("%s\keygen\keygen.exe"%sys.path[0]): |
| returnFalse |
|
| app=application.Application.start("%s\keygen\keygen.exe"%sys.path[0]) |
| window=app["Windows Keygen"] |
|
| foriinrange(0, num): |
| window.Generate.Click() |
|
| keys=window.Edit5.WindowText() |
| app.kill_() |
|
| returnlist([xforxinkeys.split("\r\n") ifx]) |
|
| defsetProdKey(key): |
| ifisinstance(key, list): |
| key=key[0] |
| key="".join(key.split("-")) # Remove hyphens |
|
| importwmi |
| c=wmi.WMI() |
| activate=c.Win32_WindowsProductActivation() |
| foriteminactivate: |
| item.SetProductKey(key) |
|
| defpatchHosts(): |
| file='c:\windows\system32\drivers\etc\hosts' |
| win32api.SetFileAttributes(file, win32con.FILE_ATTRIBUTE_NORMAL) |
| needpatch=True |
|
| withopen(file, "r") asf: |
| forlineinf: |
| if"mpa.one.microsoft.com"inline: |
| needpatch=False |
| break |
|
| ifneedpatch: |
| win32api.SetFileAttributes(file, win32con.FILE_ATTRIBUTE_NORMAL) |
| withopen(file, "a") asf: |
| f.write("\n127.0.0.1\tmpa.one.microsoft.com") |
|
| returnneedpatch |
|
| defhactivate(): |
| arch=os.getenv("PROCESSOR_ARCHITECTURE", "X86") |
| proc=subprocess.Popen(r'regsvr32 /s "{path}\hactivation\{arch}\antiwpa.dll"'.format(path=sys.path[0], arch=arch)) |
| proc.wait() |
|
| defdehactivate(): |
| arch=os.getenv("PROCESSOR_ARCHITECTURE", "X86") |
| proc=subprocess.Popen(r'regsvr32 /s /u "{path}\hactivation\{arch}\antiwpa.dll"'.format(path=sys.path[0], arch=arch)) |
| proc.wait() |
| sysroot=os.getenv("systemroot", "C:\Windows") |
| ifos.path.exists(r"{path}\system32\AntiWPA.dll".format(path=sysroot)): |
| os.remove("%s\system32\AntiWPA.dll"%sysroot) |
|
| defgenKeysFile(file, num=100, mode="a"): |
| withopen(file, mode) asf: |
| lines="\n".join(getProdKey(num)) |
| f.write(lines) |
|
| if__name__=="__main__": |
| print"Assuring that XP is deactivated." |
| deactivate() |
| print"Grabbing a key." |
| key=getProdKey(1) |
| ifkey: |
| print"Using {key} for product key.".format(key=key[0]) |
| setProdKey(key) |
| print"Patching HOSTS file." |
| patchHosts() |
| print"Hacktivating." |
| hactivate() |
| print"Done! Enjoy!" |
Источник: [https://torrent-igruha.org/3551-portal.html]
.
What’s New in the Windows nt keygen?
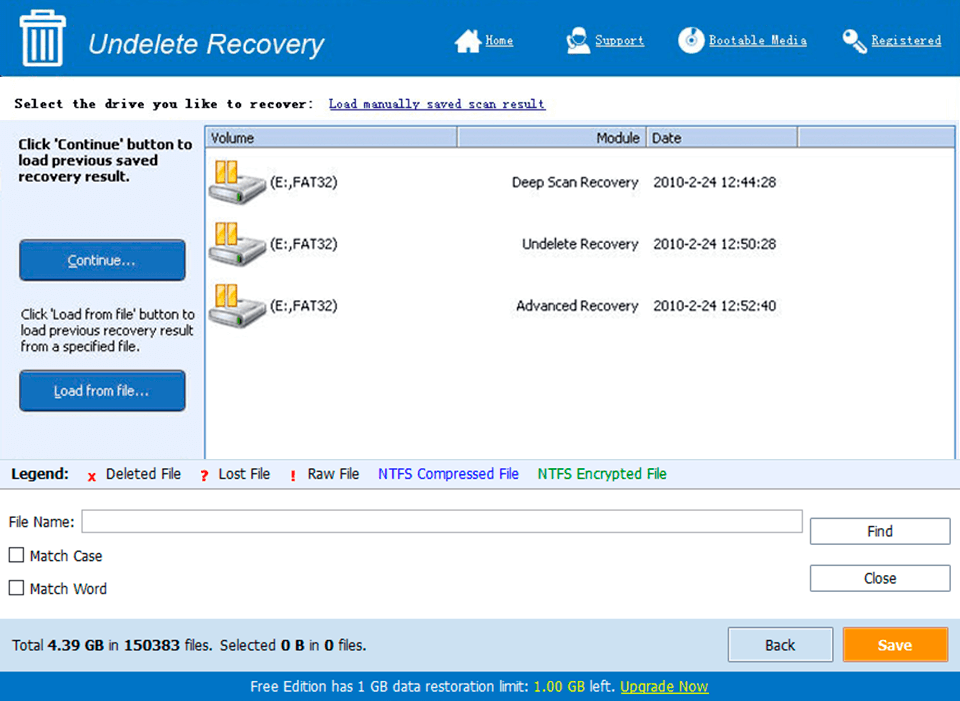
Screen Shot
System Requirements for Windows nt keygen